Additional Topologies
,This section builds on the guidance suggested by Microsoft and offers some additional sample topologies. These have not been performance tested by Microsoft and are only a suggested starting point. Each topology should be thoroughly tested for performance by an organization before being placed into production.
Small Business
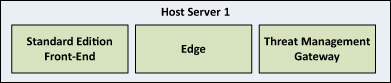
Small businesses looking to take advantage of virtualizing Lync Server 2010 on-premises will likely be looking to leverage the core feature set with remote access and possibly telephony integration. The priority in this configuration is to deploy as many features as possible with the least amount of hardware. High availability and failover are not requirements in this scenario, but the downside here is that a host or guest VM failure causes a complete loss in service. The small business topology is shown in Figure 25.6.
Figure 25.6 Sample Small Business Virtual Topology
A single virtual host can be used with the following hardware configuration:
• 2.26 GHz or higher CPU with 12 processor cores
• 48 GB RAM
• 500 GB SAS Disk (RAID 1+0)
• Six network adapters
Three virtual machines will be created: one Standard Edition Front-End Server with the Mediation Server collocated, one Edge Server, and one reverse proxy server running Microsoft Forefront Threat Management Gateway.
The Standard Edition Front-End Server would have the following configuration:
• Four virtual CPUs
• 16 GB RAM
• One network adapter
The Edge Server would have the following configuration:
• Four virtual CPUs
• 16 GB RAM
• Two network adapters
The Threat Management Gateway would have the following configuration:
• Two virtual CPUs
• 4 GB RAM
• Two network adapters
Medium-Sized Business
For those businesses that require a higher level of availability in Lync deployments, it becomes necessary to use more host server hardware and create additional virtual machines. This sample builds on the deployment for a small business, but provides redundancy at each role while adding monitoring and archiving abilities. Shared storage through an iSCSI SAN is a requirement for providing database clustering capabilities. This is only an example and can be modified to meet the needs of a business. The sample medium-sized business topology is depicted in Figure 25.7.
Figure 25.7 Sample Medium-Sized Business Virtual Topology
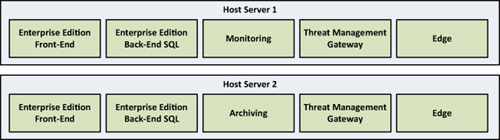
Two virtual hosts can be used with the following hardware configuration:
• 2.26 GHz or higher CPU with 16 processor cores
• 72 GB RAM
• 500 GB SAS Disk (RAID 1+0)
• 10 network adapters
Each host will run one virtual machine with the Enterprise Edition Front-End Server role in the following configuration:
• Four virtual CPUs
• 16 GB RAM
• One network adapter
Each host will run one virtual machine with the Back-End Server role in the following configuration. The two Back-End Servers can use SQL Server Failover Clustering to provide high-availability across hosts:
• Four virtual CPUs
• 16 GB RAM
• Four network adapters
Note
The additional network adapters here are for SQL Server Failover Clustering. In addition to the regular adapter, a private heartbeat network should be used. Also, because SQL clustering requires a shared disk, network adapters for iSCSI access to a SAN are required. Two are used here to allow iSCSI multipathing for redundancy.
Each host will run one virtual machine with the Edge Server role in the following configuration:
• Four virtual CPUs
• 16 GB RAM
• Two network adapters
Each host will run one virtual machine with Microsoft Forefront Threat Management Gateway in the following configuration:
• Two virtual CPUs
• 4 GB RAM
• Two network adapters
One host will run a Monitoring Server virtual machine and the other will run the Archiving Server virtual machine. Both will use the following configuration:
• Four virtual CPUs
• 16 GB RAM
• One network adapter
