You might need to connect JIRA to other services such as LDAP, mail servers, and other websites. Often, these services make use of SSL. In such cases, the connection will fail, and you will see the following errors in your JIRA log file:
javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
For this recipe, we will be using the Java keytool utility, so make sure you have the following configuration set up:
- Obtain the SSL certificate from the target system.
- Ensure that the
JAVA_HOMEenvironment variable is set properly. - Make sure you know which JDK/JRE JIRA is using. You can find this information from the System Info page, where you need to look for the
java.homeproperty. - Make sure your JRE/JDK's
bindirectory is added to your PATH environment variable, and thekeytoolcommand will output its usage. - Obtain the password for the Java trust store used by JIRA.
In this recipe, let's assume we want to connect JIRA to an LDAP server that is running on SSL. Perform the following steps to make it a trusted site inside JIRA:
- Open up a command prompt and go to the directory where the certificate file resides.
- Import the certificate into the trust store by running the
keytool –import –alias tomcat –file file.cer JAVA_HOMEjrelibsecuritycacertscommand, wherefile.ceris the certificate file. - Restart JIRA to apply the changes.
When JIRA attempts to connect to an SSL-protected service, it will first determine whether the target service can be trusted by checking if the service's certificate is present in what is called the trust store. If the certificate is not present, the connection will fail.
The trust store is typically a KeyStore called cacerts and is located in the $JAVA_HOME/lib/security directory on the server.
We used the keytool utility to import the certificate to our local trust store, so the target service will be registered as a trusted service and allows JIRA to successfully connect to it.
Manually downloading the certificate and running the keytool command every time can be a hassle. To make life easier for you, there is a free add-on called SSL for JIRA from Atlassian Labs that can help you automate some of the steps. You can download this add-on from the following link:
https://marketplace.atlassian.com/plugins/com.atlassian.jira.plugin.jirasslplugin
Perform the following steps to use the SSL for JIRA add-on:
- Log in to JIRA as a JIRA administrator.
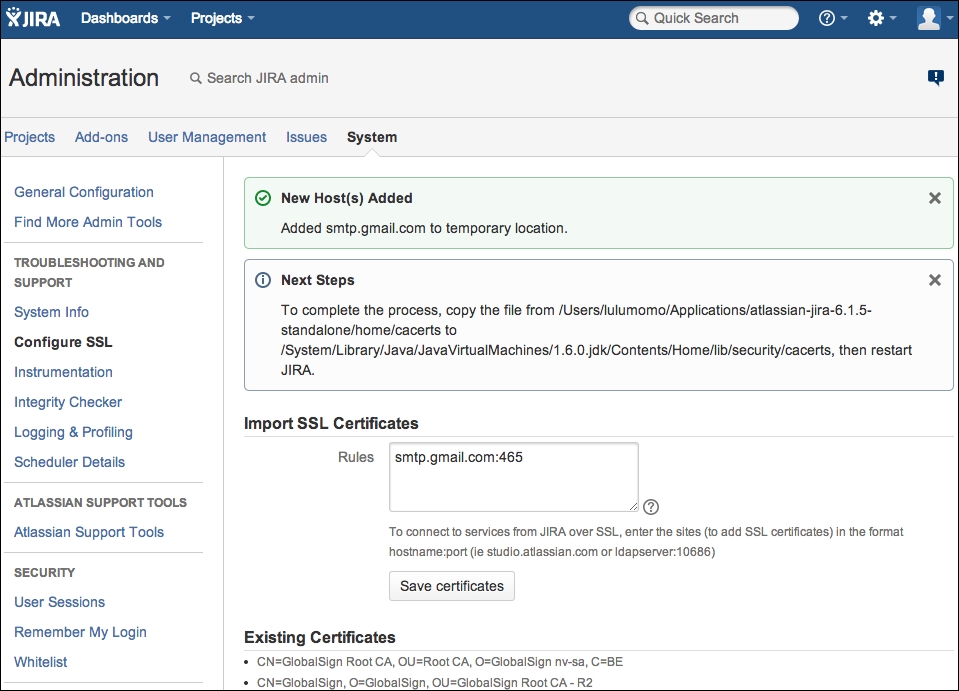
- Navigate to Administration | System | Configure SSL.
- Type in the target system's address in the Rules textbox in the
host:portformat (for example, smtp.gmail.com:465). - Click on Save certificates as shown in the following screenshot.
- Follow the instruction on the screen to copy over the
cacertsfile to the target location. - Restart JIRA to apply the changes.