To use Ettercap in order to carry out DNS spoofing, we need to give Ettercap some additional privileges. Follow these steps:
- Use a text editor and edit the
/etc/ettercap/etter.conffile.#nano /etc/ettercap/etter.conf
- Change the
gidanduidthat Ettercap uses to0. This will allow the process to run as root and manipulating interface or operating settings to accomplish our goals will not be an issue. - Edit the configuration for
dns_spoofplugin for Ettercap. Again, use a text editor and edit the file at/etc/ettercap/etter.dns. - In the redirection section of the file titled microsoft sucks ;), you will be adding in the domain names you would like to redirect to your local server. In this example, we will be adding the
gateway.localDNS name. You can also add other hostnames, domain names, or wildcard domain names such as the given*.microsoft.comexample. When the user attempts to access anything at the domain namemicrosoft.com, they will be redirected to the IP address that is specified following theAor host record.This example uses:
gateway.loca l A 192.168.0.147
- Save the file and exit your text editor.

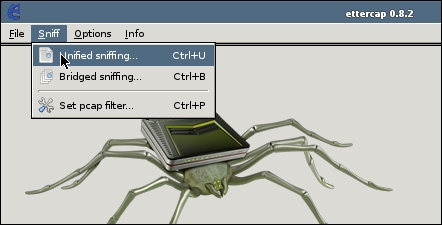
- With the configuration changes made, open up Ettercap using the command ettercap
–G; the G flag specifies to use the GTK interface.ettercap –G - Enter Unified Sniffing mode by choosing Sniff | Unified Sniffing… from the menu followed by the interface you are using to connect to the wireless network, commonly wlan0.
- The menu items will change and you will select Plugins | Manage the Plugins.

- Activate the
dns_spoofplugin by double-clicking thedns_spoofline. Anxwill appear next to the plugin name and the status box in the Ettercap status window will indicate that it is Activating the dns_spoof plugin…, as shown in the following screenshot:
- Repeat the preceding process described to initiate the ARP poisoning attack.
To recap, you will be selecting the two hosts you want to sit in between, typically the router and the victim. In this case, we will target the administrator's desktop in the hope that they will try to access the administrative web page using the DNS name that we have spoofed and then fall victim to our fake administrative interface for the router.

Once ARP poisoning is in place, when the administrator brings up their web browser and attempts to access gateway.local in their web browser, they will instead be presented with the administrative interface that we cloned and is running locally in S.E.T. The reason for this is instead of gateway.local resolving via the network DNS server to 192.168.0.1, the response will instead be spoofed by Ettercap and will be returned to the client as 192.168.0.147, the IP address of Kali. You will see that this is successful in the Ettercap status window that indicates dns_spoof followed by the hostname that was specified followed by the IP address that was delivered to the client.

When the administrator attempts to enter the username and password for the device, S.E.T. will automatically capture these account credentials and will be displayed on the console.

In this section, we saw how you can combine several tools together to achieve the outcome you are looking for. We were able to use the Social Engineering Toolkit to clone a popular website, network device's administrative interface, or any other web page and host it on our Kali server. This allows us to view the information that is submitted into the web page, which could contain a username and password combination.
After the page was cloned, we set up a DNS spoof in Ettercap. This allowed us to listen for DNS requests and send the client back to the address we wanted them to go to instead of the one that would have been returned by the DNS server.
DNS spoofing is not the only type of name resolution spoofing that is possible on wireless networks. Next, we will look at NBNS and how spoofing this service on a shared medium, such as wireless, can allow you to capture sensitive information from Windows clients in particular.