As discussed in the previous chapter, man-in-the-middle attacks represent a real threat to the confidentiality and integrity of the wireless network and the clients who access it. We saw how traffic can be captured and manipulated between legitimate clients and the resources they are trying to access. We also explored how we can manipulate an existing wireless network to redirect client traffic flows. Another, and potentially more effective, way to see all of a client's wireless traffic is to become the access point they connect to.
In this chapter, we will set up an evil twin access point and, effectively, become the network infrastructure. This access point will act just like the legitimate access point in servicing clients; however, since we are in control of the configuration and the device running the AP services, we are able to capture and manipulate any of the traffic that traverses it. This opens up many new possibilities to us as the attacker when it comes to compromising the client, such as extracting usernames and passwords from the network traffic, presenting the user with spoofed login pages, attacking the client with browser-based exploits, DNS poisoning, and much more. Once our access point is utilized by the connecting clients, it enables the attacker with virtually unlimited access to the data generated by the connecting clients, including traffic that would normally be encrypted. While these types of attacks do not directly compromise the target network, enough information can be gleaned through data collection to lead to privilege escalation or compromising the connecting clients, which can also accelerate our penetration test.
We will discuss different techniques to compromise the target machine and use various tools available to perform man in the middle attacks. Specifically, we will discuss the following topics in this chapter:
- Create an evil twin AP using Hostapd and airbase-ng
- Session hijacking
- Credential harvesting
- Exploiting clients via web-based attacks
In this chapter, we will discuss several techniques that will allow the attacker to position themselves in the flow of traffic, from legitimate connecting clients to the target network. One possible option is to configure an access point that mimics a production access point and contains the same authentication and encryption attributes. The following figure depicts the scenario we are trying to achieve with this type of attack. Essentially, the attacker's device becomes the access point, and the upstream traffic, including the Internet traffic, is forwarded to another interface on the device.

We will discuss how to create virtual access points in Kali Linux using a wireless card. To use a laptop/PC wireless card as an access point, we need Hostapd in Linux. Hostapd enables a virtual access point on a Linux box using the wireless card available to it. It supports all kinds of wireless cards. Occasionally, you may face a challenge where the wireless card you are using does not support all of the Hostapd features. We will also cover some alternative techniques to bring up evil twin access points in other exercises that follow:
- Insert the card you have with you into the Kali machine. To know what mode your cards support, type the following command:
#iw list - Bring up the card that supports the AP mode and assign the IP address
192.168.1.1to the wireless card:#ifconfig wlan1 192.168.1.1 up
- We need to start a
dhcpserver on a virtual access point, so whenever a wireless client associates with us, we deliver a dynamic IP address to the client:#dhcpd –cf labfiles/fakeap-1/hostap/dhcp.conf wlan1
- The following is the content of the DHCP configuration file. Just copy the content, paste it in a file, and use it as a configuration file for the DHCP daemon.

The preceding DHCP configuration assigns the wireless clients the IP address starting from
192.168.1.100to192.168.1.254, with the gateway IP as192.168.1.1, which is the virtual access point's IP: - To forward the traffic from wireless clients to a wired adapter where Internet connectivity is available, you can use the
iptablesforwarding feature. After this configuration, the wireless clients now get an IP address, and they can reach the Internet through our virtual access point. - Create the
iptablesrules to enable packet forwarding on the machine:#sh labfiles/fakeap-1/hostapd/iptables.sh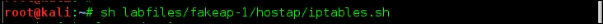
The following screenshot highlights the contents of the
iptablesscript used earlier: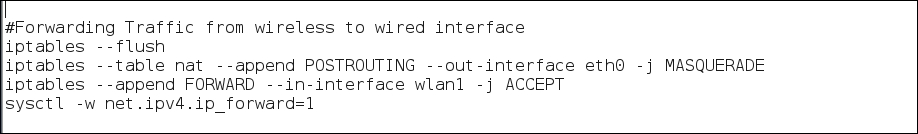
- Create a configuration file for Hostapd based on the encryption technique you will be emulating on the target AP. We will list some examples here for WEP, WPA, and WPA2:
- WEP
- Specify the interface, SSID, Channel, and WEP Key.

- Start
hostapdwith your WEP configuration:#hostapd /etc/hostapd/hostapd-wep.conf -dd
- Specify the interface, SSID, Channel, and WEP Key.
- WPA: To host an access point with WPA encryption use the following Hostapd configuration file.
- WPA2
- WEP
The goal is to minimize any differences between the evil twin AP and the experience they have when connecting to the legitimate AP. Once legitimate clients connect to our fake access point, we can run Wireshark on our interfaces to capture the data flowing from and to wireless clients. Further session hijacking, extracting usernames and passwords from plain text protocols, and modifying the data are all now possible.