Reference Models and Architectures
Information in this chapter:
• Smart Grid cyber security reference model
• Smart Grid cyber security design template
• Generation cyber security reference model (detail)
• Generation cyber security design template (detail)
• NISTIR 7628 guidelines for Smart Grid cyber security
• IEEE 2030-2011 Smart Grid power system, communication technology, and information technology reference diagrams
• SGSC reference architecture for the Smart Grid
• Applying endpoint security controls
Have ever tried to find that diagram you saw in a book and couldn’t remember what it was titled or what it was in? This appendix has been provided as a convenient way to quickly find reference diagrams from this book as well as from other sources, for that very reason.
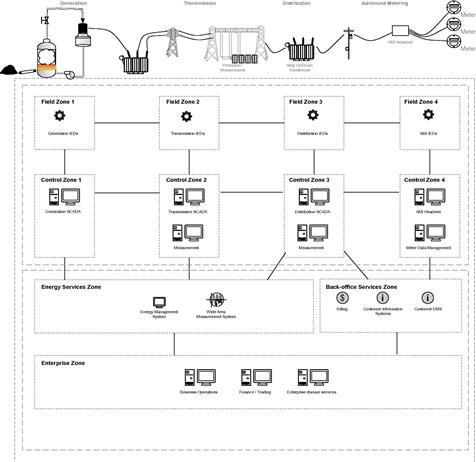
Smart Grid cyber security reference model
A simplified representation of the Smart Grid, to show how different systems in different zones interconnect in order to determine where to implement different cyber security measures. Refer to Chapter 5, “Security Models for SCADA, ICS, and Smart Grid” (see Figure A.1).
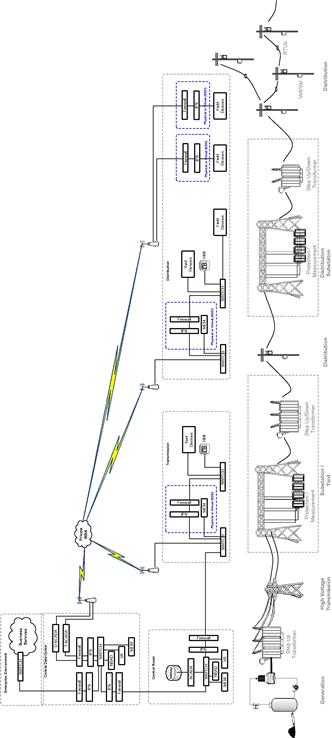
Smart Grid cyber security design template
Extrapolating the more generic security model above to a more accurate and detailed Smart Grid architecture. Refer to Chapter 6, “Protecting the Smart Grid” (see FigureA.2).
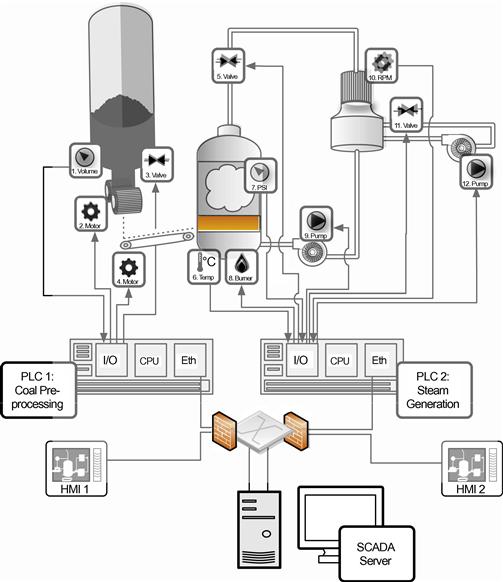
Generation cyber security reference model (detail)
A detailed model of a fossil fuel power generation system was designed to highlight the many dependent components that could be attacked or manipulated by a cyber threat. Refer to Chapter 2, “Smart Grid Network Architecture,” and Chapter 6, “Protecting the Smart Grid” (see Figure A.3).
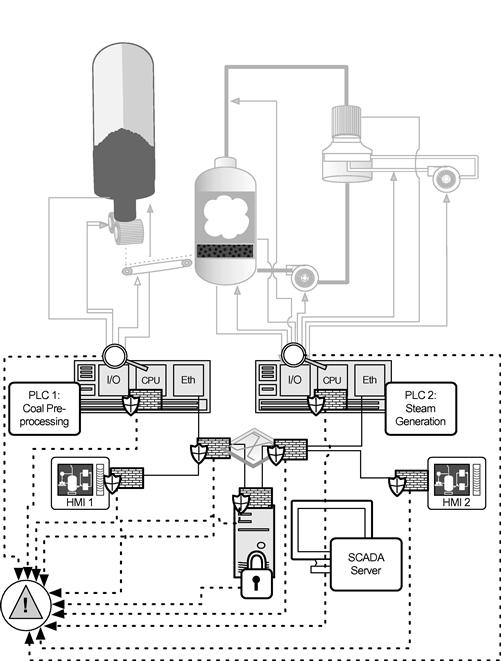
Generation cyber security design template (detail)
Common cyber security countermeasures applied to the above “Generation Cyber Security Reference Model.” Refer to Chapter 6, “Protecting the Smart Grid” (see Figure A.4).
NISTIR 7628 guidelines for Smart Grid cyber security
The NIST representation of the Smart Grid, and the interconnection of its many systems, grouped by actor (Transmission, Distribution, Bulk Generation, Operations, Marketing, Service Provider, and Customer). Refer to the NISTIR 7628 for more information (see Figure A.5).
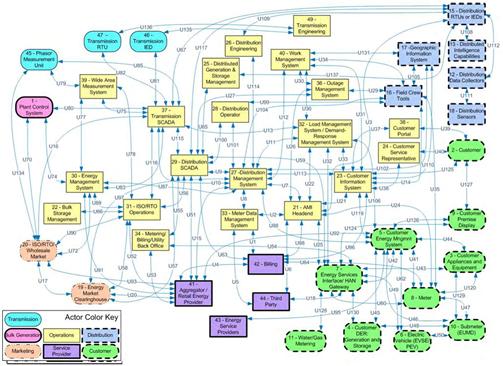
Figure A.5 NIST Smart Grid logical reference model (reprinted from NISTIR 7628 Figure 2.3 as public information).1
SGCG reference architecture for the Smart Grid
The Smart Grids Coordination Group Reference Architecture for the Smart Grid, highlighting the different domains, zones, and interoperability layers of the Smart Grid (see Figure A.6).
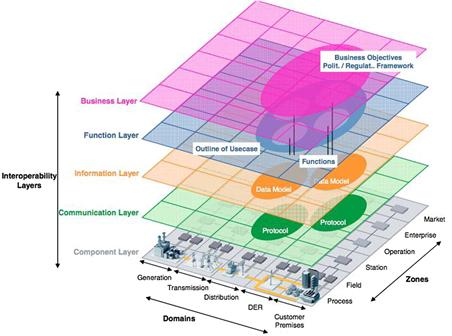
Figure A.6 The SGAM framework with interoperability layers (reprinted with permission from Figure 7 of the SGCG report on reference architecture for the Smart Grid).2
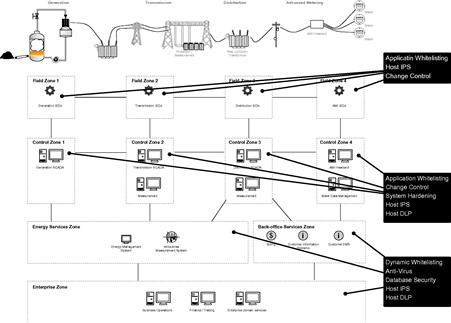
Applying endpoint security controls
Recommended applications of endpoint security (defined in Chapter 6, “Protecting the Smart Grid”), using the Smart Grid reference model (defined in Chapter 5, “Security Models for SCADA, ICS, and Smart Grid”) (see Figure A.7).
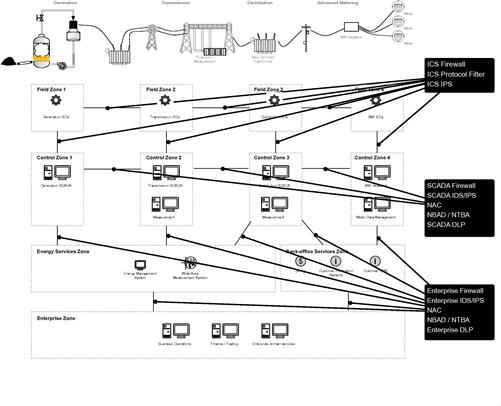
Applying network security controls
Recommended applications of network security (defined in Chapter 6, “Protecting the Smart Grid”), using the Smart Grid reference model (defined in Chapter 5, “Security Models for SCADA, ICS, and Smart Grid”) (see Figure A.8).
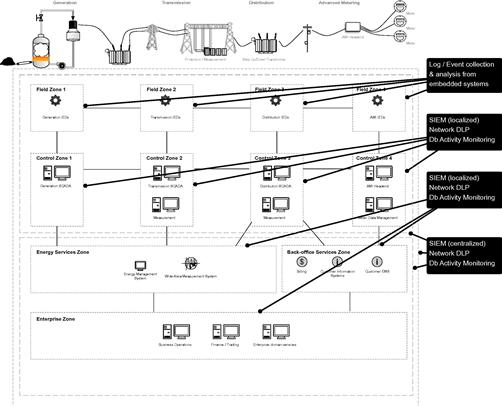
Applying data integrity and protection controls
Recommended applications of data integrity and protection (defined in Chapter 6, “Protecting the Smart Grid”), using the Smart Grid reference model (defined in Chapter 5, “Security Models for SCADA, ICS, and Smart Grid”) (see Figure A.9).
References
1. The Smart Grid Interoperability Panel – Cyber Security Working Group. NISTIR 7628 guidelines for smart grid cyber security: Vol. 1, Smart Grid cyber security strategy, architecture, and high-level requirements. US Department of Commerce, National Institute of Standards and Technologies; August 2010.
2. CEN, CENELEC and ETSI. SGCG report on reference architecture for the Smart Grid external version V2.0. SGSC Reference Architecture Working Group (RAWG); August 2012.