- About This eBook
- Title Page
- Copyright Page
- About the Authors
- About the Technical Reviewers
- Dedications
- Acknowledgments
- Contents at a Glance
- Contents
- Command Syntax Conventions
- Introduction
- Part I: Fundamentals of Network Security
- Chapter 1. Networking Security Concepts
- Chapter 2. Common Security Threats
- Part II: Secure Access
- Chapter 3. Implementing AAA in Cisco IOS
- Chapter 4. Bring Your Own Device (BYOD)
- Part III: Virtual Private Networks (VPN)
- Chapter 5. Fundamentals of VPN Technology and Cryptography
- Chapter 6. Fundamentals of IP Security
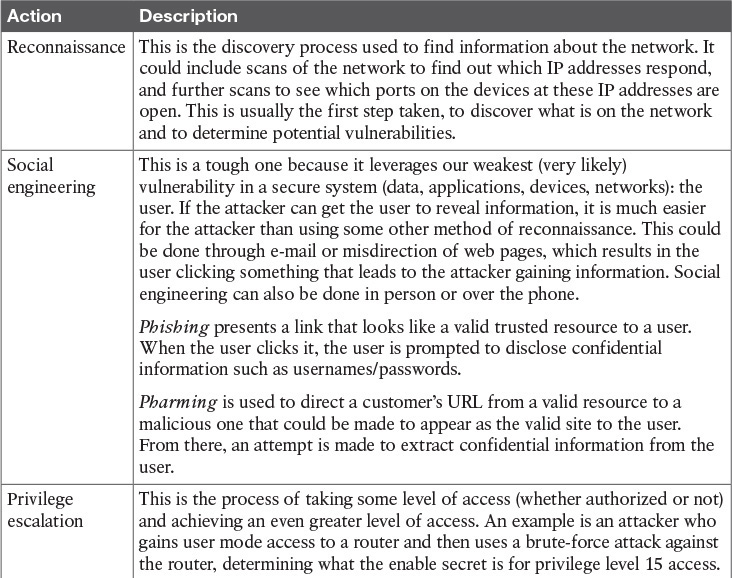
Attack Methods
Most attackers do not want to be discovered and so they use a variety of techniques to remain in the shadows when attempting to compromise a network, as described in Table 1-5.
-
No Comment
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.