Cisco WSA
The Cisco WSA uses cloud-based intelligence from Cisco to help protect the organization before, during, and after an attack. This “lifecycle” is what is referred to as the attack continuum. The cloud-based intelligence includes web (URL) reputation and zero-day threat intelligence from Cisco’s security intelligence and research group named Talos. This threat intelligence helps security professionals to stop threats before they enter the corporate network, while also enabling file reputation and file sandboxing to identify threats during an attack. Retrospective attack analysis allows security administrators to investigate and provide protection after an attack when advanced malware might have evaded other layers of defense.
The Cisco WSA can be deployed in explicit proxy mode or as a transparent proxy using the Web Cache Communication Protocol (WCCP). WCCP is a protocol originally developed by Cisco, but several other vendors have integrated it in their products to allow clustering and transparent proxy deployments on networks using Cisco infrastructure devices (routers, switches, firewalls, and so on).
Figure 18-4 illustrates a Cisco WSA deployed as an explicit proxy.
The following are the steps illustrated in Figure 18-4:
1. An internal user makes an HTTP request to an external website. The client browser is configured to send the request to the Cisco WSA.
2. The Cisco WSA connects to the website on behalf of the internal user.
3. The firewall (Cisco ASA) is configured to only allow outbound web traffic from the Cisco WSA, and it forwards the traffic to the web server.
Figure 18-5 shows a Cisco WSA deployed as a transparent proxy.
The following are the steps illustrated in Figure 18-5:
1. An internal user makes an HTTP request to an external website.
2. The internal router (R1) redirects the web request to the Cisco WSA using WCCP.
3. The Cisco WSA connects to the website on behalf of the internal user.
4. Also in this example, the firewall (Cisco ASA) is configured to only allow outbound web traffic from the WSA. The web traffic is sent to the Internet web server.
Figure 18-6 demonstrates how the WCCP registration works. The Cisco WSA is the WCCP client, and the Cisco router is the WCCP server.
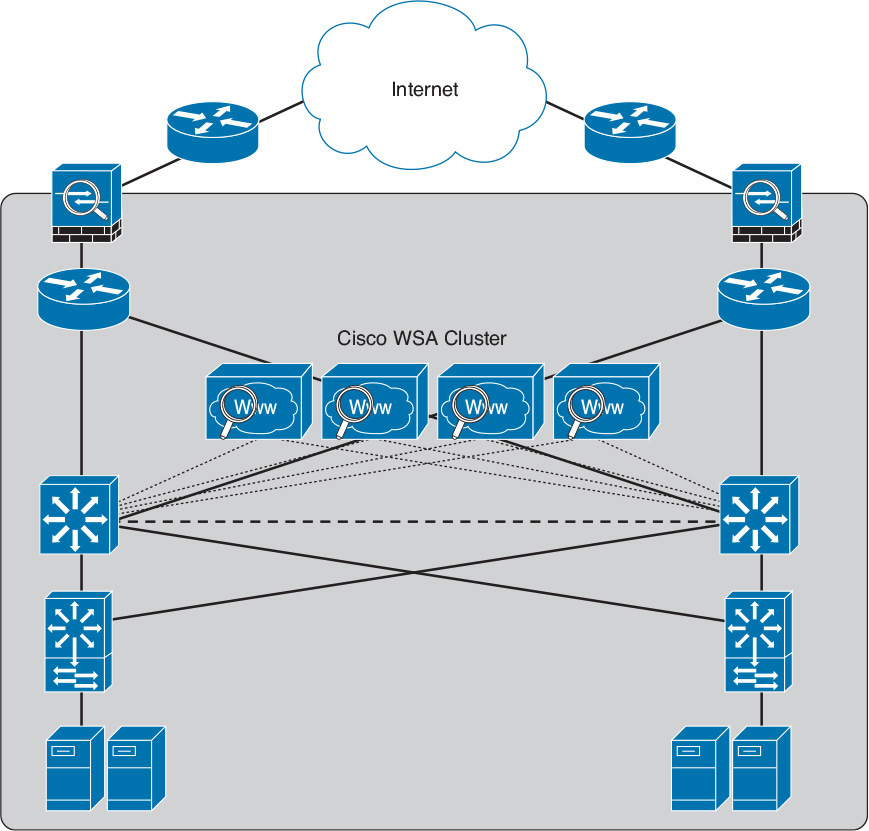
During the WCCP registration process, the WCCP client sends a registration announcement (“Here I am”) every 10 seconds. The WCCP server (the Cisco router in this example) accepts the registration request and acknowledges it with an “I See You” WCCP message. The WCCP server waits 30 seconds before it declares the client as “inactive” (engine failed). WCCP can be used in large-scale environments. Figure 18-7 shows a cluster of Cisco WSAs, where internal Layer 3 switches redirect web traffic to the cluster.
The Cisco WSA comes in different models. The following are the different Cisco WSA models:
![]() It is a high-performance WSA designed for large organizations with 6000 to 12,000 users.
It is a high-performance WSA designed for large organizations with 6000 to 12,000 users.
![]() A 2 rack-unit (RU) appliance with 16 (2 octa core) CPUs, 32 GB of memory, and 4.8 TB of disk space.
A 2 rack-unit (RU) appliance with 16 (2 octa core) CPUs, 32 GB of memory, and 4.8 TB of disk space.
![]() Cisco WSA S670
Cisco WSA S670
![]() A high-performance WSA designed for large organizations with 6000 to 12,000 users
A high-performance WSA designed for large organizations with 6000 to 12,000 users
![]() A 2 RU appliance with 8 (2 octa core) CPUs, 8 GB of memory, and 2.7 TB of disk space.
A 2 RU appliance with 8 (2 octa core) CPUs, 8 GB of memory, and 2.7 TB of disk space.
![]() Cisco WSA S380
Cisco WSA S380
![]() Designed for medium-size organizations with 1500 to 6000 users.
Designed for medium-size organizations with 1500 to 6000 users.
![]() A 2 RU appliance with 6 (1 hexa core) CPUs, 16 GB of memory, and 2.4 TB of disk space.
A 2 RU appliance with 6 (1 hexa core) CPUs, 16 GB of memory, and 2.4 TB of disk space.
![]() Cisco WSA S370
Cisco WSA S370
![]() Designed for medium-size organizations with 1500 to 6000 users.
Designed for medium-size organizations with 1500 to 6000 users.
![]() A 2 RU appliance with 4 (1 quad core) CPUs, 4 GB of memory, and 1.8 TB of disk space.
A 2 RU appliance with 4 (1 quad core) CPUs, 4 GB of memory, and 1.8 TB of disk space.
![]() Cisco WSA S170
Cisco WSA S170
![]() Designed for small- to medium-size organizations with up to 1500 users.
Designed for small- to medium-size organizations with up to 1500 users.
![]() A 1 RU appliance with 2 (1 dual core) CPUs, 4 GB of memory, and 500 GB of disk space.
A 1 RU appliance with 2 (1 dual core) CPUs, 4 GB of memory, and 500 GB of disk space.
The Cisco WSA runs Cisco AsyncOS operating system. The Cisco AsyncOS supports numerous features that will help mitigate web-based threats. The following are examples of these features:
![]() Real-time antimalware adaptive scanning: The Cisco WSA can be configured to dynamically select an antimalware scanning engine based on URL reputation, content type, and scanner effectiveness. Adaptive scanning is a feature designed to increase the “catch rate” of malware that is embedded in images, JavaScript, text, and Adobe Flash files. Adaptive scanning is an additional layer of security on top of Cisco WSA Web Reputation Filters that include support for Sophos, Webroot, and McAfee.
Real-time antimalware adaptive scanning: The Cisco WSA can be configured to dynamically select an antimalware scanning engine based on URL reputation, content type, and scanner effectiveness. Adaptive scanning is a feature designed to increase the “catch rate” of malware that is embedded in images, JavaScript, text, and Adobe Flash files. Adaptive scanning is an additional layer of security on top of Cisco WSA Web Reputation Filters that include support for Sophos, Webroot, and McAfee.
![]() Layer 4 traffic monitor: Used to detect and block spyware. It dynamically adds IP addresses of known malware domains to a database of sites to block.
Layer 4 traffic monitor: Used to detect and block spyware. It dynamically adds IP addresses of known malware domains to a database of sites to block.
![]() Third-party DLP integration: Redirects all outbound traffic to a third-party DLP appliance, allowing deep content inspection for regulatory compliance and data exfiltration protection. It enables an administrator to inspect web content by title, metadata, and size and to even prevent users from storing files to cloud services, such as Dropbox, Google Drive, and others.
Third-party DLP integration: Redirects all outbound traffic to a third-party DLP appliance, allowing deep content inspection for regulatory compliance and data exfiltration protection. It enables an administrator to inspect web content by title, metadata, and size and to even prevent users from storing files to cloud services, such as Dropbox, Google Drive, and others.
![]() File reputation: Using threat information from Cisco Talos. This file reputation threat intelligence is updated every 3 to 5 minutes.
File reputation: Using threat information from Cisco Talos. This file reputation threat intelligence is updated every 3 to 5 minutes.
![]() File sandboxing: If malware is detected, the Cisco AMP capabilities can put files in a sandbox to inspect its behavior, combining the inspection with machine-learning analysis to determine the threat level. Cisco Cognitive Threat Analytics (CTA) uses machine-learning algorithms to adapt over time.
File sandboxing: If malware is detected, the Cisco AMP capabilities can put files in a sandbox to inspect its behavior, combining the inspection with machine-learning analysis to determine the threat level. Cisco Cognitive Threat Analytics (CTA) uses machine-learning algorithms to adapt over time.
![]() File retrospection: After a malicious attempt or malware is detected, the Cisco WSA continues to cross-examine files over an extended period of time.
File retrospection: After a malicious attempt or malware is detected, the Cisco WSA continues to cross-examine files over an extended period of time.
![]() Application visibility and control: Allows the Cisco ASA to inspect and even block applications that are not allowed by the corporate security policy. For example, an administrator can allow users to use social media sites like Facebook but block micro-applications such as Facebook games.
Application visibility and control: Allows the Cisco ASA to inspect and even block applications that are not allowed by the corporate security policy. For example, an administrator can allow users to use social media sites like Facebook but block micro-applications such as Facebook games.