Appendix C
APP Channel Equalization
The APP equalizer outputs the channel information, which is expressed as {Lf(dk)}, associated with all data bits, given Nc received samples hosted by the vector y = y1Nc as well as the a priori information {Lb(dk)} corresponding to all data bits. The feed-forward information Lf(dk) corresponding to bit dk is given by
where L(dk|y) =ln[P(dk = + 1|y)/P(dk = −1|y)] represents the a posteriori Logarithmic Likelihood Ratio (LLR) of the data bit dk, which may be computed using the algorithm described below by following the approaches outlined in [69, 70, 72, 99].
The a posteriori LLR of thedatabit dk can be expressed in conjunction with the channel states sk−1 and sk as
The sequence y1Nc involved in the computation of the probability P(sk−1, sk, y1Nc) can be written in a more detailed form as P(sk−1, sk, y1k−1, yk, yNck+1). Applying the chain rule for joint probabilities, i.e., exploiting that we have P(a, b) = P(a)P(b|a), this expression yields the following decomposition of P(sk−1, sk, y1Nc):
Let us introduce the following definitions:
Then according to [48] the term αk(s) can be computed via the recursion
associated with the initial values of α0(q0) = 1 and α0(qi) = 0 for i ≠ 0. The term βk(s) can be computed via the recursion
in conjunction with the initial values of βNc(q0) = 1 and βNc(qi) = 0 for i ≠ 0. The term γk(sk−1, sk) represents the transition probability from state sk−1 to state sk, which can be further decomposed into
The transition probability γk(sk−1 = qi, sk = qj) is zero if the index pair (i, j) is not in ![]() . For pairs (i, j) within
. For pairs (i, j) within ![]() , the probability P(sk = qj|sk−1 = qi) is governed by the corresponding input symbol di,j, and p(yk|sk−1, sk) is governed by the corresponding output symbol vi,j, which can be described as
, the probability P(sk = qj|sk−1 = qi) is governed by the corresponding input symbol di,j, and p(yk|sk−1, sk) is governed by the corresponding output symbol vi,j, which can be described as
Given the AWGN channel of Equation (4.49), it follows that p(yk|νk) is given by
From Equation (C.2) and from the decomposition of P(sk−1, sk, y1Nc) given in Equation (C.3), it follows that
As shown in Equation (C.10), once the channel output samples are available the corresponding values of γk(s′, s) can be computed and stored. With the aid of these values, both αk(s) and βk(s) of Equations (C.7) and (C.8) can be computed, and, finally, the a posteriori LLR of Equation (C.12) can be obtained. For the sake of reducing the associated complexity, these computations can be performed in the log domain, as follows.
Let us introduce the following notations:
Consequently, Ak(s) can be formed iteratively by:
1. Initialization:
2. Forward Recursion:
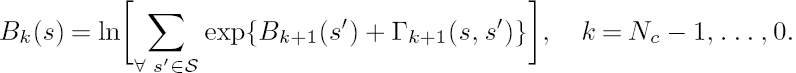
Bk(s) of (C.14) can be solved similarly, by:
1. Initialization:
2. Backward Recursion:
Furthermore, given the L-values of the encoded bits dk, i.e., given the a priori information of L(dk), and given the channel observations yk, Γk(s′, s) seen in Equation (C.15) can be calculated as follows:
Finally, the a posteriori LLR of Equation (C.12) can be obtained as follows:
The above calculations entail the evaluation of the logarithm of a sum of exponentials. These calculations may be carried out using either either the MAX-Log approximation or the Jacobian logarithm employing a look-up table [250].