iCloud Security
iCloud is a cloud service provided by Apple. A basic iCloud account is free and provides a connection to calendars, contacts, and other services that integrate with your Mac. Because iCloud has services that integrate with the Mac, it’s more than a traditional cloud solution, though. An iCloud account has options that include tracking the physical location of your Apple devices and potentially escrowing keys used for decrypting hard drives and remotely controlling computers. Because the iCloud account provides access to your computer, securing the account and the connection between the computer and the account is of paramount importance. This security starts with the Apple ID and extends to the settings used when setting up iCloud-based services on your Mac.
The Apple ID
Each iCloud account will have an Apple ID. This Apple ID is the gateway to most of the services described throughout the remainder of this chapter. When doing large-scale deployments, you will not need to deploy an Apple ID or even iCloud accounts for every single user. But it certainly helps if you do so. The Apple ID is a unique identifier provided by Apple, used to access a number of Apple services. This includes the most popular of these services: music purchased through iTunes. But also includes iCloud, Messages, and the iBookstore.
Much of the security concerns regarding Apple IDs arise from the fact that an Apple ID can be used to access a computer or synchronize data to iCloud or iCloud Backup even after an OS X computer or iPhone has been wiped. This is more of a concern on iPhones and iPads, where wiping a device should provide a sense of security that the data on the device has been removed due to the Managed Open-In feature of iOS, which restricts data within apps provided by an MDM solution from leaving the secure enclave of that solution. While you can wipe an OS X device, there are far more ways to synchronize data with third party services on a desktop operating system, and concerns around data security are lessened. A lot of software vendors now provide their software through the Mac App Store. And until all of the Mobile Device Management (MDM) vendors support device-based Volume Purchasing Program (VPP) access, this will be pointed out as a flaw to that program. iOS 9 and OS X 10.11 bring device-based VPP, but at the time of the writing of this book, that feature has yet to be implemented by the main VPP vendors.
So what can you do? MDM solutions do not report what Apple ID is being used to access software. However, you can use the defaults command to obtain information about Apple IDs in use on an OS X computer. You would do so by using defaults to read the global defaults domain. In the following example, we use the grep command to constrain our output to Apple IDs:
defaults read | grep AppleID
What an Apple ID Provides Access To
Today, most devices are going to need an Apple ID. The Apple ID becomes the gateway to most of the services described throughout the remainder of this chapter. The following is a list of Apple services that need an Apple ID:
- App Store: Buy Apps on the iOS and Mac App Stores and have them automatically download to your devices.
- Apple Developer programs: Access beta copies of software and developer tools.
- Apple Music: Apple’s music service that uses a monthly fee rather than purchasing each song individually.
- Apple Music Radio: Stream radio to your devices over the Apple Music Radio service.
- Apple Online Store: Purchase hardware and software through the Apple.com.
- Apple Retail services: Access to Concierge, Joint Venture, and programs, including the Apple Store app.
- Apple Support Communities: Access the Apple support site, ask questions, and answer any support requests you know the answer to.
- Apple TV: Access Content purchased on Apple from an Apple TV and control the TV with the Remote app on an iOS device.
- Back to My Mac: Provides remote access to a computer, even when that computer is using NAT behind a different firewall.
- Device Entrollment Program (DEP): Automatically associate devices owned by an organization with a Mobile Device Management (MDM) solution.
- FaceTime: Video conferencing with friends and family.
- FileVault Key Escrow: Option to keep the FileVault recovery key stored on a server.
- Find My Friends: Shows the physical location of friends you have added using the Find My Friends app, using GPS
- Find My Mac: Shows the physical location of your Apple devices using the iCloud web interface
- Game Center: Access scores in apps that support Game Center integration for friends using the Game Center app.
- iBooks Store: Access books and other multi-media content on the Apple iBooks Store.
- iChat: Legacy chat system from 10.8 and below.
- iCloud Calendars: Sets up the client for the Calendar app to work with an iCloud account.
- iCloud Contacts – sets up the client for the Contacts app to work with an iCloud account.
- iCoud Drive: allows certain apps to write data into storage on iCloud servers.
- iCloud Keychain: Synchronizes passwords and certificates between computers.
- iCloud Mail: Configures the Mail app to work with an iCloud account.
- iCloud Photos: Displays the photo stream and integrates iCloud Photo Library with your Mac and allows for iCloud Photo Sharing.
- iCloud Notes: Synchronizes notes created in the Notes app with an iCloud account.
- iMessage: Instant message with other iMessage users rather than using text messages.
- iTunes Genius: Tracks purchases on iTunes and allows you to find similar content to music in your library and purchase history.
- iTunes Home Sharing: Share data within apps such as iTunes and Photos from within a given Local Area Network (LAN).
- iTunes Match: Access music that was ripped from CDs and other media.
- iTunes Store: Purchase music that can be downloaded and listened to offline.
- iTunes U: Access podcasts posted by education institutions.
- Handoff – Shows the same content on an iPhone or iOS devices as on an OS X device if apps are built with Handoff support.
- My Apple ID (appleid.apple.com): Access information about an Apple ID and reset passwords and addresses for the Apple ID.
- Volume Purchase Program: Purchase applications in bulk and deploy those applications using codes, Apple IDs, or devices.
Given the number of services that an Apple ID provide access to, you will find that you need to secure an Apple ID. The first and most important part of securing the Apple ID is to use a strong password. Because Apple requires their customers maintain a good level of security, they have implemented password policies to keep users secure. These policies mean that Apple ID passwords must follow these rules:
- Have at least one capital letter
- Have at least one number
- Have at least 8 characters
- Not be used in the past year
- Not be the same as the user name
- Not have any consecutive, repeating characters (e.g. aa or bb)
- Not be a common password (e.g. ABCD1234)
While Apple doesn’t require it, we strongly recommend using special characters (e.g. !, *, or $ are pretty common) and that there be nothing that can identify you in the password, such as your child’s name, dog’s birthday, or the day you were married.
Apple also provides users the ability to reset access to an account. Here, you are given three security questions. When selecting these, don’t use easily identifiable information. For example, I was using my high school mascot for one, and then I realized my high school was listed on my Wikipedia page and therefore easily ascertained.
You can instead (and this is definitely recommended) add two-factor verification to your iCloud account. Doing so enhances security by requiring you to use a code sent to one of your Apple devices on another Apple device when you go to access certain features on that device, including resetting passwords and changing information on an account. If you haven’t done so already, you can enable two-factor authentication at https://appleid.apple.com/.
Changing passwords can be a terrible bore. You may find that when you have a lot of devices that require a new password to be entered or that you end up needing to remember this new password at annoying times. However, there’s no accounting for brute force, which is attempting iterations of a password until an attacker guesses the correct password. Therefore, set a routine reminder to change your password. This can be every 30 days or 90 days, but it should be reset routinely.
There are other things to be careful of. For example, anyone with an iCloud account is likely to get at least an occasional phishing scam email. If you get an email that seems like it came from Apple and opens a domain other than apple.com, don’t click on anything. These are likely simply directing you to portals that exist for the sole purpose of stealing the credentials to your Apple ID. Don’t send your account information to anyone. Don’t use an Apple ID on a public computer without clearing the remnants of the ID off the system when you stop using that device. Don’t sell or give a device away without first removing your Apple ID from the computer. And don’t distribute passwords to IDs over email.
The Apple ID can provide a lot of access to your computer. In addition to securing the Apple ID itself, you should also secure the account on devices that you own, and in some cases, do so on a service-by-service basis.
Suppress the iCloud Options at Startup
The first time a new user logs into a Mac, they should be prompted to provide credentials for an iCloud account. If your organization chooses not to use iCloud, you can disable this option by running the following command:
sudo defaults write /System/Library/User Template/Non_localized/Library/Preferences/com.apple.SetupAssistant DidSeeCloudSetup -bool TRUE
Once run, new accounts will no longer prompt users to provide iCloud credentials (and possibly use an iCloud account for their login to the computer). You can undo the option by running the following command:
sudo defaults write /System/Library/User Template/Non_localized/Library/Preferences/com.apple.SetupAssistant DidSeeCloudSetup -bool TRUE
Once this option is enabled, users will still be able to access iCloud; however, users will not be prompted to do so at their first login. You can also disable iCloud, which we’ll cover in the next section.
I hate disabling iCloud. We can debate the validity of killing iCloud access in any environment. However, it’s an organization’s option to allow or disallow iCloud and so our goal in this chapter is simply to provide the options to limit, restrict, or provide access securely, and to provide a solid understanding of the security ramifications of doing so.
The easiest way to disable iCloud access is going to be through a Mobile Device Management (MDM) solution, such as Profile Manager and the Casper Suite. To disable iCloud Drive and possibly leveraging iCloud for account passwords, open Profile Manager and create a new profile (or edit an existing profile). From there, select the OS X Restrictions payload. Click on the Functionality tab to see options for iCloud. As you can see in Figure 14-1, there, you’ll be provided with two options: “Allow iCloud documents & data” and “Allow use of iCloud password for local accounts.” These disable all access to iCloud Drive and disable using your iCloud password on your local computer respectively.

Figure 14-1. Authenticate to iCloud
Once you’ve configured the appropriate options, you can click on OK and save the profile. You can also use custom profiles to configure the options that we used the defaults commands to set, shown previously in this chapter.
To setup iCloud on a Mac, open System Preferences and click on the iCloud System Preference pane. From here, you will be prompted for a username and password for your iCloud account, as shown in Figure 14-2. Once entered, click on Sign In.
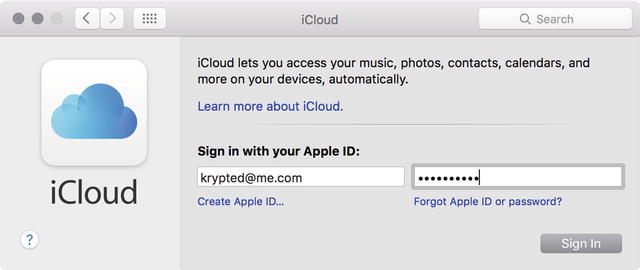
Figure 14-2. Authenticate to iCloud
Once the account is authenticated, you’ll be prompted on which features to allow access to. The main thing this screen is for is to give you the option to opt out of Find My Mac. Let’s leave these both checked, as in Figure 14-3 for now, and we’ll look at all the options later in this chapter. Click Next.

Figure 14-3. Enable iCloud Services
Once an account has been configured, you can see many of the iCloud services available on a Mac in the iCloud System Preference pane, shown in Figure 14-4. This is where an iCloud account is configured on each computer and once configured, where the settings for each service that iCloud provides are enabled. If you won’t be using a service, disable it. Most services are enabled by default, when you initially provide your iCloud credentials to access a system. But any service that’s enabled and not being used can provide access to resources that maybe shouldn’t be provided to.

Figure 14-4. The iCloud System Preference pane
In some cases, allowing access to a given service actually provides you with a more secure environment. For example, if you sync your Notes with a computer not otherwise backed up and the computer gets erased, you will still have access to your notes despite loosing access to the data on that one computer, as the notes are synchronized to iCloud. This is all, of course, provided that you secure access to the Apple ID that can access these notes.
In addition to checking and unchecking each service to configure that service on the computer, you will have an Options button for some services. These services can be granularly configured.
iCloud Drive
The first of these services that we’ll look at is iCloud Drive. You can store your files on iCloud Drive and they will synchronize with Apple’s cloud. This makes iCloud Drive similar to services such as Box, Dropbox and Google Drive. Click on the Options button for iCloud Drive and you will see each application installed on the computer that can leverage iCloud Drive for file storage. As you can see in Figure 14-5, these are currently mostly Apple-based applications, such as Photos and QuickTime. Uncheck each that you do not want to be able to use files on iCloud Drive or save files to iCloud Drive. Click Done when you’ve appropriately configured access.

Figure 14-5. iCloud Disk Options
Once you have configured iCloud Drive, you’ll see it listed (by default) in the sidebar of any Finder window, under the Favorites section (Figure 14-6). Once iCloud Drive has synchronized your files, you’ll see the layout of your iCloud drive in that folder and be able to access the files directly, opening them in any application you so choose.

Figure 14-6. iCloud Drive Folders
The most important aspect of iCloud Drive security is the knowledge that there are files that, by default, are going to be stored on iCloud. You can easily change this by running the following command on a computer, as is common using a standard patch management solution such as Munki or the Casper Suite:
defaults write NSGlobalDomain NSDocumentSaveNewDocumentsToCloud -bool false
The iCloud files are also by default cached using the OS X Server caching service. Any Mac computer with OS X Server 5 installed in your environment can act as a Caching server. The Caching server caches iCloud files by default. These files are encrypted with a key unique to each device with which the caching service is caching data for. While overall this service is a great tool for many an enterprise, it may be a concern for some that these files are cached on potentially rogue servers. You can disable the iCloud caching option (also known as Personal Caching) by writing an AllowPersonalCaching key into the Config.plist file at /Library/Server/Caching/Config/ of the server. The most graceful way to do this is using the serveradmin command, followed by the settings verb and then caching:AllowPersonalCaching option, setting that equals no, as follows:
sudo serveradmin settings caching:AllowPersonalCaching = no
To turn it back on:
sudo serveradmin settings caching:AllowPersonalCaching = yes
This can also be done by dropping a Config.plist file into the correct location for new server installations. You can also leverage this file to keep track of what computers that you have enrolled in a patch management system are running this service. If you see the file, the service has been enabled.
Find My Mac
One of the most interesting security ramifications of iCloud is Find My Mac. Once enabled, you can track the physical location of a Mac, which leverages Wi-Fi-based triangulation to show the physical location of a computer. This isn’t for everyone. To disable the Find My Mac option, click on the iCloud System Preference pane and then uncheck the box for Find My Mac.

Figure 14-7. Disable Find My Mac
Once the setting saves, you should no longer see the Mac on a map when you log into the iCloud web portal.
Back to My Mac
Back to My Mac allows you to log into your Mac from another computer that has your iCloud account installed. When you use two computers that run Back to My Mac, you will see computers that can be controlled using Back to My Mac by clicking on them in the sidebar of a Finder window. This feature works using NAT-PMP, as you can see in Figure 14-8.

Figure 14-8. Back to My Mac
Provided your iCloud account is secure, this feature is secure; however, if you wish to mitigate the risk associated with someone else gaining access to your iCloud account, uncheck the box for Back to My Mac.
The Mac App Store
The Mac App Store represented a completely new idea in software distribution. All software on the Mac App Store can be accessed through an Apple ID. Some of this software you pay for, some you don’t. From a security perspective, it’s worth nothing that Apple reviews all software before the apps get posted to the App Store. As you can see in Figure 14-9, even operating systems are distributed through the App Store.

Figure 14-9. The Mac App Store
When possible, use software from the Mac App Store. Any software posted on the Mac App Store is vetted by Apple prior to becoming available on the store. Additionally, software from the iOS App Store that is managed with MDM can have features limited by the MDM to secure content. While these types of options are not currently available for the Mac, it is only a matter of time before they are.
Summary
Apple provides a number of services with an iCloud account. Some of these can introduce risks into an environment. Others can help further secure an environment. I personally use most of the options that we looked at disabling in this chapter. But I don’t have official security requirements for my personal systems that many organizations have with their large fleets of computers. Each organization should review each option available and then determine which should be allowed and which should not. Then only disable the features that you don’t want to use.
