APPENDIX B
RESOURCES
Figure B.1
A sample contract from the Independent Computer Consultants Association (ICCA)
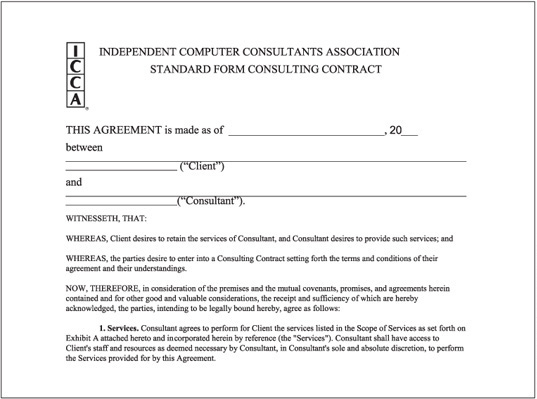
Courtesy Course Technology/Cengage Learning
BOOKS
Chapter 1
Ruhl, Janet. The Computer Consultants Guide. Wiley, 1997. ISBN 0471176494.
Meyer, Peter. Getting Started in Computer Security. Wiley, 1999. ISBN 0471348139.
Chapter 8
Palmer, Michael. Guide to Operating Systems, Enhanced Edition. Course Technology, Cengage Learning, 2007. ISBN 1418837199.
Chapter 12
Kahn, David. The Code Breakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet, Revised Edition. Scribner, 1996. ISBN 0684831309.
Schneier, Bruce. Applied Crytopgraphy: Protocols, Algorithms, and Source Code in C, Second Edition. Wiley, 1996. ISBN 0471117099.
Chapter 13
Cannon, Kelly, Kelly Caudle, and Anthony V. Chiarella. CCNA Guide to Cisco Networking Fundamentals, Fourth Edition. Course Technology, Cengage Learning, 2009. ISBN 1418837059.
WEB SITES
Chapter 1
Professional Certifications, Security Jobs, and Applicable Laws
www.ncsl.org/programs/lis/CIP/hacklaw.htm
Chapter 2
Protocols
www.cisco.com/security_services/ciag/documents/v6-v4-threats.pdf
Chapter 3
Identifying Malware
Searching for Known Vulnerabilities and Exposures
www.lysator.liu.se/mit-guide/MITLockGuide.pdf
www.microsoft.com/security/bulletins/default.mspx
Chapter 4
Footprinting
http://gnu.org/software/wget/wget.html
http://members.shaw.ca/nicholas.fong/dig
www.paterva.com/web4/index.php/maltego
www.securityfocus.com/tools/139
Chapter 5
Port Scanning
Chapter 6
Enumeration
www.l0phtcrack.com/download.html
Chapter 7
Programming
http://activestate.com/activeperl
http://history.perl.org/PerlTimeline.html
Chapter 8
Desktop and Server OSs
www.cisecurity.org/benchmarks.html
www.iana.org/assignments/port-numbers
www.microsoft.com/technet/security/Bulletin/MS09-044.mspx
www.microsoft.com/technet/security/tools/mbsahome.mspx
www.microsoft.com/technet/security/tools
www.ntsecurity.nu/toolbox/lns/
http://support.microsoft.com/kb/325864
www.trustedcs.com www.us-cert.gov
Chapter 9
Embedded OSs
Chapter 10
Web Server Security
www.adobe.com/support/security/
www.microsoft.com/technet/security/current.aspx
http://poweryogi.blogspot.com/2005/03/hbsapplyyourself-admit-status-snafu.html
www.us-cert.gov/cas/alerts/SA09-133B.html
Chapter 11
Wireless Networking
www.blackalchemy.to/project/fakeap/
http://grouper.ieee.org/groups/802/
www.oreillynet.com/cs/weblog/view/wlg/448
Chapter 12
Cryptography
http://cracker.offensive-security.com
www.mandylionlabs.com/documents/BFTCalc.xls
www.nsa.gov/ia/programs/suiteb_cryptography
Chapter 13
Network Protection Systems
www.ripe.net/news/study-youtube-hijacking.html
www.securityfocus.com/infocus/1659
www.specter.com or www.spectorcne.com



