Chapter 6
Security Assessment and Testing (Domain 6)
-
During a port scan, Susan discovers a system running services on TCP and UDP 137-139 and TCP 445, as well as TCP 1433. What type of system is she likely to find if she connects to the machine?
- A Linux email server
- A Windows SQL server
- A Linux file server
- A Windows workstation
-
Which of the following is a method used to design new software tests and to ensure the quality of tests?
- Code auditing
- Static code analysis
- Regression testing
- Mutation testing
-
During a port scan, Lauren found TCP port 443 open on a system. Which tool is best suited to scanning the service that is most likely running on that port?
- zzuf
- Nikto
- Metasploit
- sqlmap
-
What message logging standard is commonly used by network devices, Linux and Unix systems, and many other enterprise devices?
- Syslog
- Netlog
- Eventlog
- Remote Log Protocol (RLP)
-
Alex wants to use an automated tool to fill web application forms to test for format string vulnerabilities. What type of tool should he use?
- A black box
- A brute-force tool
- A fuzzer
- A static analysis tool
-
Susan needs to scan a system for vulnerabilities, and she wants to use an open source tool to test the system remotely. Which of the following tools will meet her requirements and allow vulnerability scanning?
- Nmap
- OpenVAS
- MBSA
- Nessus
-
NIST Special Publication 800-53A describes four major types of assessment objects that can be used to identify items being assessed. If the assessment covers IPS devices, which of the types of assessment objects is being assessed?
- A specification
- A mechanism
- An activity
- An individual
-
Jim has been contracted to perform a penetration test of a bank’s primary branch. In order to make the test as real as possible, he has not been given any information about the bank other than its name and address. What type of penetration test has Jim agreed to perform?
- A crystal box penetration test
- A gray box penetration test
- A black box penetration test
- A white box penetration test
-
As part of a penetration test, Alex needs to determine if there are web servers that could suffer from the 2014 Heartbleed bug. What type of tool could he use, and what should he check to verify that the tool can identify the problem?
- A vulnerability scanner, to see whether the scanner has a signature or test for the Heartbleed CVE number
- A port scanner, to see whether the scanner properly identifies SSL connections
- A vulnerability scanner, to see whether the vulnerability scanner detects problems with the Apache web server
- A port scanner, to see whether the port scanner supports TLS connections
-
In a response to a Request for Proposal, Susan receives a SAS-70 Type 1 report. If she wants a report that includes operating effectiveness detail, what should Susan ask for as followup and why?
- An SAS-70 Type II, because Type I only covers a single point in time
- An SOC Type 1, because Type II does not cover operating effectiveness
- An SOC Type 2, because Type I does not cover operating effectiveness
- An SAC-70 type 3, because Types 1 and 2 are outdated and no longer accepted
-
During a wireless network penetration test, Susan runs aircrack-ng against the network using a password file. What might cause her to fail in her password-cracking efforts?
- Use of WPA2 encryption
- Running WPA2 in Enterprise mode
- Use of WEP encryption
- Running WPA2 in PSK mode
-
Which type of SOC report is best suited to provide assurance to users about an organization’s security, availability, and the integrity of their service operations?
- An SOC 1 Type 2 report
- An SOC 2 report
- An SOC 3 report
- An SOC 1 Type 1 report
-
What type of testing is used to ensure that separately developed software modules properly exchange data?
- Fuzzing
- Dynamic testing
- Interface testing
- API checksums
-
Which of the following is not a potential problem with active wireless scanning?
- Accidently scanning apparent rogue devices that actually belong to guests
- Causing alarms on the organization’s wireless IPS
- Scanning devices that belong to nearby organizations
- Misidentifying rogue devices
-
Ben uses a fuzzing tool that develops data models and creates fuzzed data based on information about how the application uses data to test the application. What type of fuzzing is Ben doing?
- Mutation
- Parametric
- Generational
- Derivative
-
Saria wants to log and review traffic information between parts of her network. What type of network logging should she enable on her routers to allow her to perform this analysis?
- Audit logging
- Flow logging
- Trace logging
- Route logging
-
Jim has been contracted to conduct a gray box penetration test, and his clients have provided him with the following information about their networks so that he can scan them.
- Data center: 10.10.10.0/24
- Sales: 10.10.11.0/24
- Billing: 10.10.12.0/24
- Wireless: 192.168.0.0/16
What problem will Jim encounter if he is contracted to conduct a scan from offsite?
- The IP ranges are too large to scan efficiently.
- The IP addresses provided cannot be scanned.
- The IP ranges overlap and will cause scanning issues.
- The IP addresses provided are RFC 1918 addresses.
-
Karen’s organization has been performing system backups for years but has not used the backups frequently. During a recent system outage, when administrators tried to restore from backups they found that the backups had errors and could not be restored. Which of the following options should Karen avoid when selecting ways to ensure that her organization’s backups will work next time?
- Log review
- MTD verification
- Hashing
- Periodic testing
Questions 19, 20, and 21 refer to the following scenario.
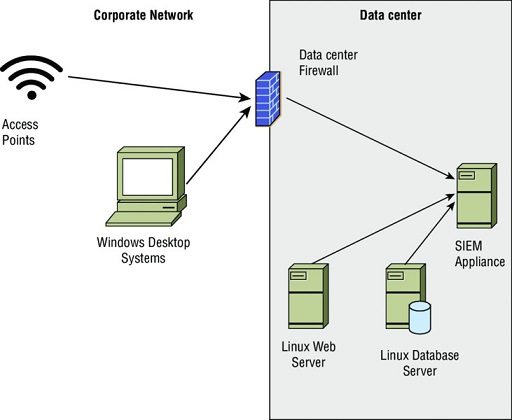
The company that Jennifer works for has implemented a central logging infrastructure, as shown in the following image. Use this diagram and your knowledge of logging systems to answer the following questions.
-
Jennifer needs to ensure that all Windows systems provide identical logging information to the SIEM. How can she best ensure that all Windows desktops have the same log settings?
- Perform periodic configuration audits.
- Use Group Policy.
- Use Local Policy.
- Deploy a Windows syslog client.
-
During normal operations, Jennifer’s team uses the SIEM appliance to monitor for exceptions received via syslog. What system shown does not natively have support for syslog events?
- Enterprise wireless access points
- Windows desktop systems
- Linux web servers
- Enterprise firewall devices
-
What technology should an organization use for each of the devices shown in the diagram to ensure that logs can be time sequenced across the entire infrastructure?
- Syslog
- NTP
- Logsync
- SNAP
-
During a penetration test, Danielle needs to identify systems, but she hasn’t gained sufficient access on the system she is using to generate raw packets. What type of scan should she run to verify the most open services?
- A TCP connect scan
- A TCP SYN scan
- A UDP scan
- An ICMP scan
-
During a port scan using nmap, Joseph discovers that a system shows two ports open that cause him immediate worry:
- 21/open
- 23/open
What services are likely running on those ports?
- SSH and FTP
- FTP and Telnet
- SMTP and Telnet
- POP3 and SMTP
-
Saria’s team is working to persuade their management that their network has extensive vulnerabilities that attackers could exploit. If she wants to conduct a realistic attack as part of a penetration test, what type of penetration test should she conduct?
- Crystal box
- Gray box
- White box
- Black box
-
What method is commonly used to assess how well software testing covered the potential uses of a an application?
- A test coverage analysis
- A source code review
- A fuzz analysis
- A code review report
-
Testing that is focused on functions that a system should not allow are an example of what type of testing?
- Use case testing
- Manual testing
- Misuse case testing
- Dynamic testing
-
What type of monitoring uses simulated traffic to a website to monitor performance?
- Log analysis
- Synthetic monitoring
- Passive monitoring
- Simulated transaction analysis
-
Which of the following vulnerabilities is unlikely to be found by a web vulnerability scanner?
- Path disclosure
- Local file inclusion
- Race condition
- Buffer overflow
-
Jim uses a tool that scans a system for available services, then connects to them to collect banner information to determine what version of the service is running. It then provides a report detailing what it gathers, basing results on service fingerprinting, banner information, and similar details it gathers combined with CVE information. What type of tool is Jim using?
- A port scanner
- A service validator
- A vulnerability scanner
- A patch management tool
-
Emily builds a script that sends data to a web application that she is testing. Each time the script runs, it sends a series of transactions with data that fits the expected requirements of the web application to verify that it responds to typical customer behavior. What type of transactions is she using, and what type of test is this?
- Synthetic, passive monitoring
- Synthetic, use case testing
- Actual, dynamic monitoring
- Actual, fuzzing
-
What passive monitoring technique records all user interaction with an application or website to ensure quality and performance?
- Client/server testing
- Real user monitoring
- Synthetic user monitoring
- Passive user recording
-
Earlier this year, the information security team at Jim’s employer identified a vulnerability in the web server that Jim is responsible for maintaining. He immediately applied the patch and is sure that it installed properly, but the vulnerability scanner has continued to flag the system as vulnerable even though Jim is sure the patch is installed. Which of the following options is Jim’s best choice to deal with the issue?
- Uninstall and reinstall the patch.
- Ask the information security team to flag the system as patched and not vulnerable.
- Update the version information in the web server’s configuration.
- Review the vulnerability report and use alternate remediation instructions if they are provided.
-
Angela wants to test a web browser’s handling of unexpected data using an automated tool. What tool should she choose?
- Nmap
- zzuf
- Nessus
- Nikto
-
STRIDE, which stands for Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege, is useful in what part of application threat modeling?
- Vulnerability assessment
- Misuse case testing
- Threat categorization
- Penetration test planning
-
Why should passive scanning be conducted in addition to implementing wireless security technologies like wireless intrusion detection systems?
- It can help identify rogue devices.
- It can test the security of the wireless network via scripted attacks.
- Their short dwell time on each wireless channel can allow them to capture more packets.
- They can help test wireless IDS or IPS systems.
-
During a penetration test, Lauren is asked to test the organization’s Bluetooth security. Which of the following is not a concern she should explain to her employers?
- Bluetooth scanning can be time consuming.
- Many devices that may be scanned are likely to be personal devices.
- Bluetooth passive scans may require multiple visits at different times to identify all targets.
- Bluetooth active scans can’t evaluate the security mode of Bluetooth devices.
-
What term describes software testing that is intended to uncover new bugs introduced by patches or configuration changes?
- Nonregression testing
- Evolution testing
- Smoke testing
- Regression testing
-
Which of the tools cannot identify a target’s operating system for a penetration tester?
- Nmap
- Nessus
- Nikto
- sqlmap
-
Susan needs to predict high-risk areas for her organization and wants to use metrics to assess risk trends as they occur. What should she do to handle this?
- Perform yearly risk assessments.
- Hire a penetration testing company to regularly test organizational security.
- Identify and track key risk indicators.
- Monitor logs and events using a SIEM device.
-
What major difference separates synthetic and passive monitoring?
- Synthetic monitoring only works after problems have occurred.
- Passive monitoring cannot detect functionality issues.
- Passive monitoring only works after problems have occurred.
- Synthetic monitoring cannot detect functionality issues.
-
Chris uses the standard penetration testing methodology shown here. Use this methodology and your knowledge of penetration testing to answer the following questions about tool usage during a penetration test.
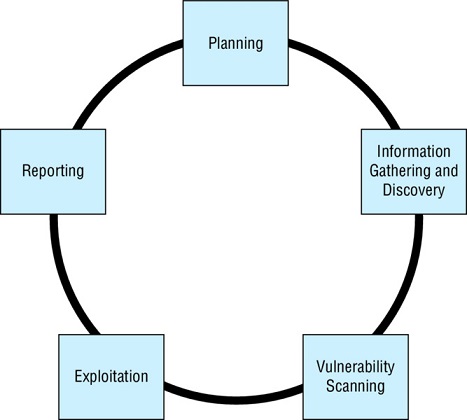
What task is the most important during Phase 1, Planning?
- Building a test lab
- Getting authorization
- Gathering appropriate tools
- Determining if the test is white, black, or gray box
-
Which of the following tools is most likely to be used during discovery?
- Nessus
- john
- Nmap
- Nikto
-
Which of these concerns is the most important to address during planning to ensure the reporting phase does not cause problems?
- Which CVE format to use
- How the vulnerability data will be stored and sent
- Which targets are off limits
- How long the report should be
-
What four types of coverage criteria are commonly used when validating the work of a code testing suite?
- Input, statement, branch, and condition coverage
- Function, statement, branch, and condition coverage
- API, branch, bounds, and condition coverage
- Bounds, branch, loop, and condition coverage
-
As part of his role as a security manager, Jacob provides the following chart to his organization’s management team. What type of measurement is he providing for them?

- A coverage rate measure
- A key performance indicator
- A time to live metric
- A business criticality indicator
-
What does using unique user IDs for all users provide when reviewing logs?
- Confidentiality
- Integrity
- Availability
- Accountability
-
Which of the following is not an interface that is typically tested during the software testing process?
- APIs
- Network interfaces
- UIs
- Physical interfaces
-
What protocol is used to handle vulnerability management data?
- VML
- SVML
- SCAP
- VSCAP
-
Misconfiguration, logical and functional flaws, and poor programming practices are all causes of what type of issue?
- Fuzzing
- Security vulnerabilities
- Buffer overflows
- Race conditions
-
Which of the following strategies should not be used to handle a vulnerability identified by a vulnerability scanner?
- Install a patch.
- Use a workaround fix.
- Update the banner or version number.
- Use an application layer firewall or IPS to prevent attacks against the identified vulnerability.
-
During a penetration test Saria calls her target’s help desk claiming to be the senior assistance to an officer of the company. She requests that the help desk reset the officer’s password because of an issue with his laptop while traveling and persuades them to do so. What type of attack has she successfully completed?
- Zero knowledge
- Help desk spoofing
- Social engineering
- Black box
-
In this image, what issue may occur due to the log handling settings?

- Log data may be lost when the log is archived.
- Log data may be overwritten.
- Log data may not include needed information.
- Log data may fill the system disk.
-
Which of the following is not a hazard associated with penetration testing?
- Application crashes
- Denial of service
- Exploitation of vulnerabilities
- Data corruption
-
Which NIST special publication covers the assessment of security and privacy controls?
- 800-12
- 800-53A
- 800-34
- 800-86
-
What type of port scanning is known as “half open” scanning?
- TCP Connect
- TCP ACK
- TCP SYN
- Xmas
-
Lauren is performing a review of a third-party service organization and wants to determine if the organization’s policies and procedures are effectively enforced over a period of time. What type of industry standard assessment report should she request?
- SSAE 16 SOC 1 Type I
- SAS 70 Type I
- SSAE 16 SOC 1 Type II
- SAS 70 Type II
-
Jim is working with a penetration testing contractor who proposes using Metasploit as part of her penetration testing effort. What should Jim expect to occur when Metasploit is used?
- Systems will be scanned for vulnerabilities.
- Systems will have known vulnerabilities exploited.
- Services will be probed for buffer overflow and other unknown flaws.
- Systems will be tested for zero-day exploits.
-
During a third-party audit, Jim’s company receives a finding that states, “The administrator should review backup success and failure logs on a daily basis, and take action in a timely manner to resolve reported exceptions.” What is the biggest issue that is likely to result if Jim’s IT staff need to restore from a backup?
- They will not know if the backups succeeded or failed.
- The backups may not be properly logged.
- The backups may not be usable.
- The backup logs may not be properly reviewed.
-
Jim is helping his organization decide on audit standards for use throughout their international organization. Which of the following is not an IT standard that Jim’s organization is likely to use as part of its audits?
- COBIT
- SSAE-16
- ITIL
- ISO27002
-
Which of the following best describes a typical process for building and implementing an Information Security Continuous Monitoring program as described by NIST Special Publication 800-137?
- Define, establish, implement, analyze and report, respond, review, and update
- Design, build, operate, analyze, respond, review, revise
- Prepare, detect and analyze, contain, respond, recover, report
- Define, design, build, monitor, analyze, react, revise
-
Lauren’s team conducts regression testing on each patch that they release. What key performance measure should they maintain to measure the effectiveness of their testing?
- Time to remediate vulnerabilities
- A measure of the rate of defect recurrence
- A weighted risk trend
- A measure of the specific coverage of their testing
-
Which of the following types of code review is not typically performed by a human?
- Software inspections
- Code review
- Static program analysis
- Software walkthroughs
Susan is the lead of a Quality Assurance team at her company. They have been tasked with the testing for a major release of their company’s core software product. Use your knowledge of code review and testing to answer the following three questions.
-
Susan’s team of software testers are required to test every code path, including those that will only be used when an error condition occurs. What type of testing environment does her team need to ensure complete code coverage?
- White box
- Gray box
- Black box
- Dynamic
-
As part of the continued testing of their new application, Susan’s quality assurance team has designed a set of test cases for a series of black box tests. These functional tests are then run, and a report is prepared explaining what has occurred. What type of report is typically generated during this testing to indicate test metrics?
- A test coverage report
- A penetration test report
- A code coverage report
- A line coverage report
-
As part of their code coverage testing, Susan’s team runs the analysis in a nonproduction environment using logging and tracing tools. Which of the following types of code issues is most likely to be missed during testing due to this change in the operating environment?
- Improper bounds checking
- Input validation
- A race condition
- Pointer manipulation
-
What step should occur after a vulnerability scan finds a critical vulnerability on a system?
- Patching
- Reporting
- Remediation
- Validation
-
Kathleen is reviewing the code for an application. She first plans the review, conducts an overview session with the reviewers and assigns roles, and then works with the reviewers to review materials and prepare for their roles. Next, she intends to review the code, rework it, and ensure that all defects found have been corrected.
What type of review is Kathleen conducting?
- A dynamic test
- Fagan inspection
- Fuzzing
- A Roth-Parker review
-
Danielle wants to compare vulnerabilities she has discovered in her data center based on how exploitable they are, if exploit code exists, as well as how hard they are to remediate. What scoring system should she use to compare vulnerability metrics like these?
- CSV
- NVD
- VSS
- CVSS
-
During a port scan of his network, Alex finds that a number of hosts respond on TCP ports 80, 443, 515, and 9100 in offices throughout his organization. What type of devices is Alex likely discovering?
- Web servers
- File servers
- Wireless access points
- Printers
-
Nikto, Burp Suite, and Wapiti are all examples of what type of tool?
- Web application vulnerability scanners
- Code review tools
- Vulnerability scanners
- Port scanners
-
During an nmap scan, what three potential statuses are provided for a port?
- Open, unknown, closed
- Open, closed, and filtered
- Available, denied, unknown
- Available, unavailable, filtered
-
Which of the following is not a method of synthetic transaction monitoring?
- Database monitoring
- Traffic capture and analysis
- User session monitoring
- Website performance monitoring
-
Susan needs to ensure that the interactions between the components of her e-commerce application are all handled properly. She intends to verify communications, error handling, and session management capabilities throughout her infrastructure. What type of testing is she planning to conduct?
- Misuse case testing
- Fuzzing
- Regression testing
- Interface testing
-
Jim is designing his organization’s log management systems and knows that he needs to carefully plan to handle the organization’s log data. Which of the following is not a factor that Jim should be concerned with?
- The volume of log data
- A lack of sufficient log sources
- Data storage security requirements
- Network bandwidth
-
Jim has contracted with a software testing organization that uses automated testing tools to validate software. He is concerned that they may not completely test all statements in his software. What measurement should he ask for in their report to provide information about this?
- A use case count
- A test coverage report
- A code coverage report
- A code review report
-
When a Windows system is rebooted, what type of log is generated?
- Error
- Warning
- Information
- Failure audit
-
During a review of access logs, Alex notices that Danielle logged into her workstation in New York at 8 a.m. daily, but that she was recorded as logging into her department’s main web application shortly after 3 a.m. daily. What common logging issue has Alex likely encountered?
- Inconsistent log formatting
- Modified logs
- Inconsistent timestamps
- Multiple log sources
-
What type of vulnerability scan accesses configuration information from the systems it is run against as well as information that can be accessed via services available via the network?
- Authenticated scans
- Web application scans
- Unauthenticated scans
- Port scans
Ben’s organization has begun to use STRIDE to assess their software, and has identified threat agents and the business impacts that these threats could have. Now they are working to identify appropriate controls for the issues they have identified. Use the STRIDE model to answer the following three questions.
-
Ben’s development team needs to address an authorization issue, resulting in an elevation of privilege threat. Which of the following controls is most appropriate to this type of issue?
- Auditing and logging is enabled.
- RBAC is used for specific operations.
- Data type and format checks are enabled.
- User input is tested against a whitelist.
-
Ben’s team is attempting to categorize a transaction identification issue that is caused by use of a symmetric key shared by multiple servers. What STRIDE category should this fall into?
- Information disclosure
- Denial of service
- Tampering
- Repudiation
-
Ben wants to prevent or detect tampering with data. Which of the following is not an appropriate solution?
- Hashes
- Digital signatures
- Filtering
- Authorization controls
-
Which NIST document covers the creation of an Information Security Continuous Monitoring (ISCM)?
- NIST SP 800-137
- NIST SP 800-53a
- NIST SP 800-145
- NIST SP 800-50
-
Which of the following is not an issue when using fuzzing to find program faults?
- They often find only simple faults.
- Fuzz testing bugs are often severe.
- Fuzzers may not fully cover the code.
- Fuzzers can’t reproduce errors.
-
What term describes an evaluation of the effectiveness of security controls performed by a third party?
- A security assessment
- A penetration test
- A security audit
- A security test
During a port scan, Ben uses nmap’s default settings and sees the following results. Use this information to answer the following three questions.

-
If Ben is conducting a penetration test, what should his next step be after receiving these results?
- Connect to the web server using a web browser.
- Connect via Telnet to test for vulnerable accounts.
- Identify interesting ports for further scanning.
- Use sqlmap against the open databases.
-
Based on the scan results, what OS was the system that was scanned most likely running?
- Windows Desktop
- Linux
- Network device
- Windows Server
-
Ben’s manager expresses concern about the coverage of his scan. Why might his manager have this concern?
- Ben did not test UDP services.
- Ben did not discover ports outside the “well-known ports.”
- Ben did not perform OS fingerprinting.
- Ben tested only a limited number of ports.
-
What technique relies on reviewing code without running it?
- Fuzzing
- Black box analysis
- Static analysis
- Gray box analysis
-
Saria needs to write a request for proposal for code review and wants to ensure that the reviewers take the business logic behind her organization’s applications into account. What type of code review should she specify in the RFP?
- Static
- Fuzzing
- Manual
- Dynamic
-
What type of diagram used in application threat modeling includes malicious users as well as descriptions like mitigates and threatens?
- Threat trees
- STRIDE charts
- Misuse case diagrams
- DREAD diagrams
-
What is the first step that should occur before a penetration test is performed?
- Data gathering
- Port scanning
- Getting permission
- Planning
-
What international framework was SSAE-16 based on?
- ISO27001
- SAS70
- SOX
- ISAE 3402
-
During a penetration test of her organization, Kathleen’s IPS detects a port scan that has the URG, FIN, and PSH flags set and produces an alarm. What type of scan is the penetration tester attempting?
- A SYN scan
- A TCP flag scan
- An Xmas scan
- An ACK scan
-
Nmap is an example of what type of tool?
- Vulnerability scanner
- Web application fuzzer
- Network design and layout
- Port scanner
-
What type of vulnerabilities will not be found by a vulnerability scanner?
- Local vulnerabilities
- Service vulnerabilities
- Zero-day vulnerabilities
- Vulnerabilities that require authentication
-
MITRE’s CVE database provides what type of information?
- Current versions of software
- Patching information for applications
- Vulnerability information
- A list of costs versus effort required for common processes
-
A zero-day vulnerability is announced for the popular Apache web server in the middle of a workday. In Jacob’s role as an information security analyst, he needs to quickly scan his network to determine what servers are vulnerable to the issue. What is Jacob’s best route to quickly identify vulnerable systems?
- Immediately run Nessus against all of the servers to identify which systems are vulnerable.
- Review the CVE database to find the vulnerability information and patch information.
- Create a custom IDS or IPS signature.
- Identify affected versions and check systems for that version number using an automated scanner.
NIST Special Publication 800-115, the Technical Guide to Information Security Testing and Assessment, provides NIST’s process for penetration testing. Using this image as well as your knowledge of penetration testing, answer the following questions.

-
Which of the following is not a part of the discovery phase?
- Hostname and IP address information gathering
- Service information capture
- Dumpster diving
- Privilege escalation
-
NIST specifies four attack phase steps: gaining access, escalating privileges, system browsing, and installing additional tools. Once attackers install additional tools, what phase will a penetration tester typically return to?
- Discovery
- Gaining access
- Escalating privileges
- System browsing
-
Which of the following is not a typical part of a penetration test report?
- A list of identified vulnerabilities
- All sensitive data that was gathered during the test
- Risk ratings for each issue discovered
- Mitigation guidance for issues identified
