Chapter 5
Identity and Access Management (Domain 5)
-
Which of the following is best described as an access control model that focuses on subjects and identifies the objects that each subject can access?
- An access control list
- An implicit denial list
- A capability table
- A rights management matrix
-
Jim’s organization-wide implementation of IDaaS offers broad support for cloud-based applications. The existing infrastructure for Jim’s company does not use centralized identity services but uses Active Directory for AAA services. Which of the following choices is the best option to recommend to handle the company’s onsite identity needs?
- Integrate onsite systems using OAuth.
- Use an on-premise third-party identity service.
- Integrate onsite systems using SAML.
- Design an in-house solution to handle the organization’s unique needs.
-
Which of the following is not a weakness in Kerberos?
- The KDC is a single point of failure.
- Compromise of the KDC would allow attackers to impersonate any user.
- Authentication information is not encrypted.
- It is susceptible to password guessing.
-
Voice pattern recognition is what type of authentication factor?
- Type 1
- Type 2
- Type 3
- Type 4
-
If Susan’s organization requires her to log in with her username, a PIN, a password, and a retina scan, how many distinct types of factor has she used?
- One
- Two
- Three
- Four
-
Which of the following items are not commonly associated with restricted interfaces?
- Shells
- Keyboards
- Menus
- Database views
-
During a log review, Saria discovers a series of logs that show login failures as shown here:
- Jan 31 11:39:12 ip-10-0-0-2 sshd[29092]: Invalid user admin from remotehost passwd=orange
- Jan 31 11:39:20 ip-10-0-0-2 sshd[29098]: Invalid user admin from remotehost passwd=Orang3
- Jan 31 11:39:23 ip-10-0-0-2 sshd[29100]: Invalid user admin from remotehost passwd=Orange93
- Jan 31 11:39:31 ip-10-0-0-2 sshd[29106]: Invalid user admin from remotehost passwd=Orangutan1
- Jan 31 20:40:53 ip-10-0-0-254 sshd[30520]: Invalid user admin from remotehost passwd=Orangemonkey
What type of attack has Saria discovered?
- A brute force attack
- A man-in-the-middle attack
- A dictionary attack
- A rainbow table attack
-
What type of attack can be prevented by using a trusted path?
- Dictionary attacks
- Brute force attacks
- Man-in-the-middle attacks
- Login spoofing
-
What major issue often results from decentralized access control?
- Access outages may occur.
- Control is not consistent.
- Control is too granular.
- Training costs are high.
-
Callback to a home phone number is an example of what type of factor?
- Type 1
- Somewhere you are
- Type 3
- Geographic
-
Kathleen needs to set up an Active Directory trust to allow authentication with an existing Kerberos K5 domain. What type of trust does she need to create?
- A shortcut trust
- A forest trust
- An external trust
- A realm trust
-
Which of the following AAA protocols is the most commonly used?
- TACACS
- TACACS+
- XTACACS
- Super TACACS
-
Which of the following is not a single sign-on implementation?
- Kerberos
- ADFS
- CAS
- RADIUS
-
As seen in the following image, a user on a Windows system is not able to use the “Send Message” functionality. What access control model best describes this type of limitation?

- Least privilege
- Need to know
- Constrained interface
- Separation of duties
-
What type of access controls allow the owner of a file to grant other users access to it using an access control list?
- Role based
- Non-discretionary
- Rule based
- Discretionary
-
Alex’s job requires him to see personal health information (PHI) to ensure proper treatment of patients. His access to their medical records does not provide access to patient addresses or billing information. What access control concept best describes this control?
- Separation of duties
- Constrained interfaces
- Context-dependent control
- Need to know
Using your knowledge of the Kerberos logon process and the following diagram, answer questions 17, 18, and 19.

-
At point A in the diagram, the client sends the username and password to the KDC. How is the username and password protected?
- 3DES encryption
- TLS encryption
- SSL encryption
- AES encryption
-
At point B in the diagram, what two important elements does the KDC send to the client after verifying that the username is valid?
- An encrypted TGT and a public key
- An access ticket and a public key
- An encrypted, time-stamped TGT and a symmetric key encrypted with a hash of the user’s password
- An encrypted, time-stamped TGT and an access token
-
What tasks must the client perform before it can use the TGT?
- It must generate a hash of the TGT and decrypt the symmetric key.
- It must install the TGT and decrypt the symmetric key.
- It must decrypt the TGT and the symmetric key.
- It must send a valid response using the symmetric key to the KDC and must install the TGT.
-
Jacob is planning his organization’s biometric authentication system and is considering retina scans. What concern may be raised about retina scans by others in his organization?
- Retina scans can reveal information about medical conditions.
- Retina scans are painful because they require a puff of air in the user’s eye.
- Retina scanners are the most expensive type of biometric device.
- Retina scanners have a high false positive rate and will cause support issues.
-
Mandatory access control is based on what type of model?
- Discretionary
- Group based
- Lattice based
- Rule based
-
Which of the following is not a type of attack used against access controls?
- Dictionary attack
- Brute force attack
- Teardrop
- Man-in-the-middle attack
-
What is the best way to provide accountability for the use of identities?
- Logging
- Authorization
- Digital signatures
- Type 1 authentication
-
Jim has worked in human relations, payroll, and customer service roles in his company over the past few years. What type of process should his company perform to ensure that he has appropriate rights?
- Re-provisioning
- Account review
- Privilege creep
- Account revocation
-
Biba is what type of access control model?
- MAC
- DAC
- Role BAC
- ABAC
-
Which of the following is a client/server protocol designed to allow network access servers to authenticate remote users by sending access request messages to a central server?
- Kerberos
- EAP
- RADIUS
- OAuth
-
What type of access control is being used in the following permission listing:
- Storage Device X
- User1: Can read, write, list
- User2: Can read, list
- User3: Can read, write, list, delete
- User4: Can list
- Resource-based access controls
- Role-based access controls
- Mandatory access controls
- Rule-based access controls
-
Angela uses a sniffer to monitor traffic from a RADIUS server configured with default settings. What protocol should she monitor and what traffic will she be able to read?
- UDP, none. All RADIUS traffic is encrypted.
- TCP, all traffic but the passwords, which are encrypted
- UDP, all traffic but the passwords, which are encrypted
- TCP, none. All RADIUS traffic is encrypted.
-
Which of the following is not part of a Kerberos authentication system?
- KDC
- TGT
- AS
- TS
-
When an application or system allows a logged-in user to perform specific actions, it is an example of what?
- Roles
- Group management
- Logins
- Authorization
-
Alex has been employed by his company for over a decade and has held a number of positions in the company. During an audit, it is discovered that he has access to shared folders and applications due to his former roles. What issue has Alex’s company encountered?
- Excessive provisioning
- Unauthorized access
- Privilege creep
- Account review
-
Which of the following is not a common threat to access control mechanisms?
- Fake login pages
- Phishing
- Dictionary attacks
- Man-in-the-middle attacks
-
What term properly describes what occurs when two or more processes require access to the same resource and must complete their tasks in the proper order for normal function?
- Collisions
- Race conditions
- Determinism
- Out-of-order execution
-
What type of access control scheme is shown in the following table?
Highly Sensitive Red Blue Green Confidential Purple Orange Yellow Internal Use Black Gray White Public Clear Clear Clear - RBAC
- DAC
- MAC
- TBAC
-
Which of the following is not a valid LDAP DN (distinguished name)?
- cn=ben+ou=sales
- ou=example
- cn=ben,ou=example;
- ou=example,dc=example,dc=com+dc=org
-
When a subject claims an identity, what process is occurring?
- Login
- Identification
- Authorization
- Token presentation
-
Dogs, guards, and fences are all common examples of what type of control?
- Detective
- Recovery
- Administrative
- Physical
-
Susan’s organization is updating its password policy and wants to use the strongest possible passwords. What password requirement will have the highest impact in preventing brute force attacks?
- Change maximum age from 1 year to 180 days.
- Increase the minimum password length from 8 characters to 16 characters.
- Increase the password complexity so that at least three character classes (such as uppercase, lowercase, numbers, and symbols) are required.
- Retain a password history of at least four passwords to prevent reuse.
-
What is the stored sample of a biometric factor called?
- A reference template
- A token store
- A biometric password
- An enrollment artifact
-
When might an organization using biometrics choose to allow a higher FRR instead of a higher FAR?
- When security is more important than usability
- When false rejection is not a concern due to data quality
- When the CER of the system is not known
- When the CER of the system is very high
-
Susan is working to improve the strength of her organization’s passwords by changing the password policy. The password system that she is using allows upper- and lower-case letters as well as numbers but no other characters. How much additional complexity does adding a single character to the minimum length of passwords for her organization create?
- 26 times more complex
- 62 times more complex
- 36 times more complex
- 2^62 times more complex
-
Which pair of the following factors are key for user acceptance of biometric identification systems?
- The FAR
- The throughput rate and the time required to enroll
- The CER and the ERR
- How often users must reenroll and the reference profile requirements
Alex is in charge of SAML integration with a major third-party partner that provides a variety of business productivity services for his organization. Using the following diagram and your knowledge of SAML integrations and security architecture design, answer questions 43, 44, and 45.

-
Alex is concerned about eavesdropping on the SAML traffic and also wants to ensure that forged assertions will not be successful. What should he do to prevent these potential attacks?
- Use SAML’s secure mode to provide secure authentication.
- Implement TLS using a strong cipher suite, which will protect against both types of attacks.
- Implement TLS using a strong cipher suite and use digital signatures.
- Implement TLS using a strong cipher suite and message hashing.
-
If Alex’s organization is one that is primarily made up of offsite, traveling users, what availability risk does integration of critical business applications to onsite authentication create and how could he solve it?
- Third-party integration may not be trustworthy; use SSL and digital signatures.
- If the home organization is offline, traveling users won’t be able to access third-party applications; implement a hybrid cloud/local authentication system.
- Local users may not be properly redirected to the third-party services; implement a local gateway.
- Browsers may not properly redirect; use host files to ensure that issues with redirects are resolved.
-
What solution can best help address concerns about third parties that control SSO directs as shown in step 2 in the diagram?
- An awareness campaign about trusted third parties
- TLS
- Handling redirects at the local site
- Implementing an IPS to capture SSO redirect attacks
-
Susan has been asked to recommend whether her organization should use a mandatory access control scheme or a discretionary access control scheme. If flexibility and scalability is an important requirement for implementing access controls, which scheme should she recommend and why?
- MAC, because it provides greater scalability and flexibility because you can simply add more labels as needed
- DAC, because allowing individual administrators to make choices about the objects they control provides scalability and flexibility
- MAC, because compartmentalization is well suited to flexibility and adding compartments will allow it to scale well
- DAC, because a central decision process allows quick responses and will provide scalability by reducing the number of decisions required and flexibility by moving those decisions to a central authority
-
Which of the following tools is not typically used to verify that a provisioning process was followed in a way that ensures that the organization’s security policy is being followed?
- Log review
- Manual review of permissions
- Signature-based detection
- Review the audit trail
-
Lauren needs to send information about services she is provisioning to a third-party organization. What standards-based markup language should she choose to build the interface?
- SAML
- SOAP
- SPML
- XACML
-
During a penetration test, Chris recovers a file containing hashed passwords for the system he is attempting to access. What type of attack is most likely to succeed against the hashed passwords?
- A brute force attack
- A pass-the-hash attack
- A rainbow table attack
- A salt recovery attack
-
Google’s identity integration with a variety of organizations and applications across domains is an example of which of the following?
- PKI
- Federation
- Single sign-on
- Provisioning
-
Lauren starts at her new job and finds that she has access to a variety of systems that she does not need access to to accomplish her job. What problem has she encountered?
- Privilege creep
- Rights collision
- Least privilege
- Excessive privileges
-
When Chris verifies an individual’s identity and adds a unique identifier like a user ID to an identity system, what process has occurred?
- Identity proofing
- Registration
- Directory management
- Session management
-
Jim configures his LDAP client to connect to an LDAP directory server. According to the configuration guide, his client should connect to the server on port 636. What does this indicate to Jim about the configuration of the LDAP server?
- It requires connections over SSL/TLS.
- It supports only unencrypted connections.
- It provides global catalog services.
- It does not provide global catalog services.
-
The X.500 standards cover what type of important identity systems?
- Kerberos
- Provisioning services
- Biometric authentication systems
- Directory services
-
Microsoft’s Active Directory Domain Services is based on which of the following technologies?
- RADIUS
- LDAP
- SSO
- PKI
-
Lauren is responsible for building a banking website. She needs proof of the identity of the users who register for the site. How should she validate user identities?
- Require users to create unique questions that only they will know.
- Require new users to bring their driver’s license or passport in person to the bank.
- Use information that both the bank and the user have such as questions pulled from their credit report.
- Call the user on their registered phone number to verify that they are who they claim to be.
-
By default, in what format does OpenLDAP store the value of the userPassword attribute?
- In the clear
- Salted and hashed
- MD5 hashed
- Encrypted using AES256 encryption
-
A new customer at a bank that uses fingerprint scanners to authenticate its users is surprised when he scans his fingerprint and is logged in to another customer’s account. What type of biometric factor error occurred?
- A registration error
- A Type 1 error
- A Type 2 error
- A time of use, method of use error
-
What type of access control is typically used by firewalls?
- Discretionary access controls
- Rule-based access controls
- Task-based access control
- Mandatory access controls
-
When you input a user ID and password, you are performing what important identity and access management activity?
- Authorization
- Validation
- Authentication
- Login
-
Kathleen works for a data center hosting facility that provides physical data center space for individuals and organizations. Until recently, each client was given a magnetic-strip-based keycard to access the section of the facility where their servers are located, and they were also given a key to access the cage or rack where their servers reside. In the past month, a number of servers have been stolen, but the logs for the passcards show only valid IDs. What is Kathleen’s best option to make sure that the users of the passcards are who they are supposed to be?
- Add a reader that requires a PIN for passcard users.
- Add a camera system to the facility to observe who is accessing servers.
- Add a biometric factor.
- Replace the magnetic stripe keycards with smart cards.
-
Which of the following is a ticket-based authentication protocol designed to provide secure communication?
- RADIUS
- OAuth
- SAML
- Kerberos
-
What type of access control is composed of policies and procedures that support regulations, requirements, and the organization’s own policies?
- Corrective
- Logical
- Compensating
- Administrative
-
In a Kerberos environment, when a user needs to access a network resource, what is sent to the TGS?
- A TGT
- An AS
- The SS
- A session key
-
Which objects and subjects have a label in a MAC model?
- Objects and subjects that are classified as Confidential, Secret, or Top Secret have a label.
- All objects have a label, and all subjects have a compartment.
- All objects and subjects have a label.
- All subjects have a label and all objects have a compartment.
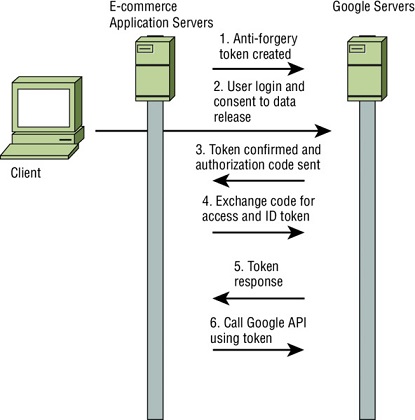
Chris is the identity architect for a growing e-commerce website that wants to leverage social identity. To do this, he and his team intend to allow users to use their existing Google accounts as their primary accounts when using the e-commerce site. This means that when a new user initially connects to the e-commerce platform, they are given the choice between using their Google+ account using OAuth 2.0, or creating a new account on the platform using their own email address and a password of their choice.
Using this information and the following diagram of an example authentication flow, answer questions 66, 67, and 68.
-
When the e-commerce application creates an account for a Google+ user, where should that user’s password be stored?
- The password is stored in the e-commerce application’s database.
- The password is stored in memory on the e-commerce application’s server.
- The password is stored in Google’s account management system.
- The password is never stored; instead, a salted hash is stored in Google’s account management system.
-
Which system or systems is/are responsible for user authentication for Google+ users?
- The e-commerce application
- Both the e-commerce application and Google servers
- Google servers
- The diagram does not provide enough information to determine this.
-
What type of attack is the creation and exchange of state tokens intended to prevent?
- XSS
- CSRF
- SQL injection
- XACML
-
Questions like “What is your pet’s name?” are examples of what type of identity proofing?
- Knowledge-based authentication
- Dynamic knowledge-based authentication
- Out-of-band identity proofing
- A Type 3 authentication factor
-
Lauren builds a table that includes assigned privileges, objects, and subjects to manage access control for the systems she is responsible for. Each time a subject attempts to access an object, the systems check the table to ensure that the subject has the appropriate rights to the objects. What type of access control system is Lauren using?
- A capability table
- An access control list
- An access control matrix
- A subject/object rights management system
-
During a review of support incidents, Ben’s organization discovered that password changes accounted for more than a quarter of its help desk’s cases. Which of the following options would be most likely to decrease that number significantly?
- Two-factor authentication
- Biometric authentication
- Self-service password reset
- Passphrases
-
Brian’s large organization has used RADIUS for AAA services for its network devices for years and has recently become aware of security issues with the unencrypted information transferred during authentication. How should Brian implement encryption for RADIUS?
- Use the built-in encryption in RADIUS.
- Implement RADIUS over its native UDP using TLS for protection.
- Implement RADIUS over TCP using TLS for protection.
- Use an AES256 pre-shared cipher between devices.
-
Jim wants to allow cloud-based applications to act on his behalf to access information from other sites. Which of the following tools can allow that?
- Kerberos
- OAuth
- OpenID
- LDAP
-
Ben’s organization has had an issue with unauthorized access to applications and workstations during the lunch hour when employees aren’t at their desk. What are the best type of session management solutions for Ben to recommend to help prevent this type of access?
- Use session IDs for all access and verify system IP addresses of all workstations.
- Set session time-outs for applications and use password protected screensavers with inactivity time-outs on workstations.
- Use session IDs for all applications, and use password protected screensavers with inactivity time-outs on workstations.
- Set session time-outs for applications and verify system IP addresses of all workstations.
-
Lauren is an information security analyst tasked with deploying technical access controls for her organization. Which of the following is not a logical or technical access control?
- Passwords
- Firewalls
- RAID arrays
- Routers
-
The financial services company that Susan works for provides a web portal for its users. When users need to verify their identity, the company uses information from third-party sources to ask questions based on their past credit reports, such as, “Which of the following streets did you live on in 2007?” What process is Susan’s organization using?
- Identity proofing
- Password verification
- Authenticating with Type 2 authentication factor
- Out-of-band identity proofing
-
The US government CAC is an example of what form of Type 2 authentication factor?
- A token
- A biometric identifier
- A smart card
- A PIV
-
What authentication technology can be paired with OAuth to perform identity verification and obtain user profile information using a RESTful API?
- SAML
- Shibboleth
- OpenID Connect
- Higgins
-
Jim has Secret clearance and is accessing files that use a mandatory access control scheme to apply the Top Secret, Secret, Confidential, and Unclassified label scheme. If his rights include the ability to access all data of his clearance level or lower, what classification levels of data can he access?
- Top Secret and Secret
- Secret, Confidential, and Unclassified
- Secret data only
- Secret and Unclassified
-
The security administrators at the company that Susan works for have configured the workstation she uses to allow her to log in only during her work hours. What type of access control best describes this limitation?
- Constrained interface
- Context-dependent control
- Content-dependent control
- Least privilege
-
When Lauren uses a fingerprint scanner to access her bank account, what type of authentication factor is she using?
- Type 1
- Type 2
- Type 3
- Type 4
-
Which of the following is not an access control layer?
- Physical
- Policy
- Administrative
- Technical
-
Ben uses a software based token which changes its code every minute. What type of token is he using?
- Asynchronous
- Smart card
- Synchronous
- Static
-
What type of token-based authentication system uses a challenge/response process in which the challenge has to be entered on the token?
- Asynchronous
- Smart card
- Synchronous
- RFID
Ben’s organization is adopting biometric authentication for its high-security building’s access control system. Using the following chart, answer questions 85, 86, and 87 about the organization’s adoption of the technology.

-
Ben’s company is considering configuring its systems to work at the level shown by point A on the diagram. To what level is it setting the sensitivity?
- The FRR crossover
- The FAR point
- The CER
- The CFR
-
At point B, what problem is likely to occur?
- False acceptance will be very high.
- False rejection will be very high.
- False rejection will be very low.
- False acceptance will be very low.
-
What should Ben do if the FAR and FRR shown in this diagram does not provide an acceptable performance level for his organization’s needs?
- Adjust the sensitivity of the biometric devices.
- Assess other biometric systems to compare them.
- Move the CER.
- Adjust the FRR settings in software.
-
What LDAP authentication mode can provide secure authentication?
- Anonymous
- SASL
- Simple
- S-LDAP
-
Which of the following Type 3 authenticators is appropriate to use by itself rather than in combination with other biometric factors?
- Voice pattern recognition
- Hand geometry
- Palm scans
- Heart/pulse patterns
-
What danger is created by allowing the OpenID relying party to control the connection to the OpenID provider?
- It may cause incorrect selection of the proper OpenID provider.
- It creates the possibility of a phishing attack by sending data to a fake OpenID provider.
- The relying party may be able to steal the client’s username and password.
- The relying party may not send a signed assertion.
-
Jim is implementing a cloud identity solution for his organization. What type of technology is he putting in place?
- Identity as a Service
- Employee ID as a Service
- Cloud-based RADIUS
- OAuth
-
RAID-5 is an example of what type of control?
- Administrative
- Recovery
- Compensation
- Logical
-
When Alex sets the permissions shown in the following image as one of many users on a Linux server, what type of access control model is he leveraging?

- Role-based access control
- Rule-based access control
- Mandatory access control
- Discretionary access control
-
What open protocol was designed to replace RADIUS—including support for additional commands and protocols, replacing UDP traffic with TCP, and providing for extensible commands—but does not preserve backward compatibility with RADIUS?
- TACACS
- RADIUS-NG
- Kerberos
- Diameter
-
LDAP distinguished names (DNs) are made up of comma-separated components called relative distinguished names (RDNs) that have an attribute name and a value. DNs become less specific as they progress from left to right. Which of the following LDAP DN best fits this rule?
- uid=ben,ou=sales,dc=example,dc=com
- uid=ben,dc=com,dc=example
- dc=com,dc=example,ou=sales,uid=ben
- ou=sales,dc=com,dc=example
-
Susan is troubleshooting Kerberos authentication problems with symptoms including TGTs that are not accepted as valid and an inability to receive new tickets. If the system she is troubleshooting is properly configured for Kerberos authentication, her username and password are correct, and her network connection is functioning, what is the most likely issue?
- The Kerberos server is offline.
- There is a protocol mismatch.
- The client’s TGTs have been marked as compromised and de-authorized.
- The Kerberos server and the local client’s time clocks are not synchronized.
-
Kerberos, KryptoKnight, and SESAME are all examples of what type of system?
- SSO
- PKI
- CMS
- Directory
-
Which of the following types of access controls do not describe a lock?
- Physical
- Directive
- Preventative
- Deterrent
-
What authentication protocol does Windows use by default for Active Directory systems?
- RADIUS
- Kerberos
- OAuth
- TACACS+
-
Alex configures his LDAP server to provide services on 636 and 3269. What type of LDAP services has he configured based on LDAP’s default ports?
- Unsecure LDAP and unsecure global directory
- Unsecure LDAP and secure global directory
- Secure LDAP and secure global directory
- Secure LDAP and unsecure global directory
