Day 4. PC Operating System and Security Troubleshooting
CompTIA A+ 220-902 Exam Topics
![]() Objective 4.1: Given a scenario, troubleshoot PC operating system problems with appropriate tools.
Objective 4.1: Given a scenario, troubleshoot PC operating system problems with appropriate tools.
![]() Objective 4.2: Given a scenario, troubleshoot common PC security issues with appropriate tools and best practices.
Objective 4.2: Given a scenario, troubleshoot common PC security issues with appropriate tools and best practices.
Key Topics
Today we will cover troubleshooting both PC operating systems (OSs) and PC security. We will be looking at OS and security problems, and the tools used to solve them. We also will look at best practices for avoiding problems in the future.
Troubleshooting Operating Systems
So many different things can go wrong in an operating system, so troubleshooting skills should include knowing where to find necessary resources and knowing which tools are available to investigate.
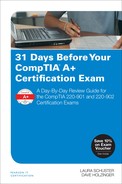
One of the best tools used for troubleshooting the OS is the Event Viewer. It contains the logs for the OS and can provide information on what is happening when errors occur and links to how to fix them.
Event Viewer—Records significant events on the computer and notifies users of any errors as they occur. Events are classified as error, warning, or informational, depending on the severity of the problem (see Figure 4-1).
A circle with an I in it indicates an informational item and indicates normal operations. A yellow triangle with an exclamation point inside indicates a warning. A red circle with an exclamation inside of it indicates an error. These should be dealt with immediately.
The Event Viewer logs most useful for troubleshooting are the following:
![]() Application (program events)—The successful or unsuccessful operation of a program that is built in to Windows
Application (program events)—The successful or unsuccessful operation of a program that is built in to Windows
![]() System—Deals with hardware, device drivers, system files, or services
System—Deals with hardware, device drivers, system files, or services
![]() Security—Holds information for security and related incidents
Security—Holds information for security and related incidents
Troubleshooting Specific OS Errors
Problems with the OS can be varied. Microsoft has included tools that will assist in diagnosing and solving these problems. The following are common problems and how to solve them.
Service fails to start—An error message may appear that indicates a problem with a service that has failed to load. In this case, go into the services utility and check that any associated services are started. Try manually starting or stopping and then restarting the service. Try to look at processes on which the service depends to see whether they have been started.
Compatibility errors—This often happens when an older application does not work properly after a Windows upgrade. To run a program in compatibility mode, right-click the program, select its properties, select the compatibility tab, and change how the program is run.
Windows 8/8/1 also has a new utility called Program Compatibility Troubleshooter. In the search box, type run programs. Select Run Programs Made for Previous Versions of Windows, and then select Next. Choose the program you want to fix or select Not Listed. Follow the instructions in the troubleshooter.
In Linux, use the service command at the terminal to view, start, and stop services. In OS X, you can find the Services submenu in the Finder by using the application name drop-down menu item.
Slow system performance—First, verify that the problem is the computer system and not a slow Internet or network connection. It is easy to mistake one for the other. Check that the hard drive has enough free space. Check for programs and add-ons that might have been loaded into the web browsers. Make sure that all the programs are up to date with the latest versions, updates, and especially any security patches. Malicious software can be a common cause of slow system performance, so be sure to run the antivirus software as well.
Troubleshooting Specific Booting Errors
Windows comes with tools designed to perform self-repairs if the OS senses a boot problem. Windows 7 had the Startup Repair tool, and Windows 8 has the Windows Automatic Repair utility. When a problem with booting is detected, these utilities launch a diagnostic-based troubleshooter.
Failure to boot—A boot problem is a critical issue. Fortunately, some type of error message typically appears and will help you troubleshoot. Bootmgr is the first file that gets loaded into memory and executes. Windows Vista, 7, and 8 use the Bootmgr and the Windows Boot Loader during startup. If any of the boot files are corrupted or missing, Windows will fail to load.
The following tools are used to fix boot failures:
![]() Boot from the Windows installation disk, and select Repair Your Computer to access System Recovery Options.
Boot from the Windows installation disk, and select Repair Your Computer to access System Recovery Options.
![]() Use Startup Repair.
Use Startup Repair.
![]() To repair the master boot record, at the command prompt type bootrec /fixmbr.
To repair the master boot record, at the command prompt type bootrec /fixmbr.
![]() To write a new boot sector to a system partition, at the command prompt type bootrec /fixboot.
To write a new boot sector to a system partition, at the command prompt type bootrec /fixboot.
![]() To scan all disks for Windows installations and choose which to add to the boot configuration store, at the command prompt type bootrec /RebuildBcd.
To scan all disks for Windows installations and choose which to add to the boot configuration store, at the command prompt type bootrec /RebuildBcd.
BSOD/Stop Errors—If the computer has crashed and a blue screen of death (BSOD) appears, most likely there will be some type of error code. Windows keeps logs of any stop errors in the Event Viewer, which can give some hint on where to look for problems. Frequent BSODs can indicate a sign of hardware problems, especially RAM. A spontaneous shutdown and restart also is indicative of a hardware problem or virus.
The following tools are used to fix a BSOD/Stop error:
![]() Reboot into Safe Mode.
Reboot into Safe Mode.
![]() Use the Event Viewer System log.
Use the Event Viewer System log.
![]() Use the Recovery Environment to run the Memory Diagnostic tool.
Use the Recovery Environment to run the Memory Diagnostic tool.
![]() If you have not logged in to the system in Vista/7, you can press F8 and select Last Known Good Configuration to get back to a previous configuration.
If you have not logged in to the system in Vista/7, you can press F8 and select Last Known Good Configuration to get back to a previous configuration.
![]() Use System Restore.
Use System Restore.
![]() Use antivirus software installed on a bootable device to repair boot viruses.
Use antivirus software installed on a bootable device to repair boot viruses.
Missing or corrupted NTLDR, Boot.ini, OS, or graphical interface—These errors can be caused by file corruption or accidental deletion. They also can be caused by problems in the BIOS/UEFI, if Windows is not up to date, or if too many files are in the root folder.
Tools to fix a missing or corrupted NTLDR, Boot.ini, OS, or the graphical interface include the following:
![]() The System Recovery option, Startup repair.
The System Recovery option, Startup repair.
![]() Run the chkdsk /F utility from the command prompt.
Run the chkdsk /F utility from the command prompt.
![]() Run the bootrec.exe utility to rebuild the boot configuration data (bcd) file at the command prompt.
Run the bootrec.exe utility to rebuild the boot configuration data (bcd) file at the command prompt.
![]() Run the system file checker tool sfc at the command prompt.
Run the system file checker tool sfc at the command prompt.
Kernel panic—A kernel panic happens as the result of a low-level error from which an OS cannot recover. It is similar to the Windows BSOD, and it can cause an immediate reboot or a screen filled with errors. On OS X, the computer restarts without warning followed by a brief message indicating that the computer needed to restart. On Linux, the system might continue to run but be unstable.
Tools to fix a kernel panic include the following:
![]() Boot to rescue media.
Boot to rescue media.
![]() Use other third-party boot repair tools such as the Ubuntu Boot Repair utility.
Use other third-party boot repair tools such as the Ubuntu Boot Repair utility.
![]() If it happens only once, a reboot usually can fix it. For a Mac, hold down the power button for several seconds to turn it off, and then press it again to turn it back on.
If it happens only once, a reboot usually can fix it. For a Mac, hold down the power button for several seconds to turn it off, and then press it again to turn it back on.
![]() For a Linux machine, just do a hard boot of the machine.
For a Linux machine, just do a hard boot of the machine.
![]() Restart a Mac in safe boot by holding down the Shift key until the gray Apple logo appears. This can temporarily disable software that could cause problems as well as runs some cleanup processes.
Restart a Mac in safe boot by holding down the Shift key until the gray Apple logo appears. This can temporarily disable software that could cause problems as well as runs some cleanup processes.
![]() Update software and firmware.
Update software and firmware.
![]() Make sure the disk has at least 10GB of free space.
Make sure the disk has at least 10GB of free space.
![]() Check peripherals and RAM for defective parts.
Check peripherals and RAM for defective parts.
Operating system cannot be found—An error that the OS cannot be found can indicate an issue with the BIOS or UEFI configuration, a hardware problem, or that the master boot record (MBR) is corrupted or missing. It also can be the result of incorrect BIOS/UEFI boot order settings or a disc loaded in a bootable location without an OS on it.
Improper shutdown—Any time an improper shutdown of the system occurs, there is a risk of data corruption. If you experience problems after an improper shutdown, use tools similar to those used for file corruption.
Tools used to fix improper shutdown include the following:
![]() Check with Event Viewer to see whether there is an error.
Check with Event Viewer to see whether there is an error.
![]() Run the sfc program to resolve issues with corrupted files.
Run the sfc program to resolve issues with corrupted files.
Spontaneous shutdown/restart—This problem causes the computer to continuously reboot. First, eliminate hardware problems. It can be an overheated element inside the computer or a hardware driver issue. Update all critical system drivers, paying attention to the video card, motherboard, and chipset drivers. Try to get into Windows using Safe Mode. Once there, look for errors in the Event Viewer. Sometimes a problem like this can be caused by viruses or other malware.
Linux boot problems—In Linux, the Linux Loader (LILO) and the GRand Unified Bootloader (GRUB) both do the same job as the Windows Boot Manager (bootmgr). A boot problem can happen after a kernel upgrade, a disk swap, or any other system change. GRUB starts with a text-mode menu that displays boot options unless it has been hidden. Options on the menu enable the loading of previous versions of Linux, a recovery mode, and a memory test option.
Troubleshooting Hardware Issues
The best tool available in Windows Vista through Windows 8.1 for dealing with hardware is the Device Manager.
Device Manager—It detects whether a device is malfunctioning or has some type of error by displaying a small, yellow triangle with an exclamation mark inside. A yellow question mark indicates that the computer is unable to start that piece of hardware. A red X icon beside the name of the device can indicate a device is no longer working, and a downward-pointing error on a device means it has been disabled. Problems in the Device Manager can be solved by installing new drivers, changing configuration settings, or removing and reinstalling the device. Figure 4-2 displays the Device Manager with a yellow triangle and exclamation point indicating a problem with a device (note the PCI Simple Communications Controller).
Device fails to start—This usually indicates a hardware problem. Use the Device Manager to check for issues. Reinstall the device drivers or get an updated driver for the problem device. Sometimes there are error messages that you can research and fix.
Peripheral stops working—If the problem is a peripheral, try disconnecting and reconnecting it, or download the latest driver and perform a full reinstall.
Multiple monitor misalignment/orientation—Alignment happens in the Screen Resolution tool. With multiple monitors, you can drag and drop the appearance of the displays. If the primary monitor is placed at the bottom, you will get a bottom-to-top orientation. If you place the primary monitor on top, you will get a top-to-bottom orientation. Putting the primary monitor on the left will provide a left-to-right orientation, and putting it on the right will provide a right-to-left orientation. When you are satisfied with the setup, click the Apply button to save the changes.
Figure 27-2, shown earlier in the book, displays a multiple-monitor configuration in Windows 8.
Troubleshooting Specific Issues with the File System
Problems with the file system usually require disk management tools. These tools provide help diagnosing problems with drives, partitions, formats, errors, viruses, and corruption.
Missing dll message—Missing dll messages appear when a dynamic link library file is missing. It can be the result of another program that overwrote it or corruption. Dlls have different versions, and an older version can become a problem if it malfunctions.
To fix missing dll file problems, try the following:
![]() Run the sfc utility at the command prompt.
Run the sfc utility at the command prompt.
![]() Run the chkdsk utility at the command prompt.
Run the chkdsk utility at the command prompt.
![]() Run the First Aid utility in OS X at the terminal prompt.
Run the First Aid utility in OS X at the terminal prompt.
![]() Run the fsck utility on OS X or a Linux machine at the terminal prompt.
Run the fsck utility on OS X or a Linux machine at the terminal prompt.
![]() To re-register dll files, run the tool called regsvr32. It will register the dll as command components in the registry.
To re-register dll files, run the tool called regsvr32. It will register the dll as command components in the registry.
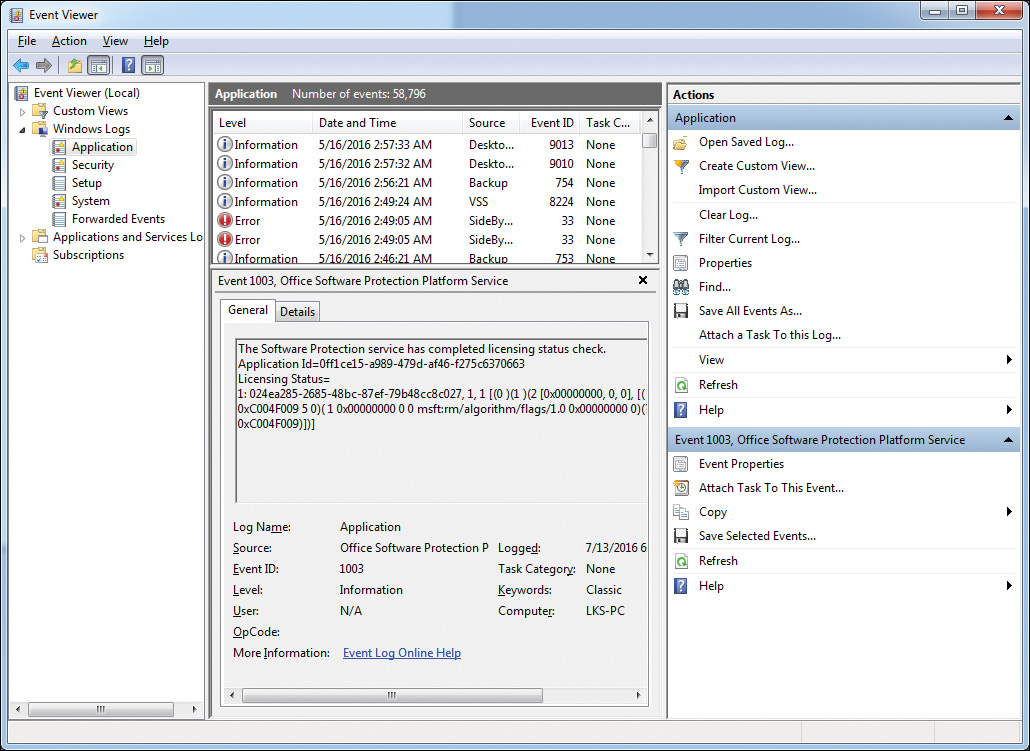
File fails to open—A file with a specific file extension can be opened only by the program(s) designed to open it. Using the wrong program can cause an error message that the file has failed to open. Changes can be made to the type of program used to open files, and sometimes other software can be installed that will recognize the file type. Figure 4-3 displays the file association utility.
Bootup Troubleshooting Tools
When the computer fails to boot, tools are available that are designed specifically for diagnosing and troubleshooting the problem. Some of these tools also are used for other problems, but when facing a booting issue, these will prove to be the most helpful:
Msconfig—This utility can help troubleshoot problems from OS startup to application and services problems. The following tabs are available:
![]() General tab—Use this option to change how Windows boots up:
General tab—Use this option to change how Windows boots up:
![]() Diagnostic startup can help rule out basic Windows files as the source of the problem.
Diagnostic startup can help rule out basic Windows files as the source of the problem.
![]() Selective startup allows basic services and drivers and only those selected services and startup programs to be used during bootup.
Selective startup allows basic services and drivers and only those selected services and startup programs to be used during bootup.
![]() Boot tab—Provides multiple booting options in different environments.
Boot tab—Provides multiple booting options in different environments.
![]() Services tab—Lists all services that are started when the computer boots, along with their current status.
Services tab—Lists all services that are started when the computer boots, along with their current status.
![]() Startup tab—Lists applications that run when the computer starts, along with the name of the publisher, the path to the executable file, and the location of the registry key.
Startup tab—Lists applications that run when the computer starts, along with the name of the publisher, the path to the executable file, and the location of the registry key.
![]() Tools tab—Provides a list of diagnostic tools and other advanced tools.
Tools tab—Provides a list of diagnostic tools and other advanced tools.
Figure 4-4 displays the optional tabs available in the Msconfig utility.
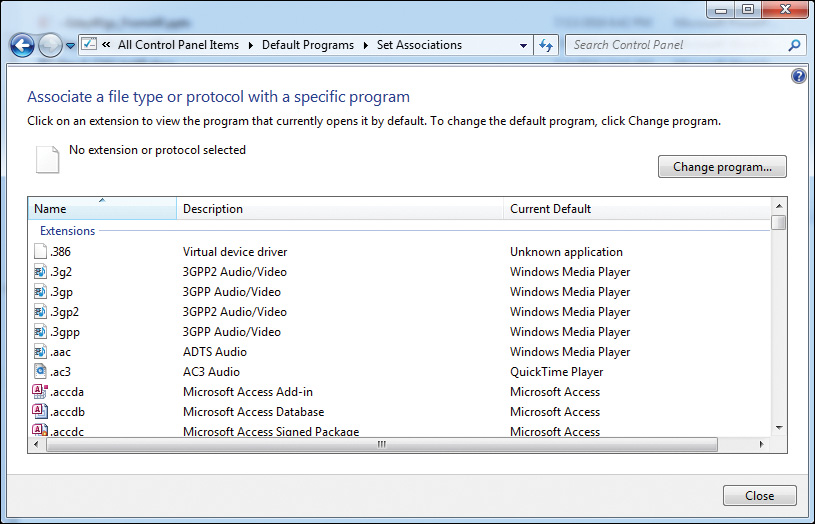
Recovery Console—The System Recovery Options menu contains multiple tools that can help Windows recover from serious errors or be used to recover access to a working copy of the OS. Access can be through a reboot and pressing F8 during the startup of Windows, or it can be accessed by booting to the installation media and selecting Recovery. After reaching the menu, select one of the following:
![]() Startup Repair—Fixes problems such as missing or damaged system files; it scans the computer and tries to fix it.
Startup Repair—Fixes problems such as missing or damaged system files; it scans the computer and tries to fix it.
![]() System Restore—Restores the computer system files to an earlier point in time without affecting current data files. If used, the changes cannot be undone.
System Restore—Restores the computer system files to an earlier point in time without affecting current data files. If used, the changes cannot be undone.
![]() System Image Recovery—Requires a system image (a personalized backup of the partition containing Windows) to have been created previously.
System Image Recovery—Requires a system image (a personalized backup of the partition containing Windows) to have been created previously.
![]() Windows Memory Diagnostic—Scans the memory for errors.
Windows Memory Diagnostic—Scans the memory for errors.
![]() Command Prompt—Used to run command-line tools for diagnosing and troubleshooting problems.
Command Prompt—Used to run command-line tools for diagnosing and troubleshooting problems.
See Figure 4-5 for a view of Windows 7 System Recovery Options.
Advanced Startup for Windows 8/8.1—Part of the Windows Recovery Environment (WinRE) that is accessed by pressing F8 during the boot. You must select the Troubleshoot icon, and then from the troubleshooting window select Advanced Options. The following are the available tools and their capabilities:
![]() System Restore—Restores the OS to an earlier created restore point.
System Restore—Restores the OS to an earlier created restore point.
![]() System Image Recovery—Restores using a system image file.
System Image Recovery—Restores using a system image file.
![]() Automatic Repair—Scans the system and tries to repair any issues preventing Windows from booting properly.
Automatic Repair—Scans the system and tries to repair any issues preventing Windows from booting properly.
![]() Command Prompt—Opens a Recovery Environment command prompt.
Command Prompt—Opens a Recovery Environment command prompt.
![]() UEFI Firmware Settings—Shown only if UEFI is enabled; use it to change any UEFI settings.
UEFI Firmware Settings—Shown only if UEFI is enabled; use it to change any UEFI settings.
![]() Windows Startup Settings—Enable Safe Mode and disable automatic restart after failure to see error messages.
Windows Startup Settings—Enable Safe Mode and disable automatic restart after failure to see error messages.
Figure 12-7, earlier in the book, provides a view of the Windows 8 advanced startup options.
Windows Recovery Environment—Built on the Windows Pre-installation Environment, it can diagnose and solve startup problems or recover the OS. Users can access Windows RE through the Boot Options menu, which can be launched in several ways. By default, Windows RE is preloaded into Windows 8.1. Here are the tools provided in Windows RE:
![]() Automatic repair and other troubleshooting tools (Startup Repair)—Windows will automatically turn to this environment if the computer fails to start.
Automatic repair and other troubleshooting tools (Startup Repair)—Windows will automatically turn to this environment if the computer fails to start.
![]() Pushbutton reset (Windows 8, 8.1 only)—Enables a user to repair his/her own PC while preserving the data and important customizations without having to back up first.
Pushbutton reset (Windows 8, 8.1 only)—Enables a user to repair his/her own PC while preserving the data and important customizations without having to back up first.
Manual troubleshooting—Select the command prompt option in the System Recovery Options menu. The bootrec.exe tool is used to repair or re-create a Windows boot configuration data (BCD) file. The BCD defines how the boot menu is configured and how the OS is started in Windows. The following are options used with the bootrec tool to repair boot problems:
![]() Boot Configuration Data store—This can be rebuilt by running the following command at the command prompt: bootrec /rebuildbcd.
Boot Configuration Data store—This can be rebuilt by running the following command at the command prompt: bootrec /rebuildbcd.
![]() Run bootrec /fixmbr—This writes an MBR to the system partition. It will not overwrite the existing partition table.
Run bootrec /fixmbr—This writes an MBR to the system partition. It will not overwrite the existing partition table.
![]() Run bootrec /fixboot—This option writes a new boot sector to the system partition by using a boot sector that is compatible. Use this option if the boot sector was replaced with a nonstandard Windows version, the boot sector is damaged, or an earlier Windows version was installed after a later Windows install.
Run bootrec /fixboot—This option writes a new boot sector to the system partition by using a boot sector that is compatible. Use this option if the boot sector was replaced with a nonstandard Windows version, the boot sector is damaged, or an earlier Windows version was installed after a later Windows install.
![]() Run bootrec /ScanOS—Scans all disks for Windows 7, 8, or 8.1 installations when an installed OS is not available or included in the BCD.
Run bootrec /ScanOS—Scans all disks for Windows 7, 8, or 8.1 installations when an installed OS is not available or included in the BCD.
Note
The bootrec /fixmbr is not required for GPT-based systems because they do not use a master boot record.
Preinstallation environments—The Windows preinstallation environment (Windows PE) is a minimal Win32 OS with limited services, built on the Windows kernel. It is used to prepare a computer for the Windows installation, so that a preconfigured image of a full install from a network server can be copied down to the drive. It can be used to troubleshoot and recover a copy of Windows that did not start by providing access to the drive with the system files.
Emergency repair disk (system repair disc)—If the system does not start and neither Safe Mode nor the Recovery Console has helped, try using the emergency Repair Disk option found in Backup. Note that this disk should have been prepared beforehand.
Factory recovery partition—The factory recovery partition is worth mentioning here because it is a way to get back to a clean install without having to diagnose or troubleshoot the system. It is not based on the OS, but on the model of computer being used. Some computer and laptop manufacturers provide this service, and some do not.
Linux and OS X Bootup Troubleshooting Tools
Some versions of Linux have boot repair utilities, and others need a third-party program to fix problems. Fortunately, the Linux community has multiple resources available for supporting either option and assisting with troubleshooting efforts. There are no Safe Mode or Automatic Repair tools for Linux, but there are some procedures that will help.
Try booting the computer while holding down the Shift key. A menu with a list of OSs should display. If the boot loader cannot be accessed, then it must be repaired by either booting to the installation disc or using another Linux system to repair it. Some versions of Linux have an option to create a boot-repair-disc.
Common symptoms for issues booting into OS X is the proprietary crash screen with a pinwheel on it. It can be caused by insufficient memory, a slow processor, or application errors. The fastest quick fix is a reboot. Try holding down the Command+R keys while booting to access recovery options. Boot to the installation disc while holding down the C key to boot into a diagnostic mode.
If there is a flashing question mark or a circle/slash, OS X cannot find a valid startup disk. This can require a reinstall. If the Apple Logo appears, OS X has found the system disk and the OS has begun loading. If it stalls at the Apple logo or the logo with a spinning gear, it is a corrupt installation. To start OS X in Safe Mode, hold down the Shift key at startup.
![]() Activity 4-1: Match the Proper Boot Repair Option to Its Description
Activity 4-1: Match the Proper Boot Repair Option to Its Description
Refer to the Digital Study Guide to complete this activity.
Command-Line Repair Tools
If the GUI is not available, sometimes the only option is to use the command line. Some commands provide switches that modify how the command’s results are displayed. The following are those that are most commonly used to fix problems with the OS:
![]() Chkdsk—Checks a drive for errors, fixes some issues like lost or cross-linked files, and displays a status report.
Chkdsk—Checks a drive for errors, fixes some issues like lost or cross-linked files, and displays a status report.
![]() Format—Used to format both magnetic and solid-state media for a file system.
Format—Used to format both magnetic and solid-state media for a file system.
![]() Bootrec—Used to repair or re-create a Windows boot configuration data file.
Bootrec—Used to repair or re-create a Windows boot configuration data file.
![]() Convert—Enables the conversion of a volume from one type of file system to another (for example, FAT32 to NTFS)
Convert—Enables the conversion of a volume from one type of file system to another (for example, FAT32 to NTFS)
![]() Diskpart—The command-line version of the Windows Disk Management program that can work with volumes, drive letters, and partitions.
Diskpart—The command-line version of the Windows Disk Management program that can work with volumes, drive letters, and partitions.
![]() Defrag—The command-line version of the Disk Defragmenter program. The -a option is used to analyze the drive if needed: defrag -a.
Defrag—The command-line version of the Disk Defragmenter program. The -a option is used to analyze the drive if needed: defrag -a.
![]() Copy—Copies files from one location to another.
Copy—Copies files from one location to another.
![]() Xcopy—Used to copy large amounts of data from one location to another, it is more robust than the copy command because it can copy empty folders.
Xcopy—Used to copy large amounts of data from one location to another, it is more robust than the copy command because it can copy empty folders.
![]() Robocopy—A directory replication tool, it can mirror complete directory trees from one computer to another. The advantage of this tool over xcopy is that it can recover from interruptions.
Robocopy—A directory replication tool, it can mirror complete directory trees from one computer to another. The advantage of this tool over xcopy is that it can recover from interruptions.
![]() Expand—If a file cannot be copied, it may be able to be extracted from the installation disc by expanding it out of the installation files.
Expand—If a file cannot be copied, it may be able to be extracted from the installation disc by expanding it out of the installation files.
![]() Tasklist—Shows all processes running and is similar to the Processes tab of the Task Manager. It will show the process identification number (PID) and the memory usage of each process.
Tasklist—Shows all processes running and is similar to the Processes tab of the Task Manager. It will show the process identification number (PID) and the memory usage of each process.
![]() Taskkill—Shuts down a process.
Taskkill—Shuts down a process.
![]() Shutdown—Used to turn off the computer, restart it, send it to hibernate mode, or log a user off the computer.
Shutdown—Used to turn off the computer, restart it, send it to hibernate mode, or log a user off the computer.
![]() System File Checker (sfc.exe)—Use this command-line utility to scan for missing or corrupted Windows system files and to restore them.
System File Checker (sfc.exe)—Use this command-line utility to scan for missing or corrupted Windows system files and to restore them.
![]() Activity 4-2: Match the Proper Command-Line Tool to Its Description
Activity 4-2: Match the Proper Command-Line Tool to Its Description
Refer to the Digital Study Guide to complete this activity.
Common PC Security Issues
Threats can come from outside the organization and from within it. To troubleshoot common PC security issues, we need to understand how problems manifest themselves; then we can look at what can be done to prevent problems in the future.
It isn’t always obvious when a system is infected with malware. Each infection can act differently. Many times the slowness of the system is the first indication there might be an infection. Sometimes it is more obvious, like when pop-ups appear, the home page on the browser is rerouted, or applications and the OS lock up or shut down unexpectedly.
These are some common symptoms that indicate a security breach caused by malware:
![]() Pop-ups—Windows that appear automatically without permission, usually advertising something.
Pop-ups—Windows that appear automatically without permission, usually advertising something.
![]() Browser redirection—The home page or a search is redirected to a page not chosen by the user.
Browser redirection—The home page or a search is redirected to a page not chosen by the user.
![]() Security alerts—These can be genuine Windows messages warning the user of the status of the firewall, antivirus settings, or other Security Center/Action Center settings; it also can indicate an infection designed to trick a user into installing rogue security software.
Security alerts—These can be genuine Windows messages warning the user of the status of the firewall, antivirus settings, or other Security Center/Action Center settings; it also can indicate an infection designed to trick a user into installing rogue security software.
![]() Slow performance—This can be a common occurrence that can be caused by multiple problems such as a full hard drive, outdated drivers, startup programs, and services running that are not needed. It is also one of the first major indications that the computer is infected by malware.
Slow performance—This can be a common occurrence that can be caused by multiple problems such as a full hard drive, outdated drivers, startup programs, and services running that are not needed. It is also one of the first major indications that the computer is infected by malware.
![]() Internet connectivity issues—Assuming this is not a hardware issue, this can be caused by incorrect TCP/IP or network configuration settings, disconnected wires, websites with problems or that have gone down, ISPs that are down, or malware.
Internet connectivity issues—Assuming this is not a hardware issue, this can be caused by incorrect TCP/IP or network configuration settings, disconnected wires, websites with problems or that have gone down, ISPs that are down, or malware.
![]() PC/OS lock-ups—This type of problem can be caused by a lack of memory, a bad power supply, corrupted system files, or a virus.
PC/OS lock-ups—This type of problem can be caused by a lack of memory, a bad power supply, corrupted system files, or a virus.
![]() Application crash—Applications crash for a variety of reasons; sometimes just poorly written code, and other times a virus, corrupted files, or authorization settings can be the problem.
Application crash—Applications crash for a variety of reasons; sometimes just poorly written code, and other times a virus, corrupted files, or authorization settings can be the problem.
![]() OS update failure—This happens when the automated Windows Update utility fails. Microsoft has a Windows Update troubleshooter download that can be used to fix problems.
OS update failure—This happens when the automated Windows Update utility fails. Microsoft has a Windows Update troubleshooter download that can be used to fix problems.
![]() Rogue antivirus—This is an instance when a user is frightened into installing software by notifications of a fake virus alert. It usually calls for some type of action, such as paying a fee or downloading software containing malware.
Rogue antivirus—This is an instance when a user is frightened into installing software by notifications of a fake virus alert. It usually calls for some type of action, such as paying a fee or downloading software containing malware.
![]() Spam—Using email to send unsolicited messages, especially advertising, to as many users as possible.
Spam—Using email to send unsolicited messages, especially advertising, to as many users as possible.
![]() Renamed or disappearing system files—If this happens without the user’s permission, it is almost always a virus.
Renamed or disappearing system files—If this happens without the user’s permission, it is almost always a virus.
![]() File permission changes—This is usually caused by a virus and only requires scanning the drive or following a trusted website dedicated to assisting users with malware fixes.
File permission changes—This is usually caused by a virus and only requires scanning the drive or following a trusted website dedicated to assisting users with malware fixes.
![]() Hijacked email—When this happens, contacts in a user’s address book start receiving emails and advertisements, automated replies from unknown sent emails are received, the inbox is suddenly empty, no access to the account is available, the user can’t retrieve messages, or contacts have been deleted. If possible, change the email password and then notify everyone on the contact list. Other repairs may be run through utilities available from the email program itself, or at the server level, which is beyond the scope of this book.
Hijacked email—When this happens, contacts in a user’s address book start receiving emails and advertisements, automated replies from unknown sent emails are received, the inbox is suddenly empty, no access to the account is available, the user can’t retrieve messages, or contacts have been deleted. If possible, change the email password and then notify everyone on the contact list. Other repairs may be run through utilities available from the email program itself, or at the server level, which is beyond the scope of this book.
![]() Invalid certificates—This can produce errors that state invalid or expired security certificate warnings informing you that the connection is untrusted. It can be caused by a virus, by problems on the computer, or a problem with the website address. Because certificates are issued to be applied during a given date range, an incorrect date also can cause this problem.
Invalid certificates—This can produce errors that state invalid or expired security certificate warnings informing you that the connection is untrusted. It can be caused by a virus, by problems on the computer, or a problem with the website address. Because certificates are issued to be applied during a given date range, an incorrect date also can cause this problem.
Tools Used to Combat Malware
Many third-party software utilities can provide protection and remediation from the threat of malware. General categories of these tools are as follows:
![]() Antivirus software—Provides prevention and removal of most viruses and malware by scanning files and folders looking for certain patterns that indicate the presence of malicious software; it might include website and email blocking.
Antivirus software—Provides prevention and removal of most viruses and malware by scanning files and folders looking for certain patterns that indicate the presence of malicious software; it might include website and email blocking.
![]() Anti-malware software—Another name for antivirus software, although it can indicate software that scans for all types of infections.
Anti-malware software—Another name for antivirus software, although it can indicate software that scans for all types of infections.
![]() Recovery console—Accessed by booting to the installation DVD, it allows a user to perform maintenance and recovery tasks on the computer.
Recovery console—Accessed by booting to the installation DVD, it allows a user to perform maintenance and recovery tasks on the computer.
![]() Terminal—Included in OS X and Linux OSs, it provides access to the command-line environment.
Terminal—Included in OS X and Linux OSs, it provides access to the command-line environment.
![]() System Restore/Snapshot—A feature in Windows to revert the computer to a previous state in time to recover from a serious error. OS X uses the Time Machine backup program that provides the option to restore a drive by selecting a “snapshot” from a timeline. This is the OS X version of the System Restore utility. Linux does not have a system restore utility loaded natively.
System Restore/Snapshot—A feature in Windows to revert the computer to a previous state in time to recover from a serious error. OS X uses the Time Machine backup program that provides the option to restore a drive by selecting a “snapshot” from a timeline. This is the OS X version of the System Restore utility. Linux does not have a system restore utility loaded natively.
![]() Preinstallation environments—Also known as Windows PE, it provides minimal file system, device drivers, and network support.
Preinstallation environments—Also known as Windows PE, it provides minimal file system, device drivers, and network support.
![]() Event Viewer—Provides access to log files such as the system, application, and security logs.
Event Viewer—Provides access to log files such as the system, application, and security logs.
![]() Refresh/restore—Used in Windows 8 and later OSs, it can refresh, reset, or restore the computer after an error.
Refresh/restore—Used in Windows 8 and later OSs, it can refresh, reset, or restore the computer after an error.
![]() MSCONFIG/Safe Boot—Msconfig has an option that can be used to boot to Safe Mode from within the OS.
MSCONFIG/Safe Boot—Msconfig has an option that can be used to boot to Safe Mode from within the OS.
Best Practice Procedures for Malware Removal
After malware has been identified, it is important to quarantine the infected system. Immediately remove it from the network so no other machine can be infected. To follow best practice procedures for malware removal, take the following steps:
1. Identify malware symptoms.
2. Quarantine the infected system.
3. Disable system restore (in Windows).
4. Remediate the infected systems:
![]() Update the antimalware software.
Update the antimalware software.
![]() Perform scan and removal techniques (safe mode, preinstallation environment).
Perform scan and removal techniques (safe mode, preinstallation environment).
5. Schedule scans and run updates.
6. Enable system restore and create a restore point (in Windows).
7. Educate the end user on safe computing practices.
![]() Activity 4-3: Match the Proper Malware Removal Step to Its Description
Activity 4-3: Match the Proper Malware Removal Step to Its Description
Refer to the Digital Study Guide to complete this activity.

![]() Check Your Understanding
Check Your Understanding
Refer to the Digital Study Guide to take a quiz covering the content of this day.