Chapter 7
Practice Exam 2
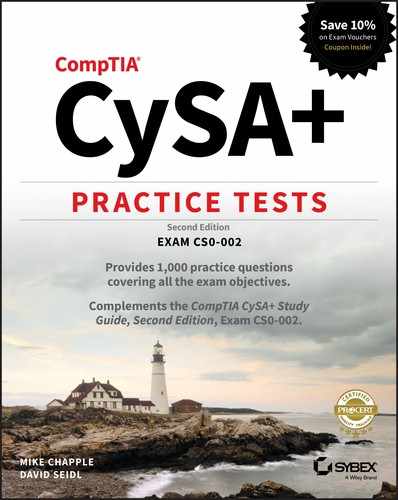
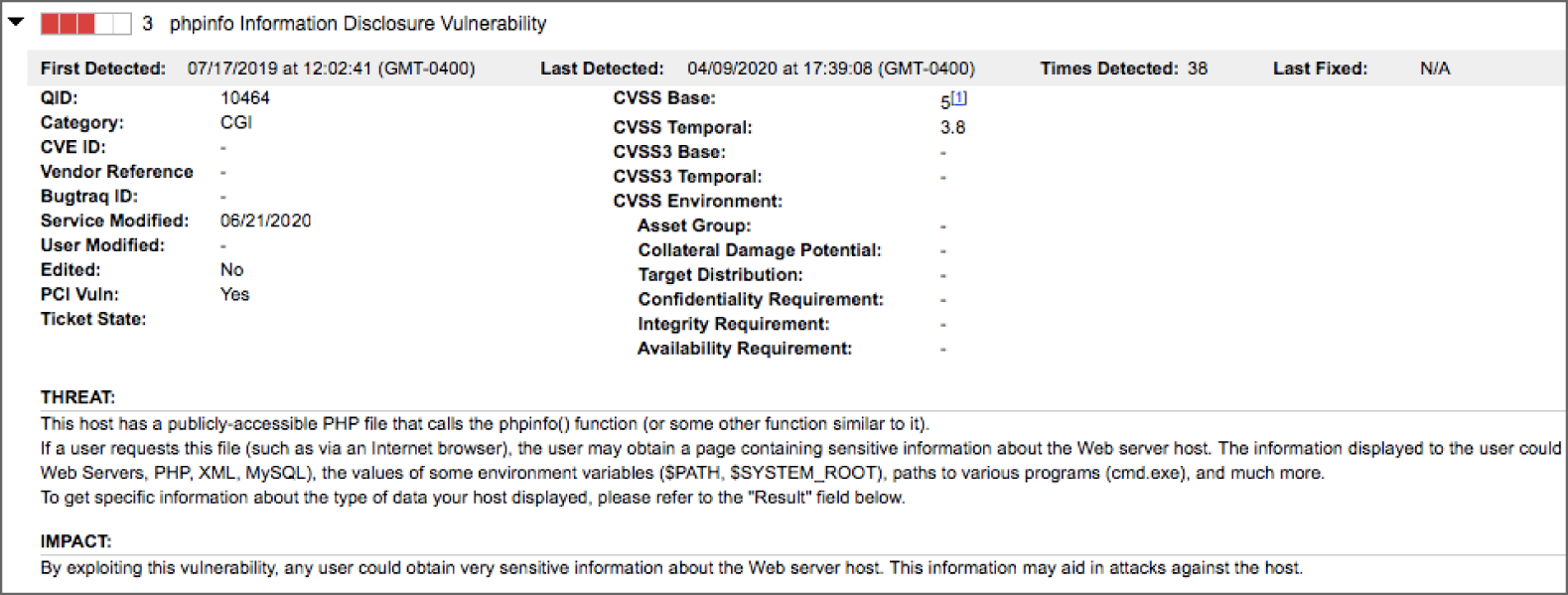
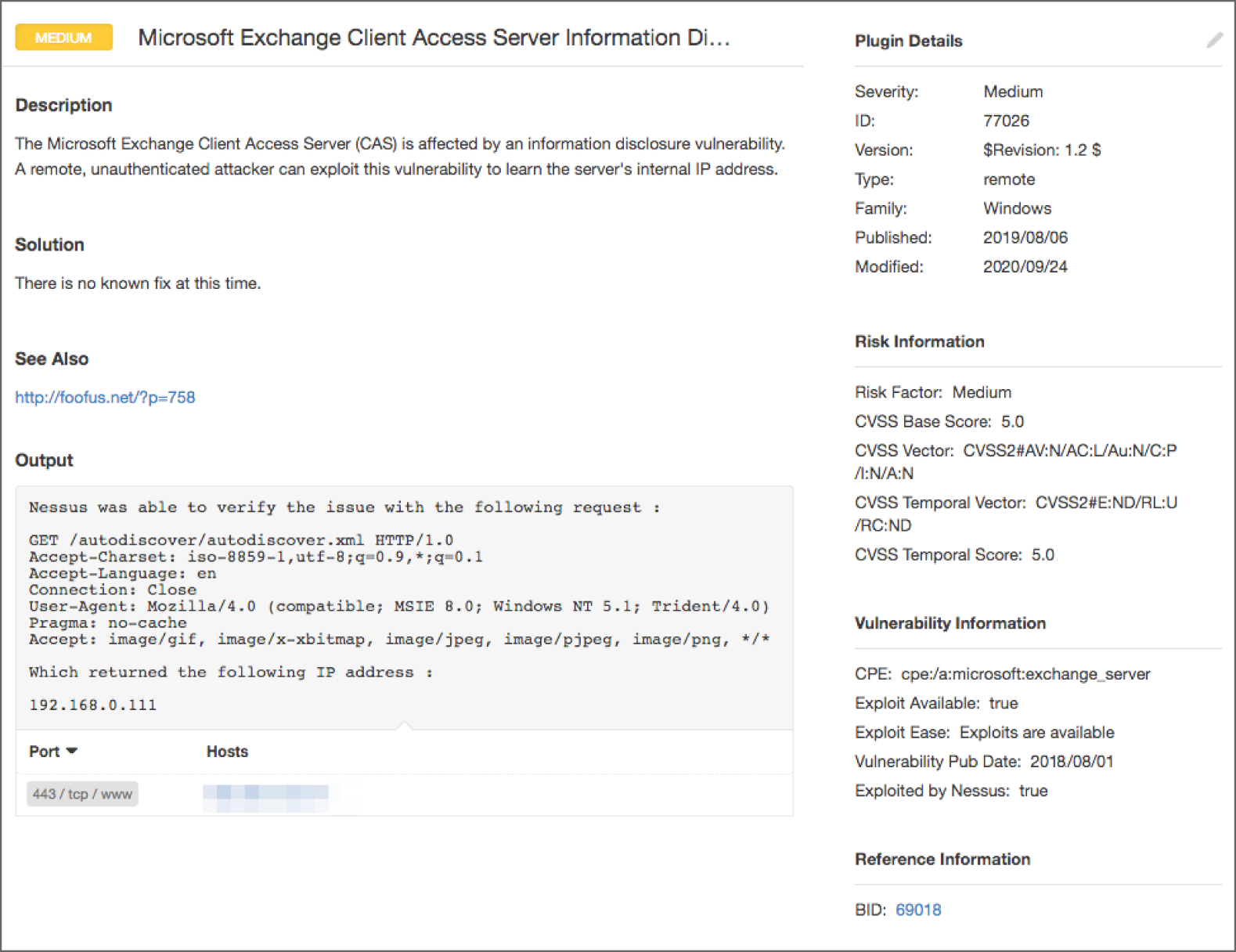
- Ty is reviewing the scan report for a Windows system joined to his organization's domain and finds the vulnerability shown here. What should be Ty's most significant concern related to this vulnerability?
- The presence of this vulnerability indicates that an attacker may have compromised his network.
- The presence of this vulnerability indicates a misconfiguration on the target server.
- The presence of this vulnerability indicates that the domain security policy may be lacking appropriate controls.
- The presence of this vulnerability indicates a critical flaw on the target server that must be addressed immediately.
- During an incident investigation, Chris discovers that attackers were able to query information about his routers and switches using SNMP. Chris finds that his routers used “public” and “private” as their community strings. Which of the following is not an appropriate action to take to help secure SNMP in Chris's organization?
- Add complexity requirements to the SNMP community string.
- Enable and configure SNMP v2c.
- Enable and require TLS setting for SNMP.
- Apply different SNMP community strings to devices with different security levels.
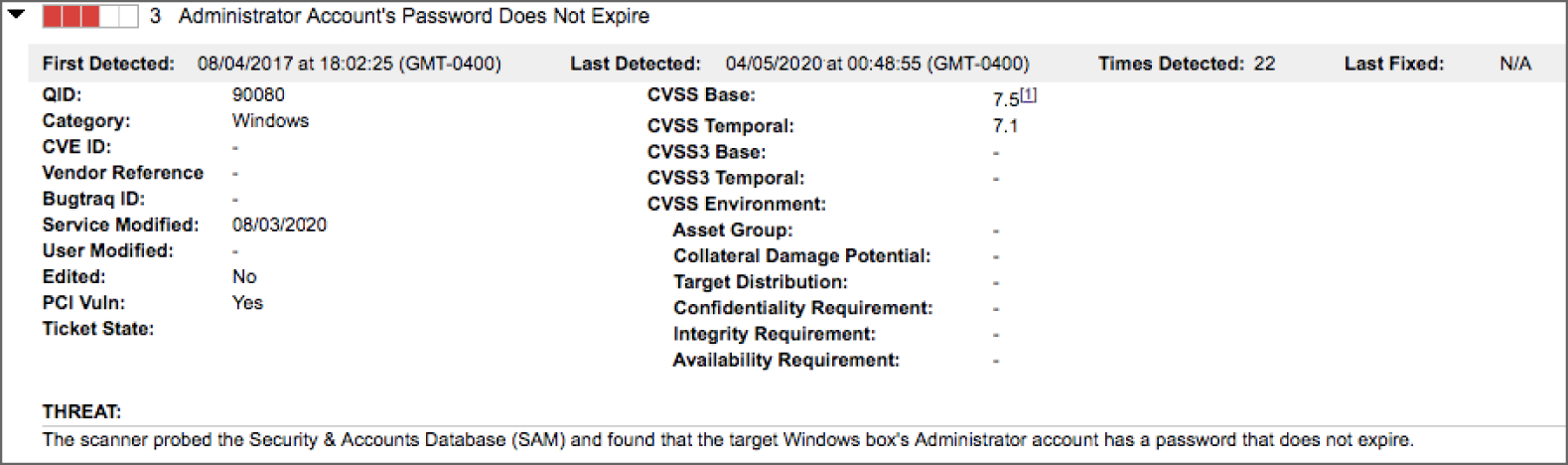
- Heidi runs a vulnerability scan of the management interface of her organization's virtualization platform and finds the severity 1 vulnerability shown here. What circumstance, if present, should increase the severity level of this vulnerability to Heidi?
- Lack of encryption
- Missing security patch
- Exposure to external networks
- Out-of-date antivirus signatures
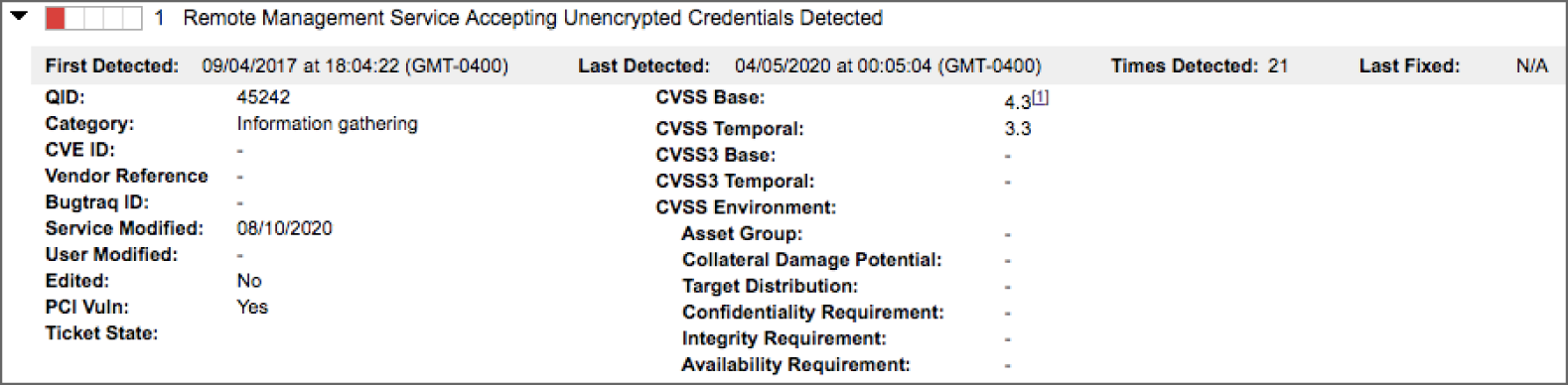
- Rowan ran a port scan against a network switch located on her organization's internal network and discovered the results shown here. She ran the scan from her workstation on the employee VLAN. Which one of the following results should be of greatest concern to her?
- Port 22
- Port 23
- Port 80
- Ports 8192 to 8194
- Evan is troubleshooting a vulnerability scan issue on his network. He is conducting an external scan of a website located on the web server shown in the diagram. After checking the Apache
httpdlogs on the web server, he saw no sign of the scan requests. Which one of the following causes is the least likely issue for him to troubleshoot?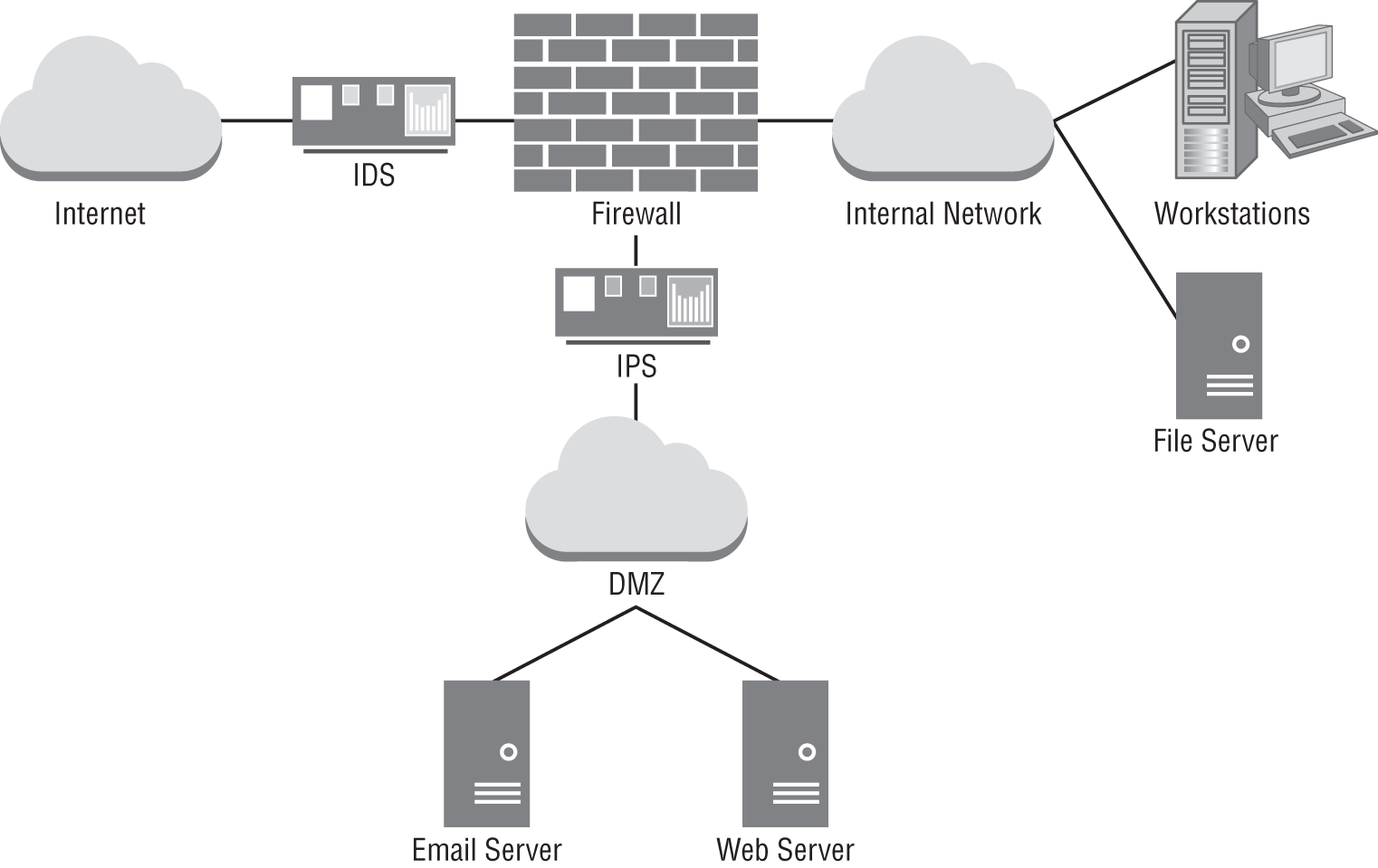
- The scans are being blocked by an intrusion prevention system.
- The scans are being blocked by an Apache
.htaccessfile. - The scans are being blocked by a network firewall.
- The scans are being blocked by a host firewall.
- Sam is looking for evidence of software that was installed on a Windows 10 system. He believes that the programs were deleted and that the suspect used both registry and log cleaners to hide evidence. What Windows feature can't he use to find evidence of the use of these programs?
- The MFT
- Volume shadow copies
- The shim (application compatibility) cache
- Prefetch files
- Mila is evaluating the security of an application developed within her organization. She would like to assess the application's security by supplying it with invalid inputs. What technique is Mila planning to use?
- Fault injection
- Stress testing
- Mutation testing
- Fuzz testing
- A port scan conducted during a security assessment shows the following results. What type of device has most likely been scanned?
Nmap scan report for EXAMPLE (192.168.1.79)Host is up (1.00s latency).Not shown: 992 closed portsPORT STATE21/tcp open23/tcp open80/tcp open280/tcp open443/tcp open515/tcp open631/tcp open9100/tcp openNmap done: 1 IP address (1 host up) scanned in 124.20 seconds- A wireless access point
- A server
- A printer
- A switch
- Kim is reviewing the data gathered by the first responder to a security incident and comes across a text file containing the output shown here. What command generated this output?
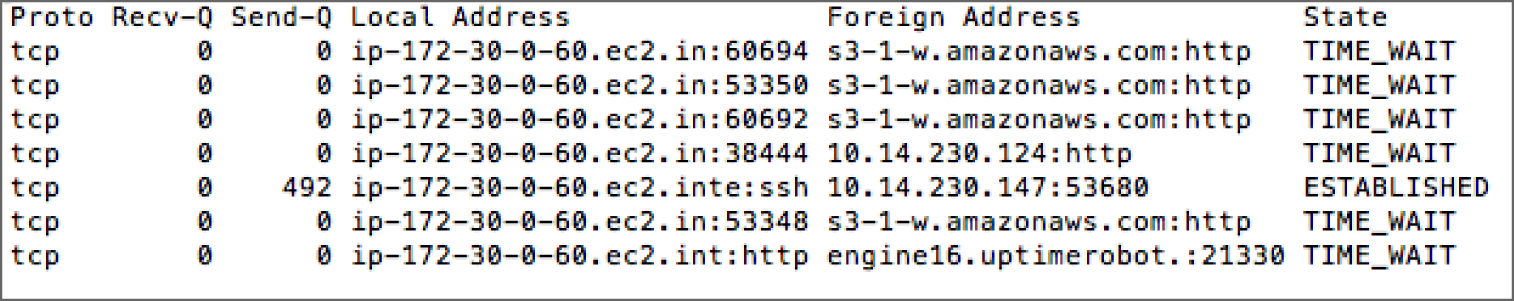
traceroutenetstatifconfigsockets
- Which of the following is not one of the major categories of security event indicators described by NIST 800-61?
- Alerts from IDS, IPS, SIEM, AV, and other security systems
- Logs generated by systems, services, and applications
- Exploit developers
- Internal and external sources
- During an
nmapscan of a network, Charles receives the following response from nmap:Starting Nmap 7.80 ( https://nmap.org ) at 2020-04-21 20:03 EDTNmap done: 256 IP addresses (0 hosts up) scanned in 29.74 secondsWhat can Charles deduce about the network segment from these results?
- There are no active hosts in the network segment.
- All hosts on the network segment are firewalled.
- The scan was misconfigured.
- Charles cannot determine if there are hosts on the network segment from this scan.
- Oskar is designing a vulnerability management program for his company, a hosted service provider. He would like to check all relevant documents for customer requirements that may affect his scanning. Which one of the following documents is least likely to contain this information?
- BPA
- SLA
- MOU
- BIA
- During a port scan of a server, Gwen discovered that the following ports are open on the internal network:
TCP port 25
TCP port 80
TCP port 110
TCP port 443
TCP port 1521
TCP port 3389
Of the services listed here, for which one does the scan not provide evidence that it is likely running on the server?
- Web
- Database
- SSH
- As part of her forensic analysis of a wiped thumb drive, Selah runs Scalpel to carve data from the image she created. After running Scalpel, she sees the following in the
audit.logfile created by the program. What should Selah do next?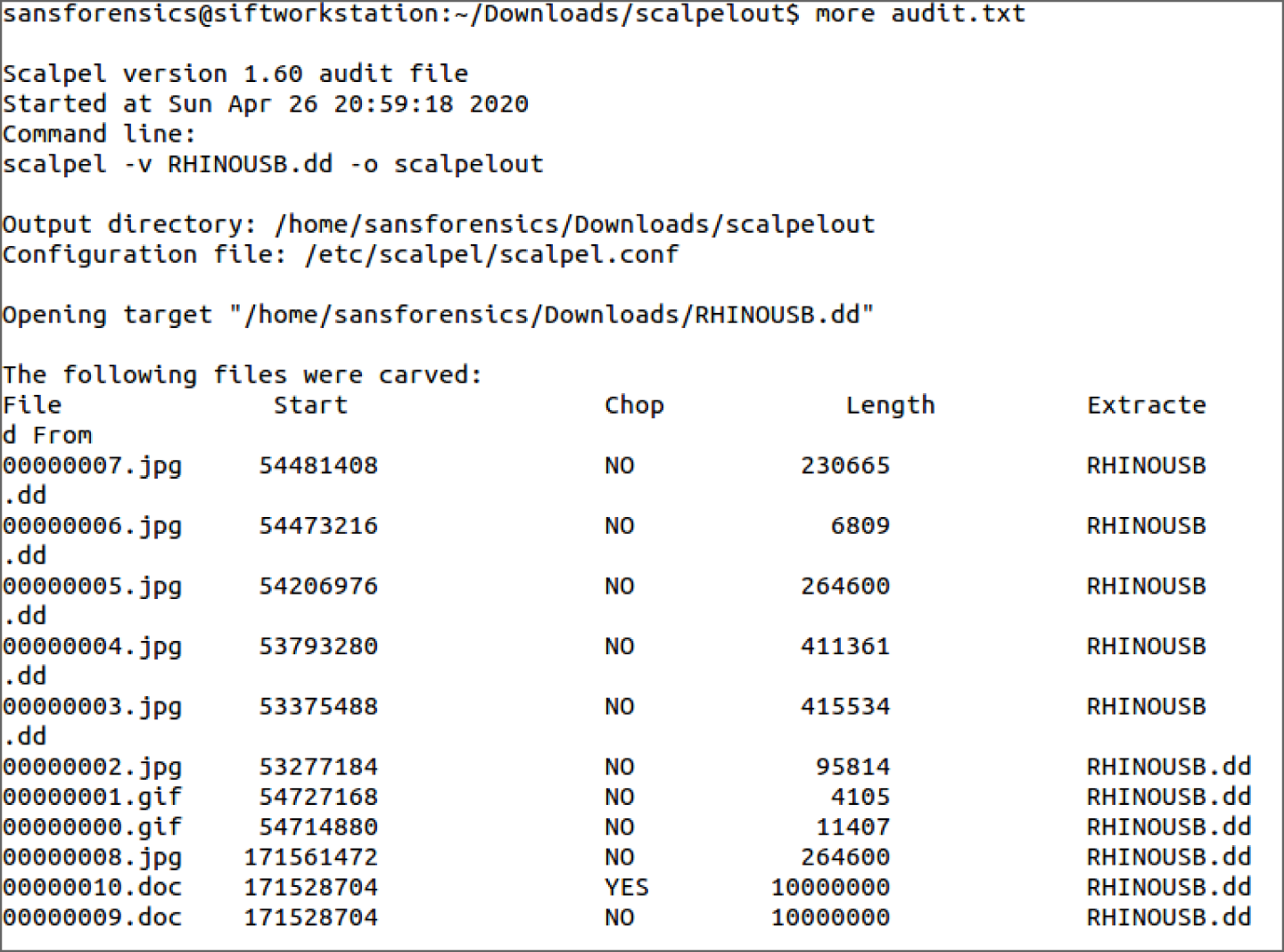
- Run a data recovery program on the drive to retrieve the files.
- Run Scalpel in filename recovery mode to retrieve the actual filenames and directory structures of the files.
- Review the contents of the
scalpeloutfolder. - Use the identified filenames to process the file using a full forensic suite.
- As part of a government acquisitions program for the U.S. Department of Defense (DoD), Sean is required to ensure that the chips and other hardware-level components used in the switches, routers, and servers that he purchases do not include malware or other potential attack vectors. What type of supplier should Sean seek out?
- A TPM
- An OEM provider
- A trusted foundry
- A gray-market provider
- One of the servers that Adam is responsible for recently ran out of disk space. Despite system-level alarms, the problem was not detected, resulting in an outage when the server crashed. How would this issue be categorized if the NIST threat categorization method were used as part of an after-action review?
- Environmental
- Adversarial
- Accidental
- Structural
- Pranab would like guidance on grouping information into varying levels of sensitivity. He plans to use these groupings to assist with decisions around the security controls that the organization will apply to storage devices containing that information. Which one of the following policies is most likely to contain relevant information for Pranab's decision-making process?
- Data retention policy
- Data classification policy
- Data encryption policy
- Data disposal policy
- Erin is attempting to collect network configuration information from a Windows system on her network. She is familiar with the Linux operating system and would use the
ifconfigcommand to obtain the desired information on a Linux system. What equivalent command should she use in Windows?ipconfignetstatifconfignetcfg
- Lonnie ran a vulnerability scan of a server that he recently detected in his organization that is not listed in the organization's configuration management database. One of the vulnerabilities detected is shown here. What type of service is most likely running on this server?
- Database
- Web
- Time
- Network management
- Jorge would like to use a standardized system for evaluating the severity of security vulnerabilities. What SCAP component offers this capability?
- CPE
- CVE
- CVSS
- CCE
- When performing threat-hunting activities, what are cybersecurity analysts most directly seeking?
- Vulnerabilities
- Indicators of compromise
- Misconfigurations
- Unpatched systems
- Taylor is preparing to run vulnerability scans of a web application server that his organization recently deployed for public access. He would like to understand what information is available to a potential external attacker about the system as well as what damage an attacker might be able to cause on the system. Which one of the following scan types would be least likely to provide this type of information?
- Internal network vulnerability scan
- Port scan
- Web application vulnerability scan
- External network vulnerability scan
- While analyzing a packet capture in Wireshark, Chris finds the packet shown here. Which of the following is he unable to determine from this packet?
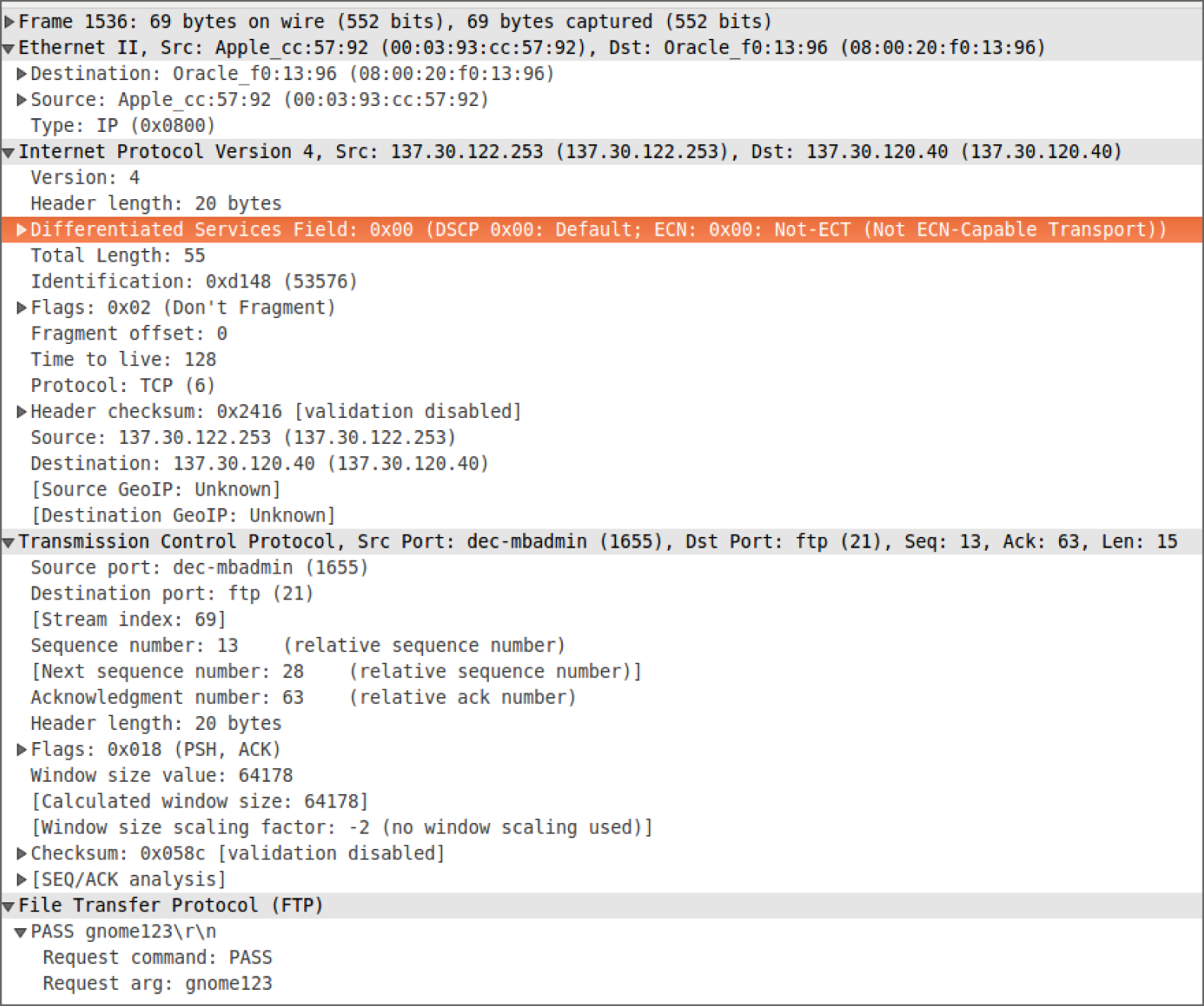
- That the username used was
gnome - That the protocol used was FTP
- That the password was
gnome123 - That the remote system was 137.30.120.40
- That the username used was
- Cynthia's review of her network traffic focuses on the graph shown here. What occurred in late June?
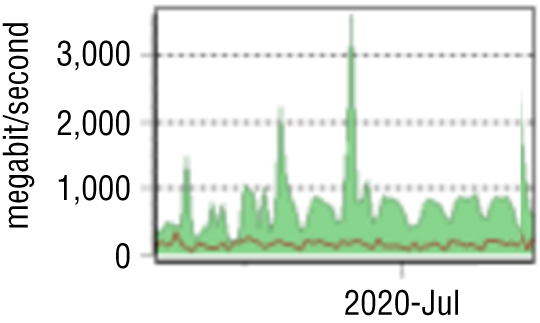
- Beaconing
- High network bandwidth consumption
- A denial-of-service attack
- A link failure
- Carlos arrived at the office this morning to find a subpoena on his desk requesting electronic records in his control. What type of procedure should he consult to determine appropriate next steps, including the people he should consult and the technical process he should follow?
- Evidence production procedure
- Monitoring procedure
- Data classification procedure
- Patching procedure
- Pranab is attempting to determine what services a Windows system is running and decides to use the
netstat -atcommand to list TCP ports. He receives the output shown here. The system is most likely running which services?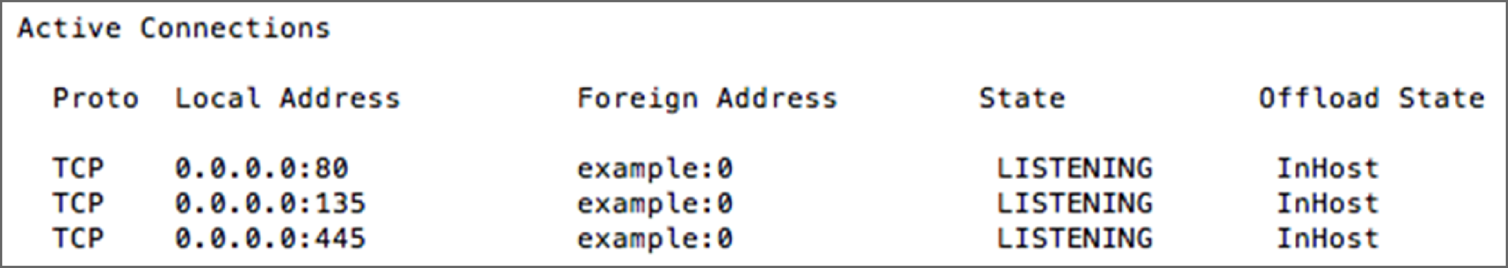
- A plain-text web server, Microsoft file sharing, and a secure web server
- SSH, email, and a plain-text web server
- An email server, a plain-text web server, and Microsoft-DS
- A plain-text web server, Microsoft RPC, and Microsoft-DS
- Paul is researching models for implementing an IT help desk and would like to draw upon best practices in the industry. Which one of the following standard frameworks would provide Paul with the best guidance?
- ISO
- ITIL
- COBIT
- PCI DSS
- Which stage of the incident response process includes activities such as adding IPS signatures to detect new attacks?
- Detection and analysis
- Containment, eradication, and recovery
- Postincident activity
- Preparation
- Gloria is configuring vulnerability scans for a new web server in her organization. The server is located on the DMZ network, as shown here. What type of scans should Gloria configure for best results?
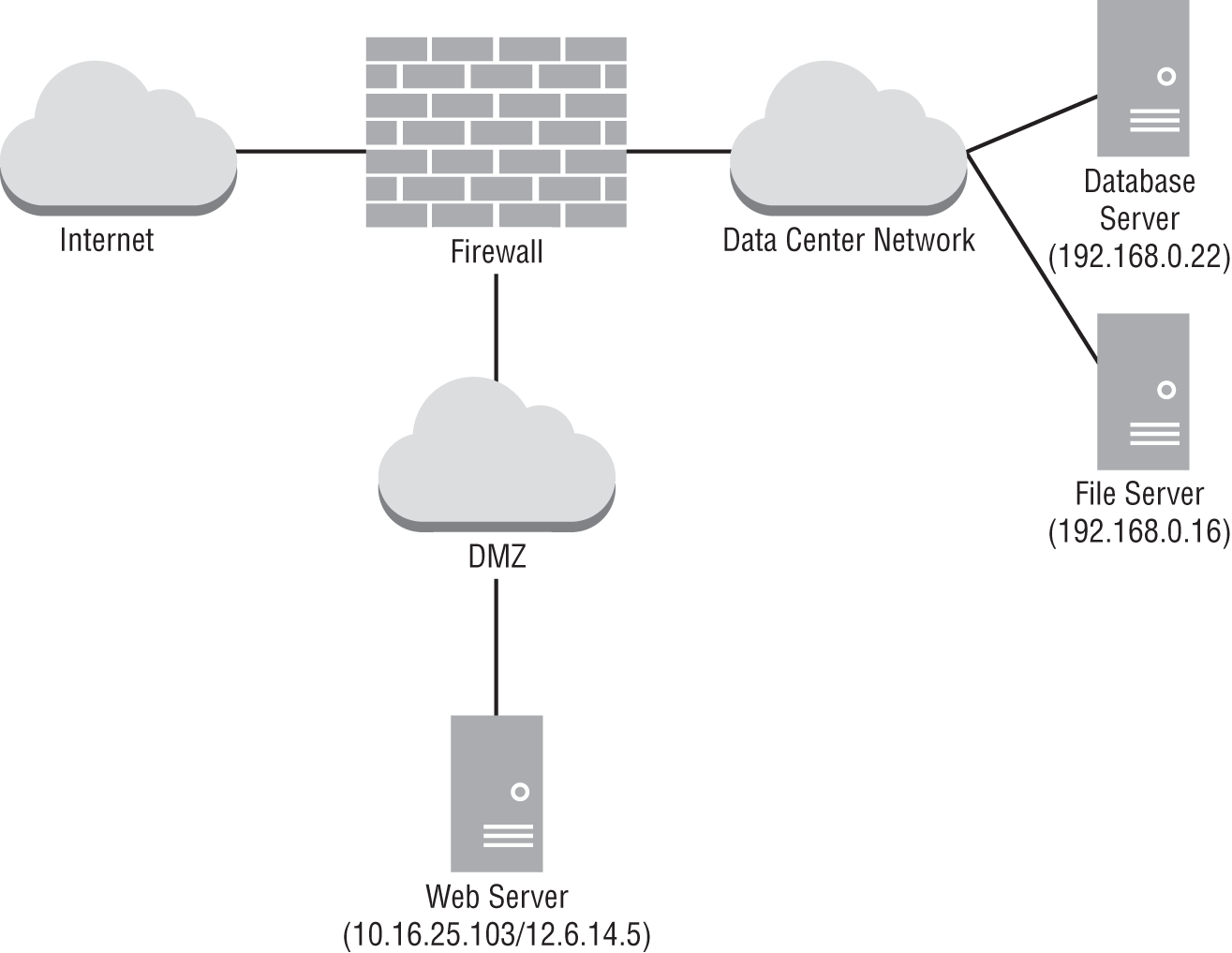
- Gloria should not scan servers located in the DMZ.
- Gloria should perform only internal scans of the server.
- Gloria should perform only external scans of the server.
- Gloria should perform both internal and external scans of the server.
- Pranab is preparing to reuse media that contained data that his organization classifies as having “moderate” value. If he wants to follow NIST SP 800-88's guidelines, what should he do to the media if the media will not leave his organization's control?
- Reformat it
- Clear it
- Purge it
- Destroy it
- Susan is building an incident response program and intends to implement NIST's recommended actions to improve the effectiveness of incident analysis. Which of the following items is not a NIST-recommended incident analysis improvement?
- Perform behavioral baselining.
- Create and implement a logging policy.
- Set system BIOS clocks regularly.
- Maintain an organizationwide system configuration database.
- Jim's nmap port scan of a system showed the following list of ports:
PORT STATE SERVICE80/tcp open http135/tcp open msrpc139/tcp open netbios-ssn445/tcp open microsoft-ds902/tcp open iss-realsecure912/tcp open apex-mesh3389/tcp open ms-wbt-serverWhat operating system is the remote system most likely running?
- Windows
- Linux
- An embedded OS
- macOS
- The Snort IPS that Adam has configured includes a rule that reads as follows:
alert tcp $EXTERNAL_NET any -> 10.0.10.0/24 80(msg:"Alert!";content:"http|3a|//www.example.com/download.php"; nocase;offset:12; classtype: web-application-activity;sid:5555555; rev:1;)What type of detection method is Adam using?
- Anomaly-based
- Trend-based
- Availability-based
- Behavioral-based
- Peter works for an organization that is joining a consortium of similar organizations that use a federated identity management system. He is configuring his identity management system to participate in the federation. Specifically, he wants to ensure that users at his organization will be able to use their credentials to access federated services. What role is Peter configuring?
- Relying party
- Service provider
- Identity provider
- Consumer
- Helen is seeking to protect her organization against attacks that involve the theft of user credentials. Which one of the following threats poses the greatest risk of credential theft in most organizations?
- DNS poisoning
- Phishing
- Telephone-based social engineering
- Shoulder surfing
- As part of her duties as an SOC analyst, Emily is tasked with monitoring intrusion detection sensors that cover her employer's corporate headquarters network. During her shift, Emily's IDS reports that a network scan has occurred from a system with IP address 10.0.11.19 on the organization's unauthenticated guest wireless network aimed at systems on an external network. What should Emily's first step be?
- Report the event to the impacted third parties.
- Report the event to law enforcement.
- Check the system's MAC address against known assets.
- Check authentication logs to identify the logged-in user.
- Which of the following commands is not useful for validating user permissions on a Linux system?
more /etc/sudoersgroupsstatstrings
- Tommy's company recently implemented a new policy that restricts root access to its cloud computing service provider master account. This policy requires that a team member from the operations group retrieve a password from a password vault to log in to the account. The account then uses two-factor authentication that requires that a team member from the security group approve the login. What type of control is the company using?
- Separation of duties
- Privileged account monitoring
- Dual control
- Least privilege
- Sai works in an environment that is subject to the Payment Card Industry Data Security Standard (PCI DSS). He realizes that technical constraints prevent the organization from meeting a specific PCI DSS requirement and wants to implement a compensating control. Which one of the following statements is not true about proper compensating controls?
- The control must include a clear audit mechanism.
- The control must meet the intent and rigor of the original requirement.
- The control must provide a similar level of defense as the original requirement provides.
- The control must be above and beyond other requirements.
- Lou recently scanned a web server in his environment and received the vulnerability report shown here. What action can Lou take to address this vulnerability?

- Configure TLS
- Replace the certificate
- Unblock port 443
- Block port 80
- Mike's company recently suffered a security incident when they lost control of thousands of personal customer records. Many of these records were from projects that ended long ago and served no business purpose. What type of policy, if followed, would have best limited the impact of this incident?
- Data ownership policy
- Account management policy
- Acceptable use policy
- Data retention policy
- Which of the following factors is not typically considered when determining whether evidence should be retained?
- Media life span
- Likelihood of civil litigation
- Organizational retention policies
- Likelihood of criminal prosecution
- Match each of the following with the appropriate element of the CIA Triad:
- A hard drive failure resulting in a service outage
- A termination letter that is left on a printer and read by others in the department
- Modification of an email's content by a third party
- 1. Integrity, 2. Confidentiality, 3. Confidentiality
- 1. Integrity, 2. Confidentiality, 3. Availability
- 1. Availability, 2. Availability, 3. Confidentiality
- 1. Availability, 2. Confidentiality, 3. Integrity
- Niesha discovered the vulnerability shown here on a server running in her organization. What would be the best way for Niesha to resolve this issue?
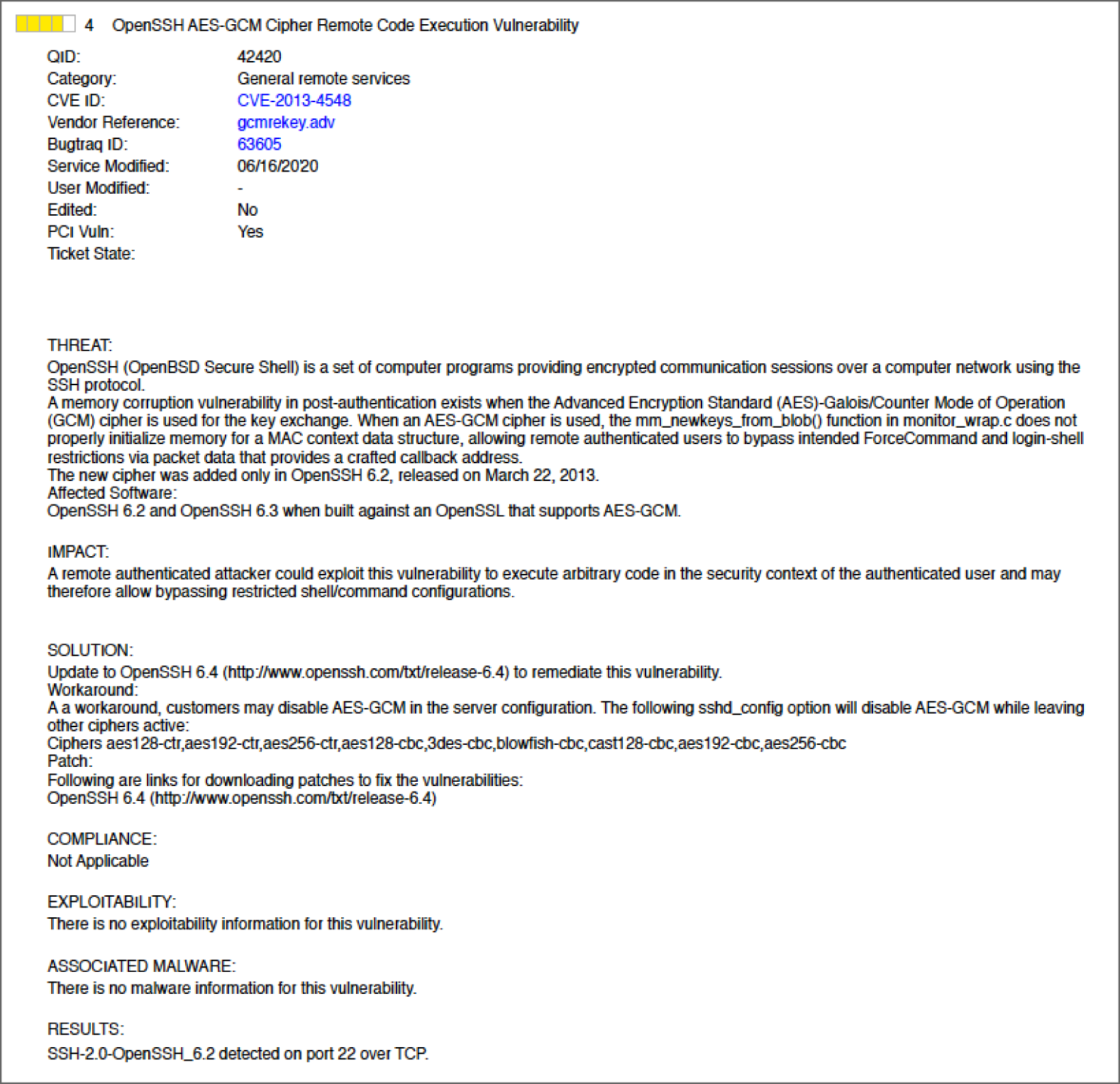
- Disable the use of AES-GCM.
- Upgrade OpenSSH.
- Upgrade the operating system.
- Update antivirus signatures.
- As part of her postincident recovery process, Alicia creates a separate virtual network as shown here to contain compromised systems she needs to investigate. What containment technique is she using?
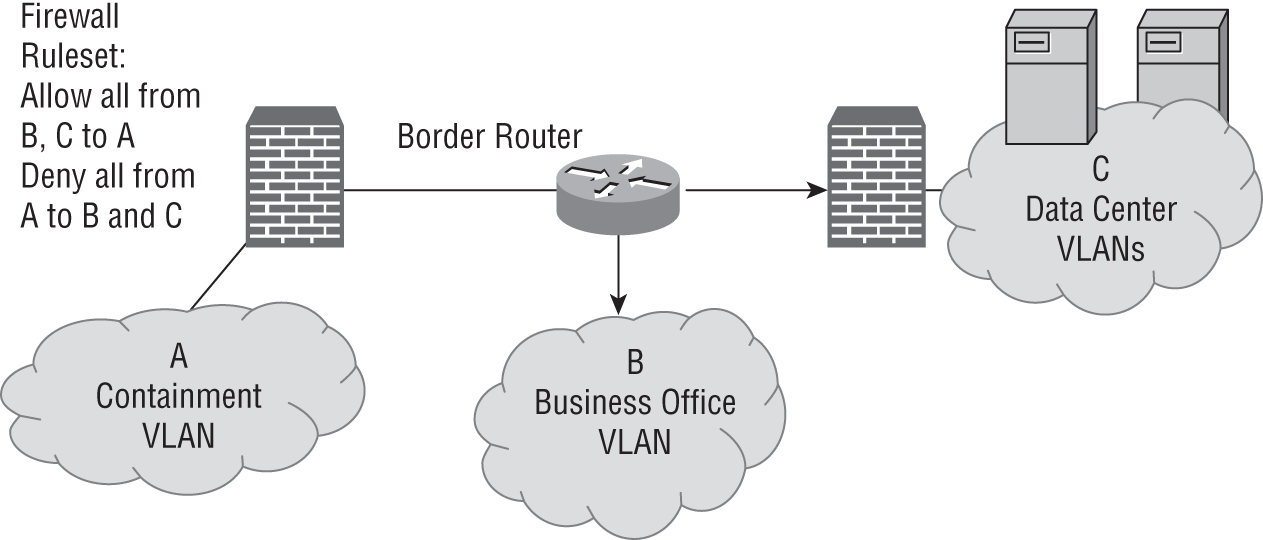
- Segmentation
- Isolation
- Removal
- Reverse engineering
- Jennifer is reviewing her network monitoring configurations and sees the following chart for a system she runs remotely in Amazon's Web Services (AWS) environment more than 400 miles away. What can she use this data for?
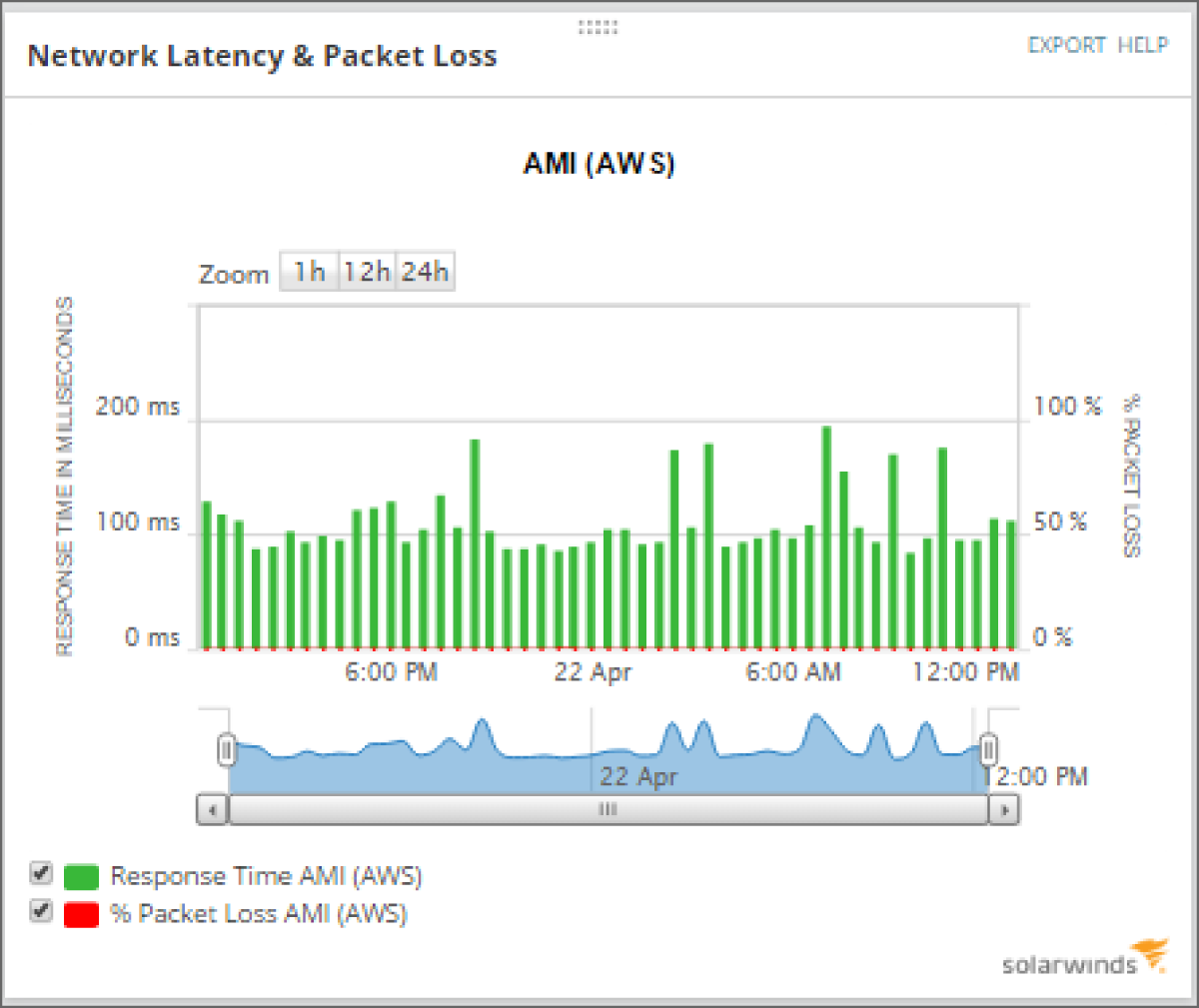
- Incident response; she needs to determine the issue causing the spikes in response time.
- The high packet loss must be investigated, since it may indicate a denial-of-service attack.
- She can use this data to determine a reasonable response time baseline.
- The high response time must be investigated, since it may indicate a denial-of-service attack.
- The Windows system that Abdul is conducting live forensics on shows a partition map, as shown here. If Abdul believes that a hidden partition was deleted resulting in the unallocated space, which of the following tools is best suited to identifying the data found in the unallocated space?
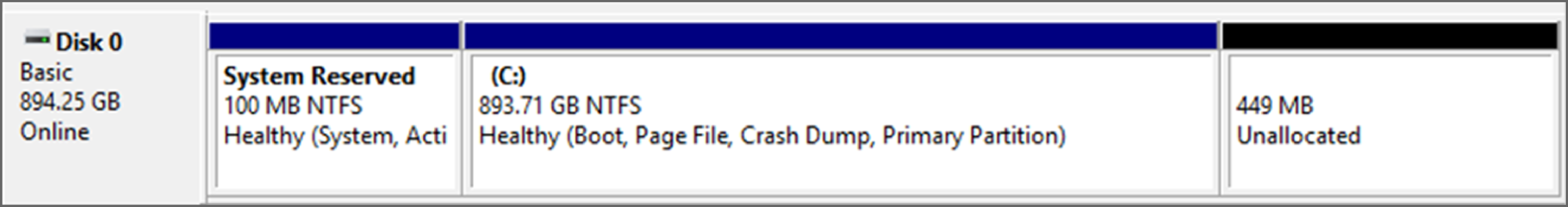
- Scalpel
- DBAN
parteddd
- During a postmortem forensic analysis of a Windows system that was shut down after its user saw strange behavior, Pranab concludes that the system he is reviewing was likely infected with a memory-resident malware package. What is his best means of finding the malware?
- Search for a core dump or
hiberfil.systo analyze. - Review the INDX files and Windows registry for signs of infection.
- Boot the system and then use a tool like the Volatility Framework to capture live memory.
- Check volume shadow copies for historic information prior to the reboot.
- Search for a core dump or
- Juliette's organization recently suffered a cross-site scripting attack, and she plans to implement input validation to protect against the recurrence of such attacks in the future. Which one of the following HTML tags should be most carefully scrutinized when it appears in user input?
<SCRIPT><XSS><B><EM>
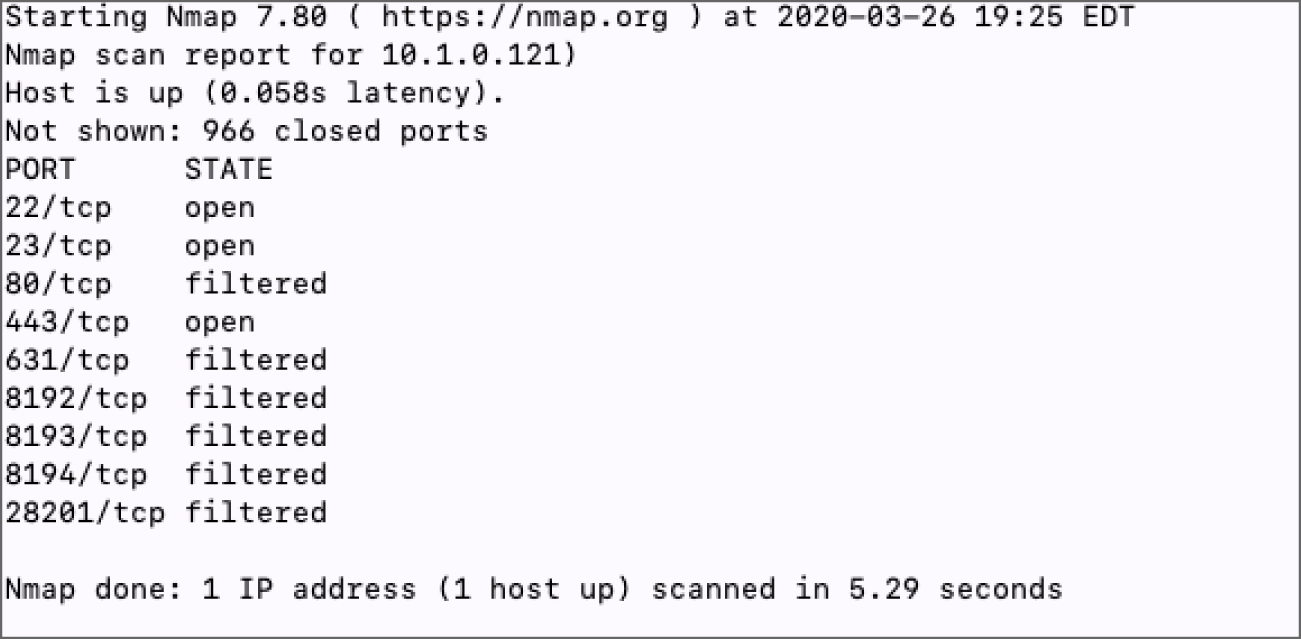
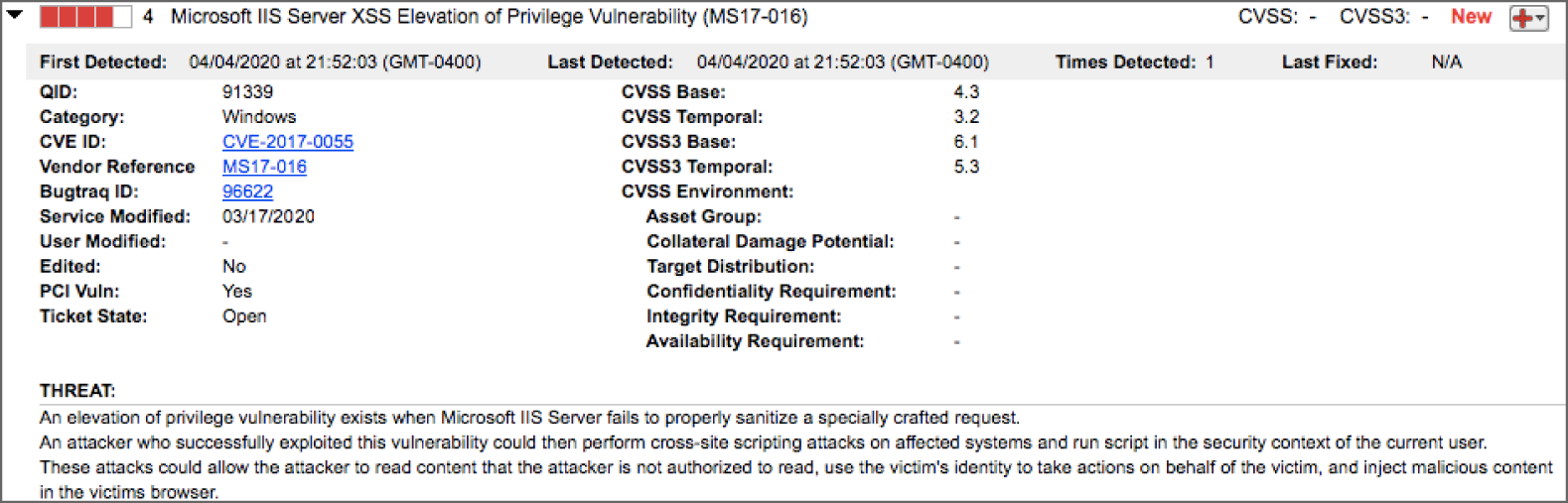
- Jessie needs to prevent port scans like the scan shown here. Which of the following is a valid method for preventing port scans?
- Not registering systems in DNS
- Using a firewall to restrict traffic to only ports required for business purposes
- Using a heuristic detection rule on an IPS
- Implementing port security
- The IT services company that Pranab works for uses the NIST functional impact categories to describe the impact of incidents. During a recent construction project, a contractor plugged a network device in twice to the same switch, resulting in a network loop and taking down the organization's network for a third of their users. How should Pranab classify this event?
- Urgent
- Medium
- Important
- High
- What information can be gathered by observing the distinct default values of the following TCP/IP fields during reconnaissance activities: initial packet size, initial TTL, window size, maximum segment size, and flags?
- The target system's TCP version
- The target system's operating system
- The target system's MAC address
- These fields are only useful for packet analysis
- Brooke would like to find a technology platform that automates workflows across a variety of security tools, including the automated response to security incidents. What category of tool best meets this need?
- SIEM
- NIPS
- SOAR
- DLP
- Miray needs to identify the device or storage type that has the lowest order of volatility. Which of the following is the least volatile?
- Network traffic
- A solid-state drive
- A spinning hard drive
- A DVD-ROM
- Henry recently completed a vulnerability scan of his organization's datacenter and received the vulnerability report shown here from a server running in the data center. This server is running on a virtualization platform running on a bare-metal hypervisor. Where must Henry correct this issue?
- Guest operating system
- Hypervisor
- Application
- Host operating system
- Luis is an IT consultant brought in to assess the maturity of risk management practices at a firm using the NIST Cybersecurity Framework. During his evaluation, he determines that the organization does use an organizationwide approach to managing cybersecurity risk but that it does not use risk-informed policies, processes, and procedures to address potential cybersecurity events. At what tier of the Cybersecurity Framework does this organization's risk management program reside?
- Tier 1: Partial
- Tier 2: Risk Informed
- Tier 3: Repeatable
- Tier 4: Adaptive
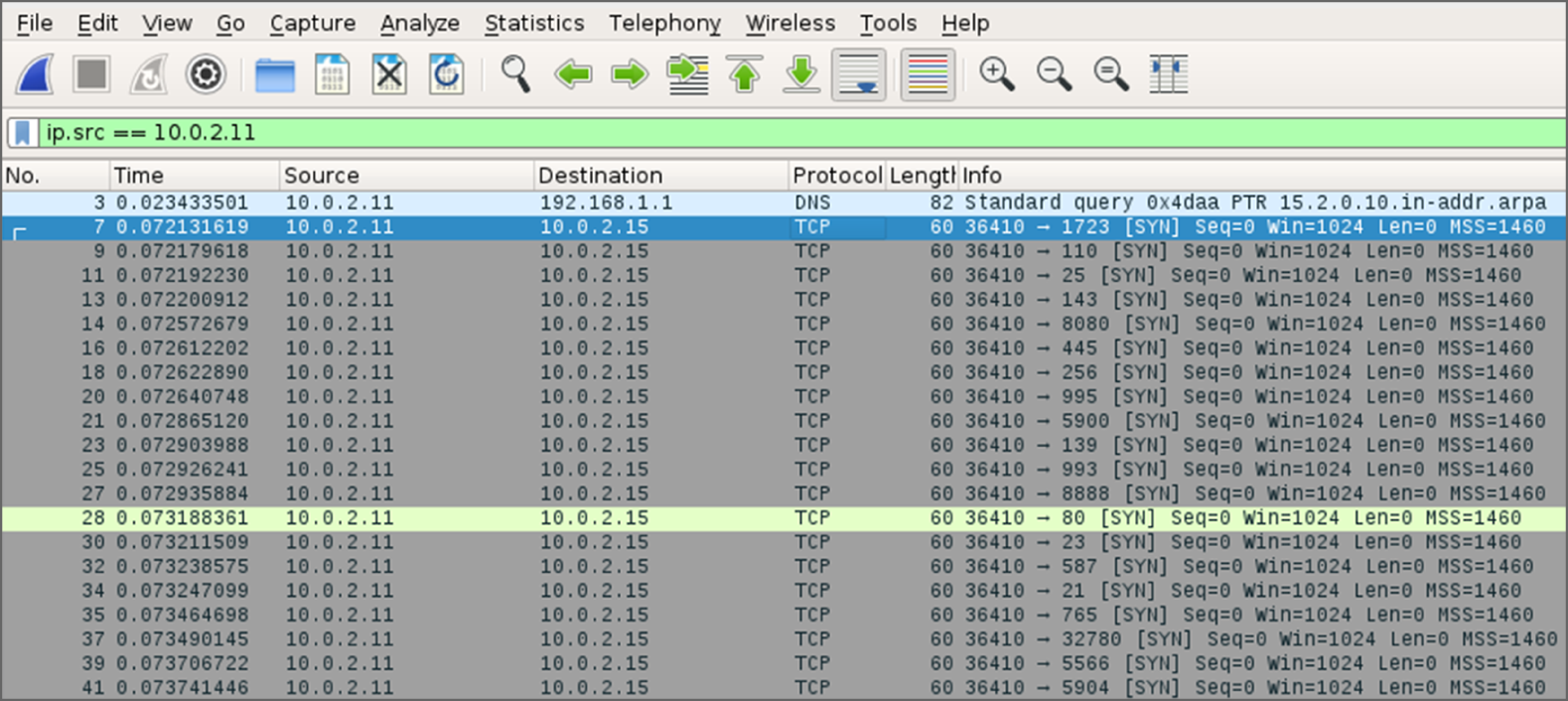
- After receiving complaints about a system on her network not performing correctly, Anastasia decides to investigate the issue by capturing traffic with Wireshark. The captured traffic is shown here. What type of issue is Anastasia most likely seeing?

- A link failure
- A failed three-way handshake
- A DDoS
- A SYN flood
- During a log review, Lisa sees repeated firewall entries, as shown here:
Sep 16 2019 23:01:37: %ASA-4-106023: Deny tcp srcoutside:10.10.0.100/53534 dstinside:192.168.1.128/1521 byaccess-group "OUTSIDE" [0x5063b82f, 0x0]Sep 16 2019 23:01:38: %ASA-4-106023: Deny tcp srcoutside:10.10.0.100/53534 dstinside:192.168.1.128/1521 byaccess-group "OUTSIDE" [0x5063b82f, 0x0]Sep 16 2019 23:01:39: %ASA-4-106023: Deny tcp srcoutside:10.10.0.100/53534 dstinside:192.168.1.128/1521 byaccess-group "OUTSIDE" [0x5063b82f, 0x0]Sep 16 2019 23:01:40: %ASA-4-106023: Deny tcp srcoutside:10.10.0.100/53534 dstinside:192.168.1.128/1521 byaccess-group "OUTSIDE" [0x5063b82f, 0x0]What service is the remote system most likely attempting to access?
- H.323
- SNMP
- MS-SQL
- Oracle
- After finishing a forensic case, Lucas needs to wipe the media that he is using to prepare it for the next case. Which of the following methods is best suited to preparing the SSD that he will use?
- Degauss the drive.
- Zero-write the drive.
- Use a PRNG.
- Use the ATA Secure Erase command.
- Luis is creating a vulnerability management program for his company. He only has the resources to conduct daily scans of approximately 10 percent of his systems, and the rest will be scheduled for weekly scans. He would like to ensure that the systems containing the most sensitive information receive scans on a more frequent basis. What criterion is Luis using?
- Data privacy
- Data remanence
- Data retention
- Data classification
- While investigating a cybersecurity incident, Bob discovers the file shown here stored on a system on his network. Which one of the following tools most likely generated this file?
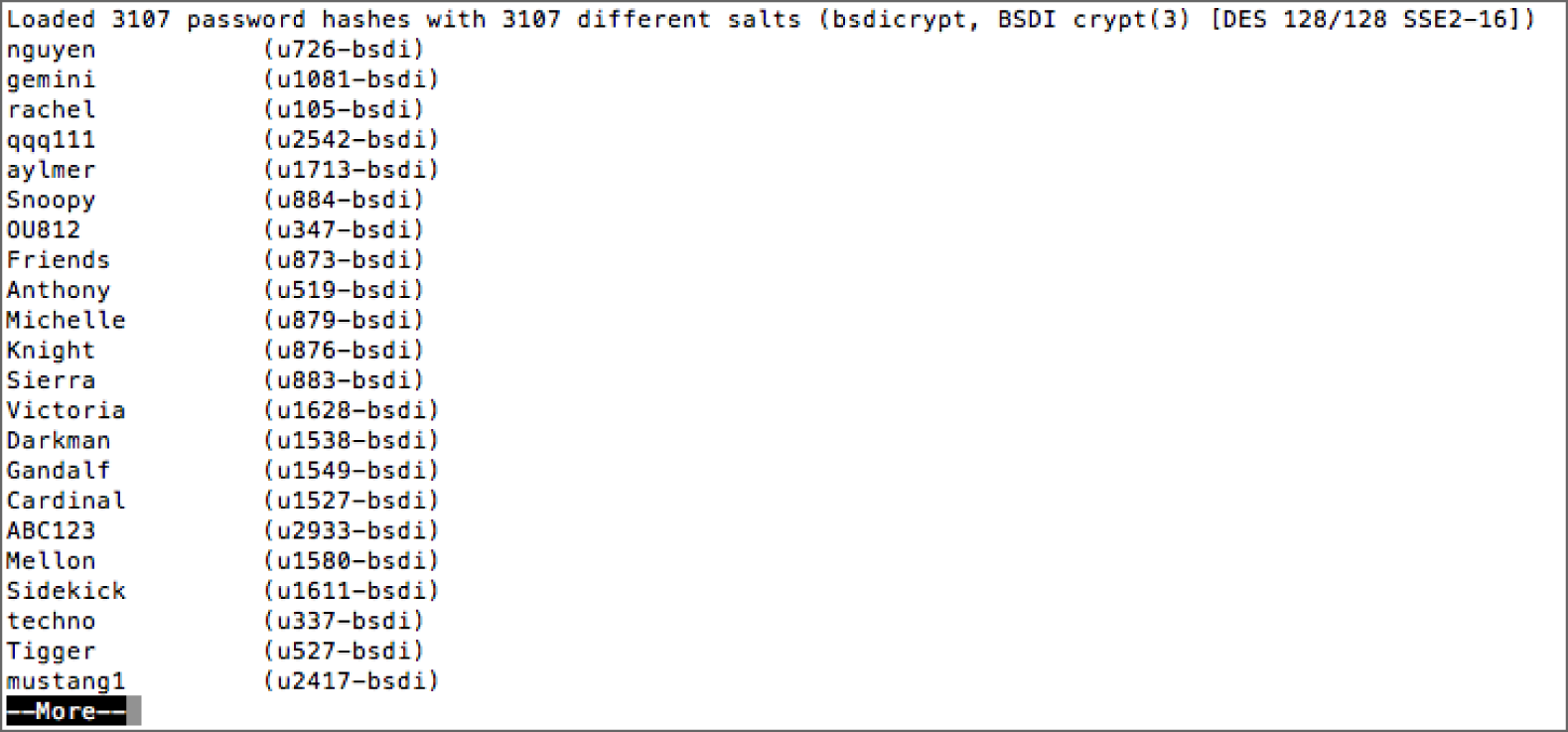
- Cain & Abel
- Metasploit
- ftk
- John the Ripper
- During a security exercise, which team engages in offensive operations designed to compromise security controls?
- Black team
- Red team
- Blue team
- White team
- Peter is designing a vulnerability scanning program for the large chain of retail stores where he works. The store operates point-of-sale terminals in its retail stores as well as an e-commerce website. Which one of the following statements about PCI DSS compliance is not true?
- Peter's company must hire an approved scanning vendor to perform vulnerability scans.
- The scanning program must include, at a minimum, weekly scans of the internal network.
- The point-of-sale terminals and website both require vulnerability scans.
- Peter may perform some required vulnerability scans on his own.
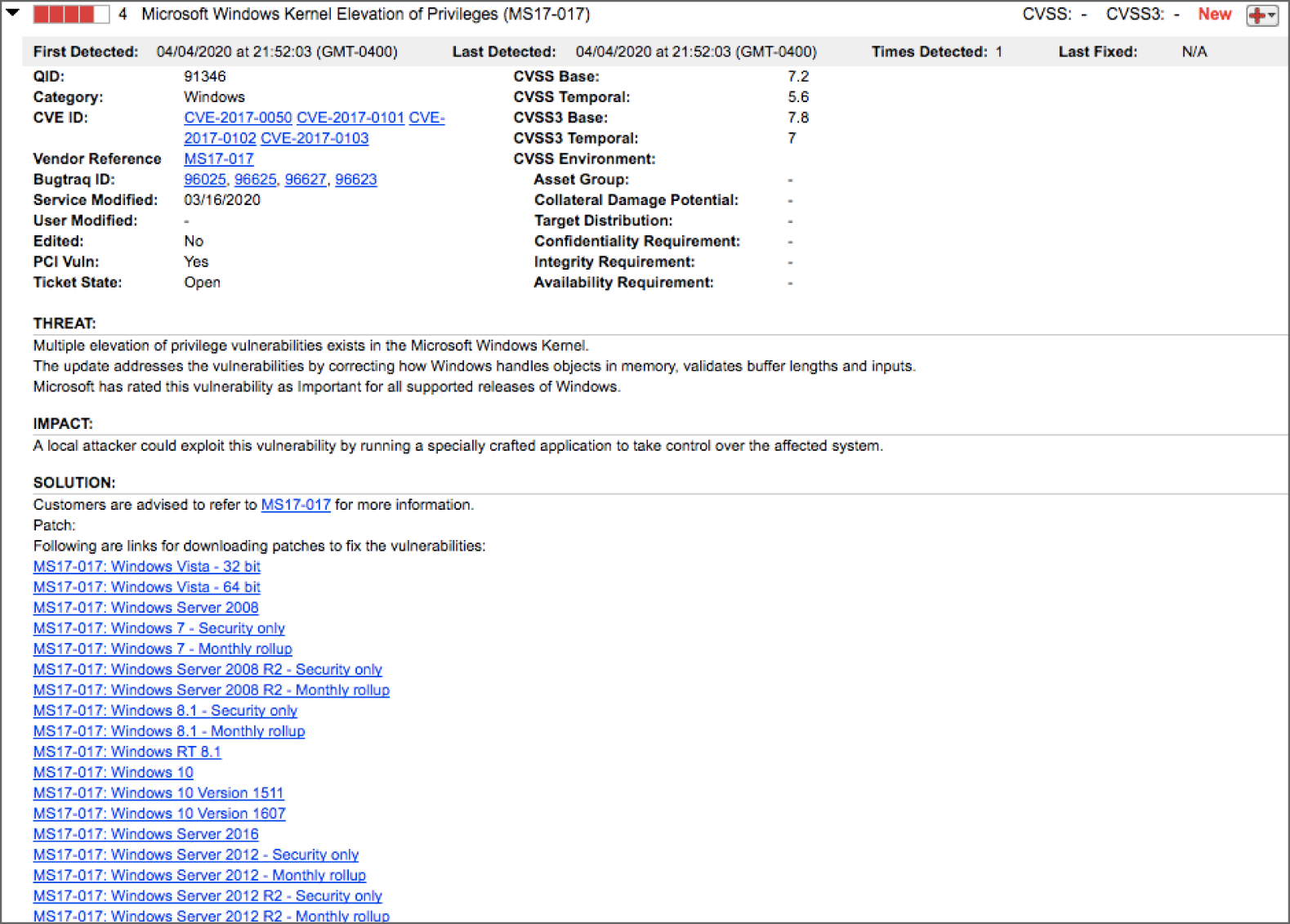
- Rachel discovered the vulnerability shown here when scanning a web server in her organization. Which one of the following approaches would best resolve this issue?
- Patching the server
- Performing input validation
- Adjusting firewall rules
- Rewriting the application code
- Charlene's incident response team is fighting a rapidly spreading zero-day malware package that silently installs via Adobe Flash a vulnerability when an email attachment is viewed via webmail. After identifying a compromised system, she determines that the system is beaconing to a group of fast flux DNS entries. Which of the following techniques is best suited to identifying other infected hosts?
- Update antivirus software and scan using the latest definitions.
- Monitor for the IP addresses associated with the command-and-control systems.
- Log DNS queries to identify compromised systems.
- Check email logs for potential recipients of the message.
- What nmap feature is enabled with the
-Oflag?- OS detection
- Online/offline detection
- Origami attack detection
- Origination port validation
- Mika uses a security token like the unit shown here and a password to authenticate to her PayPal account. What two types of factors is she using?
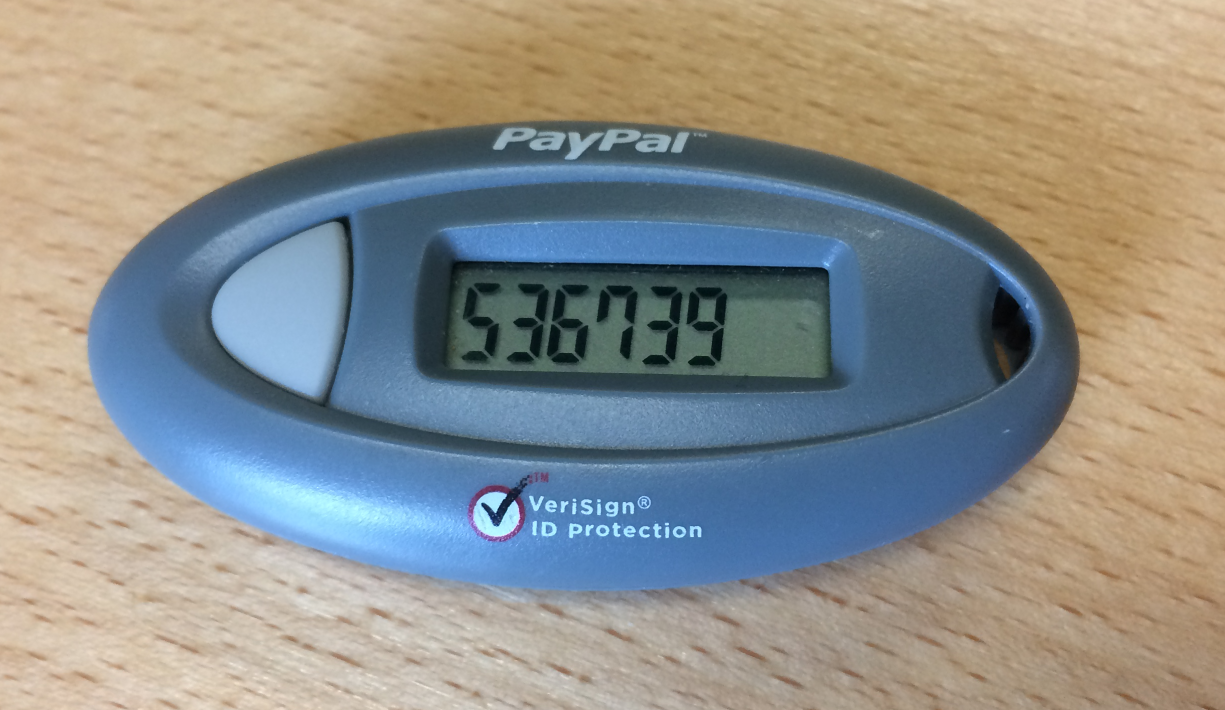
- Something she knows and something she has
- Something she knows and something she is
- Something she is and something she has
- Mika is only using one type of factor because she knows the token code and her password
- Jose is working with his manager to implement a vulnerability management program for his company. His manager tells him that he should focus on remediating critical and high-severity risks to externally accessible systems. He also tells Jose that the organization does not want to address risks on systems without any external exposure or risks rated medium or lower. Jose disagrees with this approach and believes that he should also address critical and high-severity risks on internal systems. How should he handle the situation?
- Jose should recognize that his manager has made a decision based upon the organization's risk appetite and should accept it and carry out his manager's request.
- Jose should discuss his opinion with his manager and request that the remediation criteria be changed.
- Jose should ask his manager's supervisor for a meeting to discuss his concerns about the manager's approach.
- Jose should carry out the remediation program in the manner that he feels is appropriate because it will address all of the risks identified by the manager as well as additional risks.
- Susan needs to test thousands of submitted binaries. She needs to ensure that the applications do not contain malicious code. What technique is best suited to this need?
- Sandboxing
- Implementing a honeypot
- Decompiling and analyzing the application code
- Fagan testing
- When conducting a quantitative risk assessment, what term describes the total amount of damage expected to occur as a result of one incident?
- EF
- SLE
- AV
- ALE
- Chris is implementing cryptographic controls to protect his organization and would like to use defense-in-depth controls to protect sensitive information stored and transmitted by a web server. Which one of the following controls would be least suitable to directly provide this protection?
- TLS
- VPN
- DLP
- FDE
- Alex needs to deploy a solution that will limit access to his network to only authorized individuals while also ensuring that the systems that connect to the network meet his organization's patching, antivirus, and configuration requirements. Which of the following technologies will best meet these requirements?
- Whitelisting
- Port security
- NAC
- EAP
- Chris has been tasked with removing data from systems and devices that leave his organization. One of the devices is a large multifunction device that combines copying, fax, and printing capabilities. It has a built-in hard drive to store print jobs and was used in an office that handles highly sensitive business information. If the multifunction device is leased, what is his best option for handling the drive?
- Destroy the drive.
- Reformat the drive using the MFD's built-in formatting program.
- Remove the drive and format it using a separate PC.
- Remove the drive and purge it.
- Rhonda recently configured new vulnerability scans for her organization's datacenter. Completing the scans according to current specifications requires that they run all day, every day. After the first day of scanning, Rhonda received complaints from administrators of network congestion during peak business hours. How should Rhonda handle this situation?
- Adjust the scanning frequency to avoid scanning during peak times.
- Request that network administrators increase available bandwidth to accommodate scanning.
- Inform the administrators of the importance of scanning and ask them to adjust the business requirements.
- Ignore the request because it does not meet security objectives.
- After restoring a system from 30-day-old backups after a compromise, administrators at Piper's company return the system to service. Shortly after that, Piper detects similar signs of compromise again. Why is restoring a system from a backup problematic in many cases?
- Backups cannot be tested for security issues.
- Restoring from backup may reintroduce the original vulnerability.
- Backups are performed with the firewall off and are insecure after restoration.
- Backups cannot be properly secured.
- Captured network traffic from a compromised system shows it reaching out to a series of five remote IP addresses that change on a regular basis. Since the system is believed to be compromised, the system's Internet access is blocked, and the system is isolated to a quarantine VLAN.
When forensic investigators review the system, no evidence of malware is found. Which of the following scenarios is most likely?
- The system was not infected, and the detection was a false positive.
- The beaconing behavior was part of a web bug.
- The beaconing behavior was due to a misconfigured application.
- The malware removed itself after losing network connectivity.
- Which one of the following ISO standards provides guidance on the development and implementation of information security management systems?
- ISO 27001
- ISO 9000
- ISO 11120
- ISO 23270
- Mika's forensic examination of a compromised Linux system is focused on determining what level of access attackers may have achieved using a compromised
wwwaccount. Which of the following is not useful if she wants to check for elevated privileges associated with thewwwuser?/etc/passwd/etc/shadow/etc/sudoers/etc/group
- Tracy is validating the web application security controls used by her organization. She wants to ensure that the organization is prepared to conduct forensic investigations of future security incidents. Which one of the following OWASP control categories is most likely to contribute to this effort?
- Implement logging
- Validate all inputs
- Parameterize queries
- Error and exception handling
- Jamal is using agent-based scanning to assess the security of his environment. Every time that Jamal runs a vulnerability scan against a particular system, it causes the system to hang. He spoke with the system administrator, who provided him with a report showing that the system is current with patches and has a properly configured firewall that allows access only from a small set of trusted internal servers. Jamal and the server administrator both consulted the vendor, and they are unable to determine the cause of the crashes and suspect that it may be a side effect of the agent. What would be Jamal's most appropriate course of action?
- Approve an exception for this server.
- Continue scanning the server each day.
- Require that the issue be corrected in 14 days and then resume scanning.
- Decommission the server.
- Brent's organization runs a web application that recently fell victim to a man-in-the-middle attack. Which one of the following controls serves as the best defense against this type of attack?
- HTTPS
- Input validation
- Patching
- Firewall
- During an nmap port scan using the
-sVflag to determine service versions, Ling discovers that the version of SSH on the Linux system she is scanning is not up-to-date. When she asks the system administrators, they inform her that the system is fully patched and that the SSH version is current. What issue is Ling most likely experiencing?- The system administrators are incorrect.
- The nmap version identification is using the banner to determine the service version.
- nmap does not provide service version information, so Ling cannot determine version levels in this way.
- The systems have not been rebooted since they were patched.
- Tyler scans his organization's mail server for vulnerabilities and finds the result shown here. What should be his next step?
- Shut down the server immediately.
- Initiate the change management process.
- Apply the patch.
- Rerun the scan.
- Carla is performing a penetration test of a web application and would like to use a software package that allows her to modify requests being sent from her system to a remote web server. Which one of the following tools would not meet Carla's needs?
- Nessus
- Burp
- ZAP
- Tamper Data
- Alex learns that a recent Microsoft patch covers a zero-day exploit in Microsoft Office that occurs because of incorrect memory handling. The flaw is described as potentially resulting in memory corruption and arbitrary code execution in the context of the current privilege level. Exploitation of the flaws can occur if victims open a specifically crafted Office document in a vulnerable version of Microsoft Office.
If Alex finds out that approximately 15 of the workstations in his organization have been compromised by this malware, including one workstation belonging to a domain administrator, what phase of the incident response process should he enter next?
- Preparation
- Detection and analysis
- Containment, eradication, and recovery
- Postincident activity