Chapter 2
Domain 2: Vulnerability Management
EXAM OBJECTIVES COVERED IN THIS CHAPTER:
 2.1 Given a scenario, implement an information security vulnerability management process.
2.1 Given a scenario, implement an information security vulnerability management process.- Identification of requirements
- Establish scanning frequency
- Configure tools to perform scans according to specification
- Execute scanning
- Generate reports
- Remediation
- Ongoing scanning and continuous monitoring
 2.2 Given a scenario, analyze the output resulting from a vulnerability scan.
2.2 Given a scenario, analyze the output resulting from a vulnerability scan.- Analyze reports from a vulnerability scan
- Validate results and correlate other data points
 2.3 Compare and contrast common vulnerabilities found in the following targets within an organization.
2.3 Compare and contrast common vulnerabilities found in the following targets within an organization.- Servers
- Endpoints
- Network infrastructure
- Network appliances
- Virtual infrastructure
- Mobile devices
- Interconnected networks
- Virtual private networks (VPNs)
- Industrial Control Systems (ICSs)
- SCADA devices
-
Kim is preparing to deploy a new vulnerability scanner and wants to ensure that she can get the most accurate view of configuration issues on laptops belonging to traveling salespeople. Which technology will work best in this situation?
- Agent-based scanning
- Server-based scanning
- Passive network monitoring
- Noncredentialed scanning
-
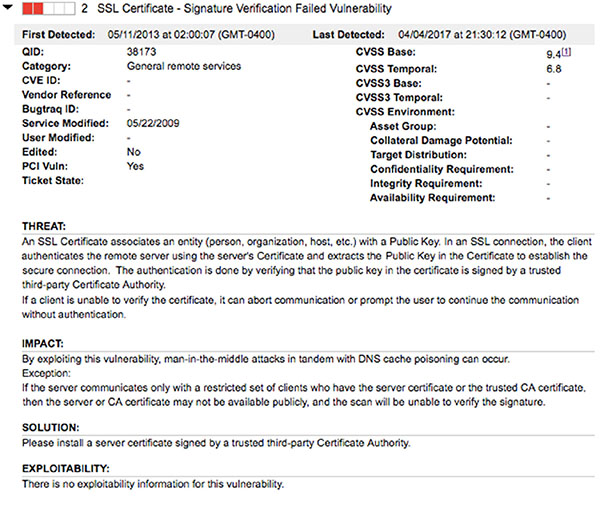
Carla runs a vulnerability scan of a new appliance that engineers are planning to place on her organization’s network and finds the results shown here. Of the actions listed, which would correct the highest criticality vulnerability?

- Block the use of TLSv1.0.
- Replace the expired SSL certificate.
- Remove the load balancer.
- Correct the information leakage vulnerability.
-
In what type of attack does the adversary leverage a position on a guest operating system to gain access to hardware resources assigned to other operating systems running in the same hardware environment?
- Buffer overflow
- Directory traversal
- VM escape
- Cross-site scripting
-
Julie is developing a vulnerability scanning approach that will unify the diverse approaches used throughout her organization’s different operating locations. She would like to ensure that everyone uses the same terminology when referring to different applications and operating systems. Which SCAP component can assist Julie with this task?
- CVE
- CPE
- CVSS
- OVAL
-
Josh is responsible for the security of a network used to control systems within his organization’s manufacturing plant. The network connects manufacturing equipment, sensors, and controllers. He runs a vulnerability scan on this network and discovers that several of the controllers are running very out-of-date firmware that introduces security issues. The manufacturer of the controllers is out of business. What action can Josh take to best remediate this vulnerability in an efficient manner?
- Develop a firmware update internally and apply it to the controllers.
- Post on an Internet message board seeking other organizations that have developed a patch.
- Ensure that the ICS is on an isolated network.
- Use an intrusion prevention system on the ICS network.
-
Vic scanned a Windows server used in his organization and found the result shown here. The server is on an internal network with access limited to IT staff and is not part of a domain. How urgently should Vic remediate this vulnerability?

- Vic should drop everything and remediate this vulnerability immediately.
- While Vic does not need to drop everything, this vulnerability requires urgent attention and should be addressed quickly.
- This is a moderate vulnerability that can be scheduled for remediation at a convenient time.
- This vulnerability is informational in nature and may be left in place.
-
Gina would like to leverage the Security Content Automation Protocol (SCAP) in her organization to bring a standard approach to their vulnerability management efforts. What SCAP component can Gina use to provide a common language for describing vulnerabilities?
- XCCDF
- CVE
- CPE
- CCE
-
Rob’s manager recently asked him for an overview of any critical security issues that exist on his network. He looks at the reporting console of his vulnerability scanner and sees the options shown here. Which of the following report types would be his best likely starting point?

- Technical Report
- High Severity Report
- Qualys Patch Report
- Unknown Device Report
-
Wendy is the security administrator for a membership association that is planning to launch an online store. As part of this launch, she will become responsible for ensuring that the website and associated systems are compliant with all relevant standards. What regulatory regime specifically covers credit card information?
- PCI DSS
- FERPA
- HIPAA
- SOX
-
During a port scan of a server, Miguel discovered that the following ports are open on the internal network:
- TCP port 25
- TCP port 80
- TCP port 110
- TCP port 443
- TCP port 1433
- TCP port 3389
The scan results provide evidence that a variety of services are running on this server. Which one of the following services is not indicated by the scan results?
- Web
- Database
- SSH
- RDP
-
Beth is a software developer and she receives a report from her company’s cybersecurity team that a vulnerability scan detected a SQL injection vulnerability in one of her applications. She examines her code and makes a modification in a test environment that she believes corrects the issue. What should she do next?
- Deploy the code to production immediately to resolve the vulnerability.
- Request a scan of the test environment to confirm that the issue is corrected.
- Mark the vulnerability as resolved and close the ticket.
- Hire a consultant to perform a penetration test to confirm that the vulnerability is resolved.
-
George recently ran a port scan on a network device used by his organization. Which one of the following open ports represents the most significant possible security vulnerability?
- 22
- 23
- 161
- 443
Questions 13 through 15 refer to the following scenario:
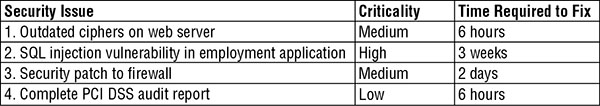
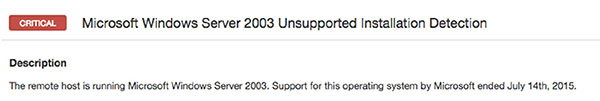
Harold runs a vulnerability scan of a server that he is planning to move into production and finds the vulnerability shown here.

-
What operating system is most likely running on the server in this vulnerability scan report?
- macOS
- Windows
- CentOS
- RHEL
-
Harold is preparing to correct the vulnerability. What service should he inspect to identify the issue?
- SSH
- HTTPS
- RDP
- SFTP
-
Harold would like to secure the service affected by this vulnerability. Which one of the following protocols/versions would be an acceptable way to resolve the issue?
- SSL v2.0
- SSL v3.0
- TLS v1.0
- None of the above
-
Seth found the vulnerability shown here in one of the systems on his network. What component requires a patch to correct this issue?

- Operating system
- VPN concentrator
- Network router or switch
- Hypervisor
-
Ken is responsible for the security of his organization’s network. His company recently contracted with a vendor that will be using laptops that he does not control to connect to their systems. Ken is concerned because he believes that these laptops contain vulnerabilities. What can he do to best mitigate the risk to other devices on the network without having administrative access to the devices?
- Apply any necessary security patches.
- Increase the encryption level of the VPN.
- Implement a jumpbox system.
- Require two-factor authentication.
-
Quentin ran a vulnerability scan of a server in his organization and discovered the results shown here. Which one of the following actions is not required to resolve one of the vulnerabilities on this server?

- Reconfigure cipher support.
- Apply Window security patches.
- Obtain a new SSL certificate.
- Enhance account security policies.
-
The presence of ____________ triggers specific vulnerability scanning requirements based upon law or regulation.
- Credit card information
- Protected health information
- Personally identifiable information
- Trade secret information
Questions 20 through 22 refer to the following scenario:
- Stella is analyzing the results of a vulnerability scan and comes across the vulnerability shown here on a server in her organization. The SharePoint service in question processes all of the organization’s work orders and is a critical part of the routine business workflow.

-
What priority should Stella place on remediating this vulnerability?
- Stella should make this vulnerability one of her highest priorities.
- Stella should remediate this vulnerability within the next several weeks.
- Stella should remediate this vulnerability within the next several months.
- Stella does not need to assign any priority to remediating this vulnerability.
-
What operating system is most likely running on the server in this vulnerability scan report?
- macOS
- Windows
- CentOS
- RHEL
-
What is the best way that Stella can correct this vulnerability?
- Deploy an intrusion prevention system.
- Apply one or more application patches.
- Apply one or more operating system patches.
- Disable the service.
-
Harry is developing a vulnerability scanning program for a large network of sensors used by his organization to monitor a transcontinental gas pipeline. What term is commonly used to describe this type of sensor network?
- WLAN
- VPN
- P2P
- SCADA
-
This morning, Eric ran a vulnerability scan in an attempt to detect a vulnerability that was announced by a software manufacturer yesterday afternoon. The scanner did not detect the vulnerability although Eric knows that at least two of his servers should have the issue. Eric contacted the vulnerability scanning vendor who assured him that they released a signature for the vulnerability overnight. What should Eric do as a next step?
- Check the affected servers to verify a false positive.
- Check the affected servers to verify a false negative.
- Report a bug to the vendor.
- Update the vulnerability signatures.
-
Natalie ran a vulnerability scan of a web application recently deployed by her organization, and the scan result reported a blind SQL injection. She reported the vulnerability to the developers who scoured the application and made a few modifications but did not see any evidence that this attack was possible. Natalie reran the scan and received the same result. The developers are now insisting that their code is secure. What is the most likely scenario?
- The result is a false positive.
- The code is deficient and requires correction.
- The vulnerability is in a different web application running on the same server.
- Natalie is misreading the scan report.
-
Frank discovers a missing Windows security patch during a vulnerability scan of a server in his organization’s data center. Upon further investigation, he discovers that the system is virtualized. Where should he apply the patch?
- To the virtualized system
- The patch is not necessary
- To the domain controller
- To the virtualization platform
-
Andrew is frustrated at the high level of false positive reports produced by his vulnerability scans and is contemplating a series of actions designed to reduce the false positive rate. Which one of the following actions is least likely to have the desired effect?
- Moving to credentialed scanning
- Moving to agent-based scanning
- Integrating asset information into the scan
- Increasing the sensitivity of scans
-
Joe is conducting a network vulnerability scan against his data center and receives reports from system administrators that the scans are slowing down their systems. There are no network connectivity issues, only performance problems on individual hosts. He looks at the scan settings shown here. Which setting would be most likely to correct the problem?

- Scan IP addresses in a random order
- Network timeout (in seconds)
- Max simultaneous checks per host
- Max simultaneous hosts per scan
-
Brenda runs a vulnerability scan of the management interface for her organization’s DNS service. She receives the vulnerability report shown here. What should be Brenda’s next action?

- Disable the use of cookies on this service.
- Request that the vendor rewrite the interface to avoid this vulnerability.
- Investigate the contents of the cookie.
- Shut down the DNS service.
-
Donna is prioritizing vulnerability scans and would like to base the frequency of scanning on the information asset value. Which of the following criteria would be most appropriate for her to use in this analysis?
- Cost of hardware acquisition
- Cost of hardware replacement
- Types of information processed
- Depreciated hardware cost
-
Laura is working to upgrade her organization’s vulnerability management program. She would like to add technology that is capable of retrieving the configurations of systems, even when they are highly secured. Many systems use local authentication, and she wants to avoid the burden of maintaining accounts on all of those systems. What technology should Laura consider to meet her requirement?
- Credentialed scanning
- Uncredentialed scanning
- Server-based scanning
- Agent-based scanning
-
Javier discovered the vulnerability shown here in a system on his network. He is unsure what system component is affected. What type of service is causing this vulnerability?

- Backup service
- Database service
- File sharing
- Web service
-
Alicia runs a vulnerability scan of a server being prepared for production and finds the vulnerability shown here. Which one of the following actions is least likely to reduce this risk?

- Block all connections on port 22.
- Upgrade OpenSSH.
- Disable AES-GCM in the server configuration.
- Install a network IPS in front of the server.
-
After scanning his organization’s email server, Frank discovered the vulnerability shown here. What is the most effective response that Frank can take in this situation?

- Upgrade to the most recent version of Microsoft Exchange.
- Upgrade to the most recent version of Microsoft Windows.
- Implement the use of strong encryption.
- No action is required.
-
A SQL injection exploit typically gains access to a database by exploiting a vulnerability in a(n) ____________.
- Operating system
- Web application
- Database server
- Firewall
Questions 36 through 38 refer to the following scenario:
Ryan ran a vulnerability scan of one of his organization’s production systems and received the report shown here. He would like to understand this vulnerability better and then remediate the issue.

-
Ryan will not be able to correct the vulnerability for several days. In the meantime, he would like to configure his intrusion prevention system to watch for issues related to this vulnerability. Which one of the following protocols would an attacker use to exploit this vulnerability?
- SSH
- HTTPS
- FTP
- RDP
-
Which one of the following actions could Ryan take to remediate the underlying issue without disrupting business activity?
- Disable the IIS service.
- Apply a security patch.
- Modify the web application.
- Apply IPS rules.
-
If an attacker is able to exploit this vulnerability, what is the probable result that will have the highest impact on the organization?
- Administrative control of the server
- Complete control of the domain
- Access to configuration information
- Access to web application logs
-
Ted is configuring vulnerability scanning for a file server on his company’s internal network. The server is positioned on the network as shown here. What types of vulnerability scans should Ted perform to balance the efficiency of scanning effort with expected results?

- Ted should not perform scans of servers on the internal network.
- Ted should only perform internal vulnerability scans.
- Ted should only perform external vulnerability scans.
- Ted should perform both internal and external vulnerability scans.
-
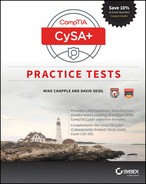
Kristen is attempting to determine the next task that she should take on from a list of security priorities. Her boss told her that she should focus on activities that have the most “bang for the buck.” Of the tasks shown here, which should she tackle first?
- Task 1
- Task 2
- Task 3
- Task 4
-
Kevin manages the vulnerability scans for his organization. The senior director that oversees Kevin’s group provides a report to the CIO on a monthly basis on operational activity, and he includes the number of open critical vulnerabilities. Kevin would like to provide this information to his director in as simple a manner as possible each month. What should Kevin do?
- Provide the director with access to the scanning system.
- Check the system each month for the correct number and email it to the director.
- Configure a report that provides the information to automatically send to the director’s email at the proper time each month.
- Ask an administrative assistant to check the system and provide the director with the information.
-
Morgan is interpreting the vulnerability scan from her organization’s network, shown here. She would like to determine which vulnerability to remediate first. Morgan would like to focus on vulnerabilities that are most easily exploitable by someone outside her organization. Assuming the firewall is properly configured, which one of the following vulnerabilities should Morgan give the highest priority?

- Severity 5 vulnerability in the workstation
- Severity 1 vulnerability in the file server
- Severity 5 vulnerability in the web server
- Severity 1 vulnerability in the mail server
-
Mike runs a vulnerability scan against his company’s virtualization environment and finds the vulnerability shown here in several of the virtual hosts. What action should Mike take?

- No action is necessary because this is an informational report.
- Mike should disable HTTP on the affected devices.
- Mike should upgrade the version of OpenSSL on the affected devices.
- Mike should immediately upgrade the hypervisor.
-
Juan recently scanned a system and found that it was running services on ports 139 and 445. What operating system is this system most likely running?
- Ubuntu
- macOS
- CentOS
- Windows
-
Gene is concerned about the theft of sensitive information stored in a database. Which one of the following vulnerabilities would pose the most direct threat to this information?
- SQL injection
- Cross-site scripting
- Buffer overflow
- Denial of service
-
Which one of the following protocols is not likely to trigger a vulnerability scan alert when used to support a virtual private network (VPN)?
- IPsec
- SSLv2
- PPTP
- SSLv3
-
Rahul ran a vulnerability scan of a server that will be used for credit card processing in his environment and received a report containing the vulnerability shown here. What action must Rahul take?

- Remediate the vulnerability when possible.
- Remediate the vulnerability prior to moving the system into production and rerun the scan to obtain a clean result.
- Remediate the vulnerability within 90 days of moving the system to production.
- No action is required.
Questions 48 and 49 refer to the following scenario:
Aaron is scanning a server in his organization’s data center and receives the vulnerability report shown here. The service is exposed only to internal hosts.

-
What is the normal function of the service with this vulnerability?
- File transfer
- Web hosting
- Time synchronization
- Network addressing
-
What priority should Aaron place on remediating this vulnerability?
- Aaron should make this vulnerability his highest priority.
- Aaron should remediate this vulnerability urgently but does not need to drop everything.
- Aaron should remediate this vulnerability within the next month.
- Aaron does not need to assign any priority to remediating this vulnerability.
-
Without access to any additional information, which one of the following vulnerabilities would you consider the most severe if discovered on a production web server?
- CGI generic SQL injection
- Web application information disclosure
- Web server uses basic authentication without HTTPS
- Web server directory enumeration
-
Gina ran a vulnerability scan on three systems that her organization is planning to move to production and received the results shown here. How many of these issues should Gina require be resolved before moving to production?

- 0.
- 1.
- 3.
- All of these issues should be resolved.
-
Morgan recently restarted an old vulnerability scanner that had not been used in more than a year. She booted the scanner, logged in, and configured a scan to run. After reading the scan results, she found that the scanner was not detecting known vulnerabilities that were detected by other scanners. What is the most likely cause of this issue?
- The scanner is running on an outdated operating system.
- The scanner’s maintenance subscription is expired.
- Morgan has invalid credentials on the scanner.
- The scanner does not have a current, valid IP address.
-
Carla runs both internal and external vulnerability scans of a web server and detects a possible SQL injection vulnerability. The vulnerability only appears in the internal scan and does not appear in the external scan. When Carla checks the server logs, she sees the requests coming from the internal scan and sees some requests from the external scanner but no evidence that a SQL injection exploit was attempted by the external scanner. What is the most likely explanation for these results?
- A host firewall is blocking external network connections to the web server.
- A network firewall is blocking external network connections to the web server.
- A host IPS is blocking some requests to the web server.
- A network IPS is blocking some requests to the web server.
-
Rick discovers the vulnerability shown here in a server running in his data center. What characteristic of this vulnerability should concern him the most?

- It is the subject of a recent security bulletin.
- It has a CVSS score of 7.2.
- There are multiple Bugtraq and CVE IDs.
- It affects kernel-mode drivers.
-
Carla is designing a vulnerability scanning workflow and has been tasked with selecting the person responsible for remediating vulnerabilities. Which one of the following people would normally be in the best position to remediate a server vulnerability?
- Cybersecurity analyst
- System administrator
- Network engineer
- IT manager
-
During a recent vulnerability scan, Ed discovered that a web server running on his network has access to a database server that should be restricted. Both servers are running on his organization’s VMware virtualization platform. Where should Ed look first to configure a security control to restrict this access?
- VMware
- Data center firewall
- Perimeter (Internet) firewall
- Intrusion prevention system
-
Carl runs a vulnerability scan of a mail server used by his organization and receives the vulnerability report shown here. What action should Carl take to correct this issue?

- Carl does not need to take any action because this is an informational report.
- Carl should replace SSL with TLS on this server.
- Carl should disable weak ciphers.
- Carl should upgrade OpenSSL.
-
Renee is configuring a vulnerability scanner that will run scans of her network. Corporate policy requires the use of daily vulnerability scans. What would be the best time to configure the scans?
- During the day when operations reach their peak to stress test systems
- During the evening when operations are minimal to reduce the impact on systems
- During lunch hour when people have stepped away from their systems but there is still considerable load
- On the weekends when the scans may run unimpeded
-
Ahmed is reviewing the vulnerability scan report from his organization’s central storage service and finds the results shown here. Which action can Ahmed take that will be effective in remediating the highest-severity issue possible?

- Upgrade to SNMPv3.
- Disable the use of RC4.
- Replace the use of SSL with TLS.
- Disable remote share enumeration.
Questions 60 and 61 refer to the following scenario:
Glenda ran a vulnerability scan of workstations in her organization. She noticed that many of the workstations reported the vulnerability shown here. She would like to not only correct this issue but also prevent the likelihood of similar issues occurring in the future.

-
What action should Glenda take to achieve her goals?
- Glenda should uninstall Chrome from all workstations and replace it with Internet Explorer.
- Glenda should manually upgrade Chrome on all workstations.
- Glenda should configure all workstations to automatically update Chrome.
- Glenda does not need to take any action.
-
What priority should Glenda place on remediating this vulnerability?
- Glenda should make this vulnerability her highest priority.
- Glenda should remediate this vulnerability urgently but does not need to drop everything.
- Glenda should remediate this vulnerability within the next several months.
- Glenda does not need to assign any priority to remediating this vulnerability.
-
After reviewing the results of a vulnerability scan, Beth discovered a flaw in her Oracle database server that may allow an attacker to attempt a direct connection to the server. She would like to review netflow logs to determine what systems have connected to the server recently. What TCP port should Beth expect to find used for this communication?
- 443
- 1433
- 1521
- 8080
-
Greg runs a vulnerability scan of a server in his organization and finds the results shown here. What is the most likely explanation for these results?

- The organization is running web services on nonstandard ports.
- The scanner is providing a false positive error report.
- The web server has mirrored ports available.
- The server has been compromised by an attacker.
-
Jim is reviewing a vulnerability scan of his organization’s VPN appliance. He wants to remove support for any insecure ciphers from the device. Which one of the following ciphers should he remove?
- ECDHE-RSA-AES128-SHA256
- AES256-SHA256
- DHE-RSA-AES256-GCM-SHA384
- EDH-RSA-DES-CBC3-SHA
-
Terry recently ran a vulnerability scan against his organization’s credit card processing environment that found a number of vulnerabilities. Which vulnerabilities must he remediate in order to have a “clean” scan under PCI DSS standards?
- Critical vulnerabilities
- Critical and high vulnerabilities
- Critical, high, and moderate vulnerabilities
- Critical, high, moderate, and low vulnerabilities
-
Beth discovers the vulnerability shown here on several Windows systems in her organization. There is a patch available, but it requires compatibility testing that will take several days to complete. What type of file should Beth be watchful for because it may directly exploit this vulnerability?
- Private key files
- Word documents
- Image files
- Encrypted files
-
During a vulnerability scan, Patrick discovered that the configuration management agent installed on all of his organization’s Windows servers contains a serious vulnerability. The manufacturer is aware of this issue, and a patch is available. What process should Patrick follow to correct this issue?
- Immediately deploy the patch to all affected systems.
- Deploy the patch to a single production server for testing and then deploy to all servers if that test is successful.
- Deploy the patch in a test environment and then conduct a staged rollout in production.
- Disable all external access to systems until the patch is deployed.
-
Matthew is creating a new forum for system engineers from around his organization to discuss security configurations of their systems. What SCAP component can Matthew take advantage of to help administrators have a standard language for discussing configuration issues?
- CPE
- CVE
- CCE
- CVSS
-
Aaron is configuring a vulnerability scan for a Class C network and is trying to choose a port setting from the list shown here. He would like to choose a scan option that will efficiently scan his network but also complete in a reasonable period of time. Which setting would be most appropriate?

- None
- Full
- Standard Scan
- Light Scan
-
Hunter discovered that a server in his organization has a critical web application vulnerability and would like to review the logs. The server is running Apache on CentOS with a default configuration. What is the name of the file where Hunter would expect to find the logs?
- httpd_log
- apache_log
- access_log
- http_log
-
Ken is reviewing the results of a vulnerability scan, shown here, from a web server in his organization. Access to this server is restricted at the firewall so that it may not be accessed on port 80 or 443. Which of the following vulnerabilities should Ken still address?

- OpenSSL version
- Cookie information disclosure
- TRACK/TRACE methods
- Ken does not need to address any of these vulnerabilities because they are not exposed to the outside world
-
Brian is considering the use of several different categories of vulnerability plug-ins. Of the types listed here, which is the most likely to result in false positive reports?
- Registry inspection
- Banner grabbing
- Service interrogation
- Fuzzing
-
Rob conducts a vulnerability scan and finds three different vulnerabilities, with the CVSS scores shown here. Which vulnerability should be his highest priority to fix, assuming all three fixes are of equal difficulty?

- Vulnerability 1
- Vulnerability 2
- Vulnerability 3
- Vulnerabilities 1 and 3 are equal in priority.
-
Which one of the following is not an appropriate criteria to use when prioritizing the remediation of vulnerabilities?
- Network exposure of the affected system
- Difficulty of remediation
- Severity of the vulnerability
- All of these are appropriate.
-
Landon is preparing to run a vulnerability scan of a dedicated Apache server that his organization is planning to move into a DMZ. Which one of the following vulnerability scans is least likely to provide informative results?
- Web application vulnerability scan
- Database vulnerability scan
- Port scan
- Network vulnerability scan
-
Ken recently received the vulnerability report shown here that affects a file server used by his organization. What is the primary nature of the risk introduced by this vulnerability?

- Confidentiality
- Integrity
- Availability
- Nonrepudiation
-
Molly is assessing the criticality of a vulnerability discovered on her organization’s network. It has the CVSS information shown here. What is the greatest risk exposed by this server?

- Confidentiality
- Integrity
- Availability
- There is no risk associated with this vulnerability.
-
Bill is creating a vulnerability management program for his company. He has limited scanning resources and would like to apply them to different systems based upon the sensitivity and criticality of the information that they handle. What criteria should Bill use to determine the vulnerability scanning frequency?
- Data remnance
- Data privacy
- Data classification
- Data privacy
-
Tom recently read a media report about a ransomware outbreak that was spreading rapidly across the Internet by exploiting a zero-day vulnerability in Microsoft Windows. As part of a comprehensive response, he would like to include a control that would allow his organization to effectively recover from a ransomware infection. Which one of the following controls would best achieve Tom’s objective?
- Security patching
- Host firewalls
- Backups
- Intrusion prevention systems
-
Kaitlyn discovered the vulnerability shown here on a workstation in her organization. Which one of the following is not an acceptable method for remediating this vulnerability?

- Upgrade WinRAR.
- Upgrade Windows.
- Remove WinRAR.
- Replace WinRAR with an alternate compression utility.
-
Brent ran a vulnerability scan of several network infrastructure devices on his network and obtained the result shown here. What is the extent of the impact that an attacker could have by exploiting this vulnerability directly?

- Denial of service
- Theft of sensitive information
- Network eavesdropping
- Reconnaissance
-
Ted runs the cybersecurity vulnerability management program for his organization. He sends a database administrator a report of a missing database patch that corrects a high severity security issue. The DBA writes back to Ted that he has applied the patch. Ted reruns the scan, and it still reports the same vulnerability. What should Ted do next?
- Mark the vulnerability as a false positive.
- Ask the DBA to recheck the database.
- Mark the vulnerability as an exception.
- Escalate the issue to the DBA’s manager.
-
Miranda is reviewing the results of a vulnerability scan and identifies the issue shown here in one of her systems. She consults with developers who check the code and assure her that it is not vulnerable to SQL injection attacks. An independent auditor confirms this for Miranda. What is the most likely scenario?

- This is a false positive report.
- The developers are wrong, and the vulnerability exists.
- The scanner is malfunctioning.
- The database server is misconfigured.
-
Eric is reviewing the results of a vulnerability scan and comes across the vulnerability report shown here. Which one of the following services is least likely to be affected by this vulnerability?

- HTTPS
- HTTP
- SSH
- VPN
Questions 85 and 86 refer to the following scenario:
Larry recently discovered a critical vulnerability in one of his organization’s database servers during a routine vulnerability scan. When he showed the report to a database administrator, the administrator responded that they had corrected the vulnerability by using a vendor-supplied workaround because upgrading the database would disrupt an important process. Larry verified that the workaround is in place and corrects the vulnerability.
-
How should Larry respond to this situation?
- Mark the report as a false positive.
- Insist that the administrator apply the vendor patch.
- Mark the report as an exception.
- Require that the administrator submit a report describing the workaround after each vulnerability scan.
-
What is the most likely cause of this report?
- The vulnerability scanner requires an update.
- The vulnerability scanner depends upon version detection.
- The database administrator incorrectly applied the workaround.
- Larry misconfigured the scan.
-
Breanne ran a vulnerability scan of a server in her organization and found the vulnerability shown here. What is the use of the service affected by this vulnerability?

- Web server
- Database server
- Email server
- Directory server
-
Margot discovered that a server in her organization has a SQL injection vulnerability. She would like to investigate whether attackers have attempted to exploit this vulnerability. Which one of the following data sources is least likely to provide helpful information?
- Netflow logs
- Web server logs
- Database logs
- IDS logs
-
Krista is reviewing a vulnerability scan report and comes across the vulnerability shown here. She comes from a Linux background and is not as familiar with Windows administration. She is not familiar with the runas command mentioned in this vulnerability. What is the closest Linux equivalent command?

- sudo
- grep
- su
- ps
-
After scanning a web application for possible vulnerabilities, Barry received the result shown here. Which one of the following best describes the threat posed by this vulnerability?

- An attacker can eavesdrop on authentication exchanges.
- An attacker can cause a denial-of-service attack on the web application.
- An attacker can disrupt the encryption mechanism used by this server.
- An attacker can edit the application code running on this server.
-
Michelle would like to share information about vulnerabilities with partner organizations who use different vulnerability scanning products. What component of SCAP can best assist her in ensuring that the different organizations are talking about the same vulnerabilities?
- CPE
- CVE
- CVSS
- OVAL
-
Javier ran a vulnerability scan of a network device used by his organization and discovered the vulnerability shown here. What type of attack would this vulnerability enable?

- Denial of service
- Information theft
- Information alteration
- Reconnaissance
-
Amanda scans a Windows server in her organization and finds that it has multiple critical vulnerabilities, detailed in the report shown here. What action can Amanda take that will have the most significant impact on these issues without creating a long-term outage?

- Configure the host firewall to block inbound connections.
- Apply security patches.
- Disable the guest account on the server.
- Configure the server to only use secure ciphers.
-
Ben is preparing to conduct a vulnerability scan for a new client of his security consulting organization. Which one of the following steps should Ben perform first?
- Conduct penetration testing.
- Run a vulnerability evaluation scan.
- Run a discovery scan.
- Obtain permission for the scans.
-
Katherine coordinates the remediation of security vulnerabilities in her organization and is attempting to work with a system engineer on the patching of a server to correct a moderate impact vulnerability. The engineer is refusing to patch the server because of the potential interruption to a critical business process that runs on the server. What would be the most reasonable course of action for Katherine to take?
- Schedule the patching to occur during a regular maintenance cycle.
- Exempt the server from patching because of the critical business impact.
- Demand that the server be patched immediately to correct the vulnerability.
- Inform the engineer that if he does not apply the patch within a week that Katherine will file a complaint with his manager.
-
During a recent vulnerability scan of workstations on her network, Andrea discovered the vulnerability shown here. Which one of the following actions is least likely to remediate this vulnerability?

- Remove JRE from workstations.
- Upgrade JRE to the most recent version.
- Block inbound connections on port 80 using the host firewall.
- Use a web content filtering system to scan for malicious traffic.
-
Grace ran a vulnerability scan and detected an urgent vulnerability in a public-facing web server. This vulnerability is easily exploitable and could result in the complete compromise of the server. Grace wants to follow best practices regarding change control while also mitigating this threat as quickly as possible. What would be Grace’s best course of action?
- Initiate a high-priority change through her organization’s change management process and wait for the change to be approved.
- Implement a fix immediately and document the change after the fact.
- Schedule a change for the next quarterly patch cycle.
- Initiate a standard change through her organization’s change management process.
-
Doug is preparing an RFP for a vulnerability scanner for his organization. He needs to know the number of systems on his network to help determine the scanner requirements. Which one of the following would not be an easy way to obtain this information?
- ARP tables
- Asset management tool
- Discovery scan
- Results of scans recently run by a consultant
-
Mary runs a vulnerability scan of her entire organization and shares the report with another analyst on her team. An excerpt from that report appears here. Her colleague points out that the report contains only vulnerabilities with severities of 3, 4, or 5. What is the most likely cause of this result?

- The scan sensitivity is set to exclude low-importance vulnerabilities.
- Mary did not configure the scan properly.
- Systems in the data center do not contain any level 1 or 2 vulnerabilities.
- The scan sensitivity is set to exclude high-impact vulnerabilities.
-
James is reviewing the vulnerability shown here, which was detected on several servers in his environment. What action should James take?

- Block TCP/IP access to these servers from external sources.
- Upgrade the operating system on these servers.
- Encrypt all access to these servers.
- No action is necessary.
-
Which one of the following approaches provides the most current and accurate information about vulnerabilities present on a system because of the misconfiguration of operating system settings?
- On-demand vulnerability scanning
- Continuous vulnerability scanning
- Scheduled vulnerability scanning
- Agent-based monitoring
Questions 102 through 104 refer to the following scenario:
Pete recently conducted a broad vulnerability scan of all the servers and workstations in his environment. He scanned the following three networks:
- DMZ network that contains servers with public exposure
- Workstation network that contains workstations that are allowed outbound access only
- Internal server network that contains servers exposed only to internal systems
He detected the following vulnerabilities:
- Vulnerability 1: A SQL injection vulnerability on a DMZ server that would grant access to a database server on the internal network (severity 5/5)
- Vulnerability 2: A buffer overflow vulnerability on a domain controller on the internal server network (severity 3/5)
- Vulnerability 3: A missing security patch on several hundred Windows workstations on the workstation network (severity 2/5)
- Vulnerability 4: A denial-of-service vulnerability on a DMZ server that would allow an attacker to disrupt a public-facing website (severity 2/5)
- Vulnerability 5: A denial of service vulnerability on an internal server that would allow an attacker to disrupt an internal website (severity 4/5)
- Note that the severity ratings assigned to these vulnerabilities are directly from the vulnerability scanner and were not assigned by Pete.
-
Absent any other information, which one of the vulnerabilities in the report should Pete remediate first?
- Vulnerability 1
- Vulnerability 2
- Vulnerability 3
- Vulnerability 4
-
Pete is working with the desktop support manager to remediate vulnerability 3. What would be the most efficient way to correct this issue?
- Personally visit each workstation to remediate the vulnerability.
- Remotely connect to each workstation to remediate the vulnerability.
- Perform registry updates using a remote configuration tool.
- Apply the patch using a GPO.
-
Pete recently conferred with the organization’s CISO, and the team is launching an initiative designed to combat the insider threat. They are particularly concerned about the theft of information by employees seeking to exceed their authorized access. Which one of the vulnerabilities in this report is of greatest concern given this priority?
- Vulnerability 2
- Vulnerability 3
- Vulnerability 4
- Vulnerability 5
-
Wanda recently discovered the vulnerability shown here on a Windows server in her organization. She is unable to apply the patch to the server for six weeks because of operational issues. What workaround would be most effective in limiting the likelihood that this vulnerability would be exploited?

- Restrict interactive logins to the system.
- Remove Microsoft Office from the server.
- Remove Internet Explorer from the server.
- Apply the security patch.
-
Garrett is configuring vulnerability scanning for a new web server that his organization is deploying on its DMZ network. The server hosts the company’s public website. What type of scanning should Garrett configure for best results?
- Garrett should not perform scanning of DMZ systems.
- Garrett should perform external scanning only.
- Garrett should perform internal scanning only.
- Garrett should perform both internal and external scanning.
-
Frank recently ran a vulnerability scan and identified a POS terminal that contains an unpatchable vulnerability because of running an unsupported operating system. Frank consults with his manager and is told that the POS is being used with full knowledge of management and, as a compensating control, it has been placed on an isolated network with no access to other systems. Frank’s manager tells him that the merchant bank is aware of the issue. How should Frank handle this situation?
- Document the vulnerability as an approved exception.
- Explain to his manager that PCI DSS does not permit the use of unsupported operating systems.
- Decommission the POS system immediately to avoid personal liability.
- Upgrade the operating system immediately.
-
James is configuring vulnerability scans of a dedicated network that his organization uses for processing credit card transactions. What types of scans are least important for James to include in his scanning program?
- Scans from a dedicated scanner on the card processing network
- Scans from an external scanner on his organization’s network
- Scans from an external scanner operated by an approved scanning vendor
- All three types of scans are equally important.
-
Helen performs a vulnerability scan of one of the internal LANs within her organization and finds a report of a web application vulnerability on a device. Upon investigation, she discovers that the device in question is a printer. What is the most likely scenario in this case?
- The printer is running a web server.
- The report is a false positive result.
- The printer recently changed IP addresses.
- Helen inadvertently scanned the wrong network.
-
Joe discovered a critical vulnerability in his organization’s database server and received permission from his supervisor to implement an emergency change after the close of business. He has eight hours before the planned change window. In addition to planning the technical aspects of the change, what else should Joe do to prepare for the change?
- Ensure that all stakeholders are informed of the planned outage.
- Document the change in his organization’s change management system.
- Identify any potential risks associated with the change.
- All of the above
-
Julian recently detected the vulnerability shown here on several servers in his environment. Because of the critical nature of the vulnerability, he would like to block all access to the affected service until it is resolved using a firewall rule. He verifies that the following TCP ports are open on the host firewall. Which one of the following does Julian not need to block to restrict access to this service?

- 137
- 139
- 389
- 445
-
Ted recently ran a vulnerability scan of his network and was overwhelmed with results. He would like to focus on the most important vulnerabilities. How should Ted reconfigure his vulnerability scanner?
- Increase the scan sensitivity.
- Decrease the scan sensitivity.
- Increase the scan frequency.
- Decrease the scan frequency.
-
After running a vulnerability scan, Janet discovered that several machines on her network are running Internet Explorer 8 and reported the vulnerability shown here. Which one of the following would not be a suitable replacement browser for these systems?

- Internet Explorer 10
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
-
Sunitha discovered the vulnerability shown here in an application developed by her organization. What application security technique is most likely to resolve this issue?

- Bounds checking
- Network segmentation
- Parameter handling
- Tag removal
-
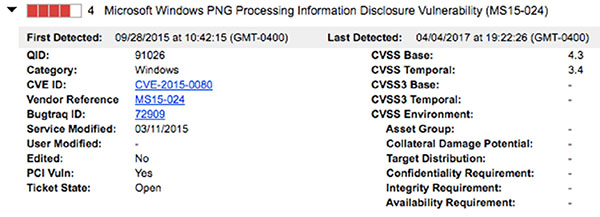
Pete ran a vulnerability scan of several network appliances in his organization and received the scan result shown here. What is the simplest tool that an attacker could use to cause a denial-of-service attack on these appliances, provided that they are running ClearCase?
- Metasploit
- Nessus
- nmap
- Wireshark
-
Which one of the following protocols might be used within a virtualization platform for monitoring and management of the network?
- SNMP
- SMTP
- BGP
- EIGRP
-
Sherry runs a vulnerability scan and receives the high-level results shown here. Her priority is to remediate the most important vulnerabilities first. Which system should be her highest priority?
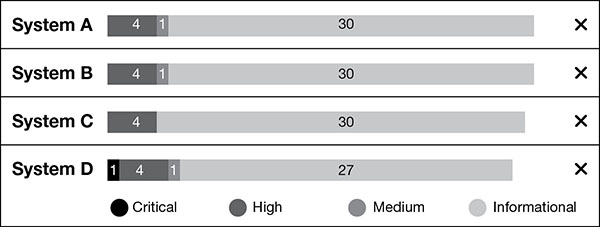
- A
- B
- C
- D
-
Victor is configuring a new vulnerability scanner. He set the scanner to run scans of his entire data center each evening. When he went to check the scan reports at the end of the week, he found that they were all incomplete. The scan reports noted the error “Scan terminated due to start of preempting job.” Victor has no funds remaining to invest in the vulnerability scanning system. He does want to cover the entire data center. What should he do to ensure that scans complete?
- Reduce the number of systems scanned.
- Increase the number of scanners.
- Upgrade the scanner hardware.
- Reduce the scanning frequency.
-
Vanessa ran a vulnerability scan of a server and received the results shown here. Her boss instructed her to prioritize remediation based upon criticality. Which issue should she address first?

- Remove the POP server.
- Remove the FTP server.
- Upgrade the web server.
- Remove insecure cryptographic protocols.
-
Gil is configuring a scheduled vulnerability scan for his organization using the QualysGuard scanner. If he selects the Relaunch On Finish scheduling option shown here, what will be the result?

- The scan will run once each time the schedule occurs.
- The scan will run twice each time the schedule occurs.
- The scan will run twice the next time the schedule occurs and once on each subsequent schedule interval.
- The scan will run continuously until stopped.
-
Terry is reviewing a vulnerability scan of a Windows server and came across the vulnerability shown here. What is the risk presented by this vulnerability?

- An attacker may be able to execute a buffer overflow and execute arbitrary code on the server.
- An attacker may be able to conduct a denial-of-service attack against this server.
- An attacker may be able to determine the operating system version on this server.
- There is no direct vulnerability, but this information points to other possible vulnerabilities on the server.
-
Andrea recently discovered the vulnerability shown here on the workstation belonging to a system administrator in her organization. What is the major likely threat that should concern Andrea?

- An attacker could exploit this vulnerability to take control of the administrator’s workstation.
- An attacker could exploit this vulnerability to gain access to servers managed by the administrator.
- An attacker could exploit this vulnerability to prevent the administrator from using the workstation.
- An attacker could exploit this vulnerability to decrypt sensitive information stored on the administrator’s workstation.
-
Craig completed the vulnerability scan of a server in his organization and discovered the results shown here. Which one of the following is not a critical remediation action dictated by these results?

- Remove obsolete software.
- Reconfigure the host firewall.
- Apply operating system patches.
- Apply application patches.
-
Tom’s company is planning to begin a bring your own device (BYOD) policy for mobile devices. Which one of the following technologies allows the secure use of sensitive information on personally owned devices, including providing administrators with the ability to wipe corporate information from the device without affecting personal data?
- Remote wipe
- Strong passwords
- Biometric authentication
- Containerization
-
Sally discovered during a vulnerability scan that a system that she manages has a high-priority vulnerability that requires a patch. The system is behind a firewall and there is no imminent threat, but Sally wants to get the situation resolved as quickly as possible. What would be her best course of action?
- Initiate a high-priority change through her organization’s change management process.
- Implement a fix immediately and then document the change after the fact.
- Implement a fix immediately and then inform her supervisor of her action and the rationale.
- Schedule a change for the next quarterly patch cycle.
-
Gene runs a vulnerability scan of his organization’s data center and produces a summary report to share with his management team. The report includes the chart shown here. When Gene’s manager reads the report, she points out that the report is burying important details because it is highlighting too many unimportant issues. What should Gene do to resolve this issue?

- Tell his manager that all vulnerabilities are important and should appear on the report.
- Create a revised version of the chart using Excel.
- Modify the sensitivity level of the scan.
- Stop sharing reports with the management team.
-
Veronica recently conducted a PCI DSS vulnerability scan of a web server and noted a critical PHP vulnerability that required an upgrade to correct. She applied the update. How soon must Veronica repeat the scan?
- Within 30 days
- At the next scheduled quarterly scan
- At the next scheduled annual scan
- Immediately
-
Chandra’s organization recently upgraded the firewall protecting the network where they process credit card information. This network is subject to the provisions of PCI DSS. When is Chandra required to schedule the next vulnerability scan of this network?
- Immediately
- Within one month
- Before the start of next month
- Before the end of the quarter following the upgrade
-
Bruce is concerned about the security of an industrial control system that his organization uses to monitor and manage systems in their factories. He would like to reduce the risk of an attacker penetrating this system. Which one of the following security controls would best mitigate the vulnerabilities in this type of system?
- Network segmentation
- Input validation
- Memory protection
- Redundancy
-
Glenda routinely runs vulnerability scans of servers in her organization. She is having difficulty with one system administrator who refuses to correct vulnerabilities on a server used as a jumpbox by other IT staff. The server has had dozens of vulnerabilities for weeks and would require downtime to repair. One morning, her scan reports that all of the vulnerabilities suddenly disappeared overnight, while other systems in the same scan are reporting issues. She checks the service status dashboard, and the service appears to be running properly with no outages reported in the past week. What is the most likely cause of this result?
- The system administrator corrected the vulnerabilities.
- The server is down.
- The system administrator blocked the scanner.
- The scan did not run.
-
Frank discovered during a vulnerability scan that an administrative interface to one of his storage systems was inadvertently exposed to the Internet. He is reviewing firewall logs and would like to determine whether any access attempts came from external sources. Which one of the following IP addresses reflects an external source?
- 10.15.1.100
- 12.8.1.100
- 172.16.1.100
- 192.168.1.100
-
Nick is configuring vulnerability scans for his network using a third-party vulnerability scanning service. He is attempting to scan a web server that he knows exposes a CIFS file share and contains several significant vulnerabilities. However, the scan results only show ports 80 and 443 as open. What is the most likely cause of these scan results?
- The CIFS file share is running on port 443.
- A firewall configuration is preventing the scan from succeeding.
- The scanner configuration is preventing the scan from succeeding.
- The CIFS file share is running on port 80.
-
Thomas learned this morning of a critical security flaw that affects a major service used by his organization and requires immediate patching. This flaw was the subject of news reports and is being actively exploited. Thomas has a patch and informed stakeholders of the issue and received permission to apply the patch during business hours. How should he handle the change management process?
- Thomas should apply the patch and then follow up with an emergency change request after work is complete.
- Thomas should initiate a standard change request but apply the patch before waiting for approval.
- Thomas should work through the standard change approval process and wait until it is complete to apply the patch.
- Thomas should file an emergency change request and wait until it is approved to apply the patch.
Questions 134 through 136 refer to the bare-metal virtualization environment shown here:

-
What component is identified by A in the image?
- Hypervisor
- Host operating system
- Guest operating system
- Physical hardware
-
What component is identified by B in the image?
- Hypervisor
- Host operating system
- Guest operating system
- Physical hardware
-
What component is identified by C in the image?
- Hypervisor
- Host operating system
- Guest operating system
- Physical hardware
-
After running a vulnerability scan of systems in his organization’s development shop, Mike discovers the issue shown here on several systems. What is the best solution to this vulnerability?

- Apply the required security patches to this framework.
- Remove this framework from the affected systems.
- Upgrade the operating system of the affected systems.
- No action is necessary.
-
Chris is preparing to conduct vulnerability scans against a set of workstations in his organization. He is particularly concerned about system configuration settings. Which one of the following scan types will give him the best results?
- Unauthenticated scan
- Credentialed scan
- External scan
- Internal scan
-
Brian is configuring a vulnerability scan of all servers in his organization’s data center. He is configuring the scan to only detect the highest-severity vulnerabilities. He would like to empower system administrators to correct issues on their servers but also have some insight into the status of those remediations. Which approach would best serve Brian’s interests?
- Give the administrators access to view the scans in the vulnerability scanning system.
- Send email alerts to administrators when the scans detect a new vulnerability on their servers.
- Configure the vulnerability scanner to open a trouble ticket when they detect a new vulnerability on a server.
- Configure the scanner to send reports to Brian who can notify administrators and track them in a spreadsheet.
-
Tonya is configuring a new vulnerability scanner for use in her organization’s data center. Which one of the following values is considered a best practice for the scanner’s update frequency?
- Daily
- Weekly
- Monthly
- Quarterly
-
Ben was recently assigned by his manager to begin the remediation work on the most vulnerable server in his organization. A portion of the scan report appears below. What remediation action should Ben take first?
- Install patches for Adobe Flash.
- Install patches for Firefox.
- Run Windows Update.
- Remove obsolete software.
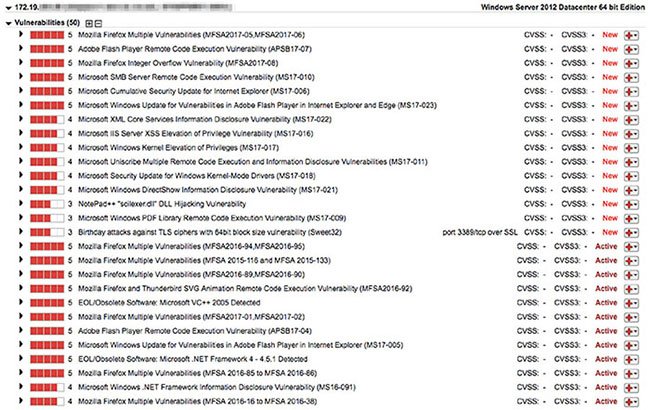
-
Tom is planning a series of vulnerability scans and wants to ensure that the organization is meeting its customer commitments with respect to the scans’ performance impact. What two documents should Tom consult to find these obligations?
- SLAs and MOUs
- SLAs and DRPs
- DRPs and BIAs
- BIAs and MOUs
-
Don is evaluating the success of his vulnerability management program and would like to include some metrics. Which one of the following would be the least useful metric?
- Time to resolve critical vulnerabilities
- Number of open critical vulnerabilities over time
- Total number of vulnerabilities reported
- Number of systems containing critical vulnerabilities
-
Don completed a vulnerability scan of his organization’s virtualization platform from an external host and discovered the vulnerability shown here. How should Don react?

- This is a critical issue that requires immediate adjustment of firewall rules.
- This issue has a very low severity and does not require remediation.
- This issue should be corrected as time permits.
- This is a critical issue, and Don should shut down the platform until it is corrected.
-
Elliott runs a vulnerability scan of one of the servers belonging to his organization and finds the results shown here. Which one of these statements is not correct?

- This server requires one or more Linux patches.
- This server requires one or more Oracle database patches.
- This server requires one or more Firefox patches.
- This server requires one or more MySQL patches.
-
Donna is working with a system engineer who wants to remediate vulnerabilities in a server that he manages. Of the report templates shown here, which would be most useful to the engineer?

- Qualys Top 20 Report
- PCI Technical Report
- Executive Report
- Technical Report
-
James received the vulnerability report shown here for a server in his organization. What risks does this vulnerability present?

- Unauthorized access to files stored on the server
- Theft of credentials
- Eavesdropping on communications
- All of the above
-
Tom runs a vulnerability scan of the file server shown here.

He receives the vulnerability report shown next. Assuming that the firewall is configured properly, what action should Tom take immediately?
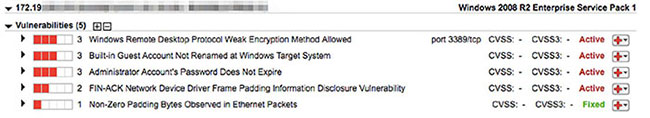
- Block RDP access to this server from all hosts.
- Review and secure server accounts.
- Upgrade encryption on the server.
- No action is required.
-
Dave is running a vulnerability scan of a client’s network for the first time. The client has never run such a scan and expects to find many results. What security control is likely to remediate the largest portion of the vulnerabilities discovered in Dave’s scan?
- Input validation
- Patching
- Intrusion prevention systems
- Encryption
-
Matt is working to integrate his organization’s network with that of a recently acquired company. He is concerned that the acquired company’s network contains systems with vulnerabilities that may be exploited and wants to protect his network against compromised hosts on the new network. Which one of the following controls would be least effective at reducing the risk from network interconnection?
- Network segmentation
- VLAN separation
- Firewall
- Proxy server
-
Rhonda is planning to patch a production system to correct a vulnerability detected during a scan. What process should she follow to correct the vulnerability but minimize the risk of a system failure?
- Rhonda should deploy the patch immediately on the production system.
- Rhonda should wait 60 days to deploy the patch to determine whether bugs are reported.
- Rhonda should deploy the patch in a sandbox environment to test it prior to applying it in production.
- Rhonda should contact the vendor to determine a safe timeframe for deploying the patch in production.
-
William is preparing a legal agreement for his organization to purchase services from a vendor. He would like to document the requirements for system availability, including the vendor’s allowable downtime for patching. What type of agreement should William use to incorporate this requirement?
- MOU
- SLA
- BPA
- BIA
-
Given no other information, which one of the following vulnerabilities would you consider the greatest threat to information confidentiality?
- HTTP TRACE/TRACK methods enabled
- SSL Server with SSLv3 enabled vulnerability
- phpinfo information disclosure vulnerability
- Web application SQL injection vulnerability
-
Which one of the following mobile device strategies is most likely to result in the introduction of vulnerable devices to a network?
- COPE
- TLS
- BYOD
- MDM
-
Kassie discovered the vulnerability shown here on one of the servers running in her organization. What action should she take?
- Decommission this server.
- Run Windows Update to apply security patches.
- Require strong encryption for access to this server.
- No action is required.
-
Morgan recently completed the security analysis of a web browser deployed on systems in her organization and discovered that it is susceptible to a zero-day integer overflow attack. Who is in the best position to remediate this vulnerability in a manner that allows continued use of the browser?
- Morgan
- The browser developer
- The network administrator
- The domain administrator
-
Jeff’s team is preparing to deploy a new database service, and he runs a vulnerability scan of the test environment. This scan results in the four vulnerability reports shown here. Jeff is primarily concerned with correcting issues that may lead to a confidentiality breach. Which vulnerability should Jeff remediate first?

- Rational ClearCase Portscan Denial of Service vulnerability
- Non-Zero Padding Bytes Observed in Ethernet Packets
- Oracle Database TNS Listener Poison Attack vulnerability
- Hidden RPC Services
-
Eric is a security consultant and is trying to sell his services to a new client. He would like to run a vulnerability scan of their network prior to their initial meeting to show the client the need for added security. What is the most significant problem with this approach?
- Eric does not know the client’s infrastructure design.
- Eric does not have permission to perform the scan.
- Eric does not know what operating systems and applications are in use.
- Eric does not know the IP range of the client’s systems.
-
Renee is assessing the exposure of her organization to the denial-of-service vulnerability in the scan report shown here. She is specifically interested in determining whether an external attacker would be able to exploit the denial-of-service vulnerability. Which one of the following sources of information would provide her with the best information to complete this assessment?

- Server logs
- Firewall rules
- IDS configuration
- DLP configuration
-
Mary is trying to determine what systems in her organization should be subject to vulnerability scanning. She would like to base this decision upon the criticality of the system to business operations. Where should Mary turn to best find this information?
- The CEO
- System names
- IP addresses
- Asset inventory
-
Paul ran a vulnerability scan of his vulnerability scanner and received the result shown here. What is the simplest fix to this issue?

- Upgrade Nessus.
- Remove guest accounts.
- Implement TLS encryption.
- Renew the server certificate.
-
Sarah is designing a vulnerability management system for her organization. Her highest priority is conserving network bandwidth. She does not have the ability to alter the configuration or applications installed on target systems. What solution would work best in Sarah’s environment to provide vulnerability reports?
- Agent-based scanning
- Server-based scanning
- Passive network monitoring
- Port scanning
-
Terry is conducting a vulnerability scan when he receives a report that the scan is slowing down the network for other users. He looks at the performance configuration settings shown here. Which setting would be most likely to correct the issue?

- Enable safe checks.
- Stop scanning hosts that become unresponsive during the scan.
- Scan IP addresses in random order.
- Max simultaneous hosts per scan.
-
Laura received a vendor security bulletin that describes a zero-day vulnerability in her organization’s main database server. This server is on a private network but is used by publicly accessible web applications. The vulnerability allows the decryption of administrative connections to the server. What reasonable action can Laura take to address this issue as quickly as possible?
- Apply a vendor patch that resolves the issue.
- Disable all administrative access to the database server.
- Require VPN access for remote connections to the database server.
- Verify that the web applications use strong encryption.
-
Emily discovered the vulnerability shown here on a server running in her organization. What is the most likely underlying cause for this vulnerability?

- Failure to perform input validation
- Failure to use strong passwords
- Failure to encrypt communications
- Failure to install antimalware software
-
Raul is replacing his organization’s existing vulnerability scanner with a new product that will fulfill that functionality moving forward. As Raul begins to build out the policy, he notices some conflicts in the scanning settings between different documents. Which one of the following document sources should Raul give the highest priority when resolving these conflicts?
- NIST guidance documents
- Vendor best practices
- Corporate policy
- Configuration settings from the prior system
-
Rex recently ran a vulnerability scan of his organization’s network and received the results shown here. He would like to remediate the server with the highest number of the most serious vulnerabilities first. Which one of the following servers should be on his highest priority list?

- 10.0.102.58
- 10.0.16.58
- 10.0.46.116
- 10.0.69.232
-
Beth is configuring a vulnerability scanning tool. She recently learned about a privilege escalation vulnerability that requires the user already have local access to the system. She would like to ensure that her scanners are able to detect this vulnerability as well as future similar vulnerabilities. What action can she take that would best improve the scanner’s ability to detect this type of issue?
- Enable credentialed scanning.
- Run a manual vulnerability feed update.
- Increase scanning frequency.
- Change the organization’s risk appetite.
-
Shannon reviewed the vulnerability scan report for a web server and found that it has multiple SQL injection and cross-site scripting vulnerabilities. What would be the least difficult way for Shannon to address these issues?
- Install a web application firewall.
- Recode the web application to include input validation.
- Apply security patches to the server operating system.
- Apply security patches to the web server service.
-
Ron is responsible for distributing vulnerability scan reports to system engineers who will remediate the vulnerabilities. What would be the most effective and secure way for Ron to distribute the reports?
- Ron should configure the reports to generate automatically and provide immediate, automated notification to administrators of the results.
- Ron should run the reports manually and send automated notifications after he reviews them for security purposes.
- Ron should run the reports on an automated basis and then manually notify administrators of the results after he reviews them.
- Ron should run the reports manually and then manually notify administrators of the results after he reviews them.
-
Karen ran a vulnerability scan of a web server used on her organization’s internal network. She received the report shown here. What circumstances would lead Karen to dismiss this vulnerability as a false positive?
- The server is running SSLv2.
- The server is running SSLv3.
- The server is for internal use only.
- The server does not contain sensitive information.
-
Which one of the following vulnerabilities is the most difficult to confirm with an external vulnerability scan?
- Cross-site scripting
- Cross-site request forgery
- Blind SQL injection
- Unpatched web server
-
Ann would like to improve her organization’s ability to detect and remediate security vulnerabilities by adopting a continuous monitoring approach. Which one of the following is not a characteristic of a continuous monitoring program?
- Analyzing and reporting findings
- Conducting forensic investigations when a vulnerability is exploited
- Mitigating the risk associated with findings
- Transferring the risk associated with a finding to a third party
-
Holly ran a scan of a server in her data center and the most serious result was the vulnerability shown here. What action is most commonly taken to remediate this vulnerability?

- Remove the file from the server.
- Edit the file to limit information disclosure.
- Password protect the file.
- Limit file access to a specific IP range.
-
Nitesh would like to identify any systems on his network that are not registered with his asset management system. He looks at the reporting console of his vulnerability scanner and sees the options shown here. Which of the following report types would be his best likely starting point?

- Technical Report
- High Severity Report
- Qualys Patch Report
- Unknown Device Report
-
What strategy can be used to immediately report configuration changes to a vulnerability scanner?
- Scheduled scans
- Continuous monitoring
- Automated remediation
- Automatic updates
-
During a recent vulnerability scan, Mark discovered a flaw in an internal web application that allows cross-site scripting attacks. He spoke with the manager of the team responsible for that application and was informed that he discovered a known vulnerability and the manager worked with other leaders and determined that the risk is acceptable and does not require remediation. What should Mark do?
- Object to the manager’s approach and insist upon remediation.
- Mark the vulnerability as a false positive.
- Schedule the vulnerability for remediation in six months.
- Mark the vulnerability as an exception.
-
Jacquelyn recently read about a new vulnerability in Apache web servers that allows attackers to execute arbitrary code from a remote location. She verified that her servers have this vulnerability, but this morning’s vulnerability scan report shows that the servers are secure. She contacted the vendor and determined that they have released a signature for this vulnerability and it is working properly at other clients. What action can Jacquelyn take that will most likely address the problem efficiently?
- Add the web servers to the scan.
- Reboot the vulnerability scanner.
- Update the vulnerability feed.
- Wait until tomorrow’s scan.
-
Dennis is developing a checklist that will be used by different security teams within his broad organization. What SCAP component can he use to help write the checklist and report results in a standardized fashion?
- XCCDF
- CCE
- CPE
- CVE
-
Vincent is a security manager for a U.S. federal government agency subject to FISMA. Which one of the following is not a requirement that he must follow for his vulnerability scans to maintain FISMA compliance?
- Run complete scans on at least a monthly basis.
- Use tools that facilitate interoperability and automation.
- Remediate legitimate vulnerabilities.
- Share information from the vulnerability scanning process.
-
Sharon is designing a new vulnerability scanning system for her organization. She must scan a network that contains hundreds of unmanaged hosts. Which of the following techniques would be most effective at detecting system configuration issues in her environment?
- Agent-based scanning
- Credentialed scanning
- Server-based scanning
- Passive network monitoring
Questions 182 through 184 refer to the following scenario:
Arlene ran a vulnerability scan of a VPN server used by contractors and employees to gain access to her organization’s network. An external scan of the server found the vulnerability shown here.

-
Which one of the following hash algorithms would not trigger this vulnerability?
- MD4
- MD5
- SHA-1
- SHA-256
-
What is the most likely result of failing to correct this vulnerability?
- All users will be able to access the site.
- All users will be able to access the site, but some may see an error message.
- Some users will be unable to access the site.
- All users will be unable to access the site.
-
How can Josh correct this vulnerability?
- Reconfigure the VPN server to only use secure hash functions.
- Request a new certificate.
- Change the domain name of the server.
- Implement an intrusion prevention system.
-
After reviewing the results of a vulnerability scan, Bruce discovered that many of the servers in his organization are susceptible to a brute-force SSH attack. He would like to determine what external hosts attempted SSH connections to his servers and is reviewing firewall logs. What TCP port would relevant traffic most likely use?
- 22
- 636
- 1433
- 1521
-
Terry runs a vulnerability scan of the network devices in his organization and sees the vulnerability report shown here for one of those devices. What action should he take?

- No action is necessary because this is an informational report.
- Upgrade the version of the certificate.
- Replace the certificate.
- Verify that the correct ciphers are being used.
-
Lori is studying vulnerability scanning as she prepares for the CySA+ exam. Which of the following is not one of the principles she should observe when preparing for the exam to avoid causing issues for her organization?
- Run only nondangerous scans on production systems to avoid disrupting a production service.
- Run scans in a quiet manner without alerting other IT staff to the scans or their results to minimize the impact of false information.
- Limit the bandwidth consumed by scans to avoid overwhelming an active network link.
- Run scans outside of periods of critical activity to avoid disrupting the business.
-
Meredith is configuring a vulnerability scan and would like to configure the scanner to perform credentialed scans. Of the menu options shown here, which will allow her to directly configure this capability?

- Manage Discovery Scans
- Configure Scan Settings
- Configure Search Lists
- Set Up Host Authentication
-
Norman is working with his manager to implement a vulnerability management program for his company. His manager tells him that he should focus on remediating critical and high-severity risks and that the organization does not want to spend time worrying about risks rated medium or lower. What type of criteria is Norman’s manager using to make this decision?
- Risk appetite
- False positive
- False negative
- Data classification
-
After running a vulnerability scan against his organization’s VPN server, Chis discovered the vulnerability shown here. What type of cryptographic situation does a birthday attack leverage?
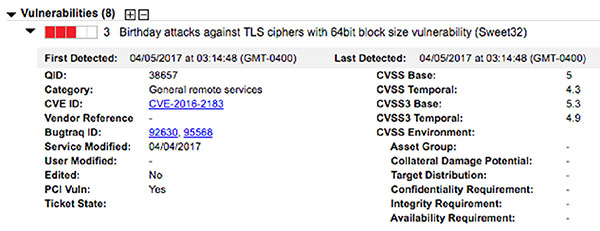
- Unsecured key
- Meet-in-the-middle
- Man-in-the-middle
- Collision
-
Meredith recently ran a vulnerability scan on her organization’s accounting network segment and found the vulnerability shown here on several workstations. What would be the most effective way for Meredith to resolve this vulnerability?

- Remove Flash Player from the workstations.
- Apply the security patches described in the Adobe bulletin.
- Configure the network firewall to block unsolicited inbound access to these workstations.
- Install an intrusion detection system on the network.
Questions 192 through 197 refer to the vulnerability shown here.

-
Based upon the information presented in the vulnerability report, what type of access must an attacker have to exploit this vulnerability?
- The attacker must have physical access to the system.
- The attacker must have logical access to the system.
- The attacker must have access to the local network that the system is connected to.
- The attacker can exploit this vulnerability remotely.
-
Based upon the information presented in the vulnerability report, how difficult would it be for an attacker to exploit this vulnerability?
- Exploiting this vulnerability requires specialized conditions that would be difficult to find.
- Exploiting this vulnerability requires somewhat specialized conditions.
- Exploiting this vulnerability does not require any specialized conditions.
- Exploiting this vulnerability is not possible without an administrator account.
-
Based upon the information presented in the vulnerability report, what authentication hurdles would an attacker need to clear to exploit this vulnerability?
- Attackers would need to authenticate two or more times.
- Attackers would need to authenticate once.
- Attackers would not need to authenticate.
- Attackers cannot exploit this vulnerability regardless of the number of authentications.
-
What level of confidentiality risk does this vulnerability pose to the organization?
- There is no confidentiality impact.
- Access to some information is possible, but the attacker does not have control over what information is compromised.
- Access to most information is possible, but the attacker does not have control over what information is compromised.
- All information on the system may be compromised.
-
What level of integrity risk does this vulnerability pose to the organization?
- There is no integrity impact.
- Modification of some information is possible, but the attacker does not have control over what information is modified.
- Modification of most information is possible, but the attacker does not have control over what information is modified.
- All information on the system may be modified.
-
What level of availability risk does this vulnerability pose to the organization?
- There is no availability impact.
- The performance of the system is degraded.
- One or more services on the system may be stopped.
- The system is completely shut down.
-
Dan is the vulnerability manager for his organization and is responsible for tracking vulnerability remediation. There is a critical vulnerability in a network device that Dan has handed off to the device’s administrator, but it has not been resolved after repeated reminders to the engineer. What should Dan do next?
- Threaten the engineer with disciplinary action.
- Correct the vulnerability himself.
- Mark the vulnerability as an exception.
- Escalate the issue to the network administrator’s manager.
-
Sara’s organization has a well-managed test environment. What is the most likely issue that Sara will face when attempting to evaluate the impact of a vulnerability remediation by first deploying it in the test environment?
- Test systems are not available for all production systems.
- Production systems require a different type of patch than test systems.
- Significant configuration differences exist between test and production systems.
- Test systems are running different operating systems than production systems.
-
How many vulnerabilities listed in the report shown here are significant enough to warrant immediate remediation in a typical operating environment?

- 22
- 14
- 5
- 0
-
Laura discovered an operating system vulnerability on a system on her network. After tracing the IP address, she discovered that the vulnerability is on a search appliance installed on her network. She consulted with the responsible engineer who informed her that he has no access to the underlying operating system. What is the best course of action for Laura?
- Contact the vendor to obtain a patch.
- Try to gain access to the underlying operating system and install the patch.
- Mark the vulnerability as a false positive.
- Wait 30 days and rerun the scan to see whether the vendor corrected the vulnerability.
-
Which one of the following types of data is subject to regulations in the United States that specify the minimum frequency of vulnerability scanning?
- Driver’s license numbers
- Insurance records
- Credit card data
- Medical records
-
Jim is responsible for managing his organization’s vulnerability scanning program. He is experiencing issues with scans aborting because the previous day’s scans are still running when the scanner attempts to start the current day’s scans. Which one of the following solutions is least likely to resolve Jim’s issue?
- Add a new scanner.
- Reduce the scope of the scans.
- Reduce the sensitivity of the scans.
- Reduce the frequency of the scans.
-
Trevor is working with an application team on the remediation of a critical SQL injection vulnerability in a public-facing service. The team is concerned that deploying the fix will require several hours of downtime and that will block customer transactions from completing. What is the most reasonable course of action for Trevor to suggest?
- Wait until the next scheduled maintenance window.
- Demand that the vulnerability be remediated immediately.
- Schedule an emergency maintenance for an off-peak time later in the day.
- Convene a working group to assess the situation.
-
While conducting a vulnerability scan of his organization’s data center, Renee discovers that the management interface for the organization’s virtualization platform is exposed to the scanner. In typical operating circumstances, what is the proper exposure for this interface?
- Internet
- Internal networks
- No exposure
- Management network
-
Richard is designing a remediation procedure for vulnerabilities discovered in his organization. He would like to make sure that any vendor patches are adequately tested prior to deploying them in production. What type of environment could Richard include in his procedure that would best address this issue?
- Sandbox
- Honeypot
- Honeynet
- Production
-
Becky is scheduling vulnerability scans for her organization’s data center. Which one of the following is a best practice that Becky should follow when scheduling scans?
- Schedule scans so that they are spread evenly throughout the day.
- Schedule scans so that they run during periods of low activity.
- Schedule scans so that they all begin at the same time.
- Schedule scans so that they run during periods of peak activity to simulate performance under load.
-
Given the CVSS information shown here, where would an attacker need to be positioned on the network to exploit this vulnerability?

- The attacker must have a local administrator account on the vulnerable system.
- The attacker must have a local account on the vulnerable system but does not necessarily require administrative access.
- The attacker must have access to the local network.
- The attacker may exploit this vulnerability remotely without an account on the system.