Chapter 11
Practice Test 3
-
Fred’s data role requires him to maintain system security plans and to ensure that system users and support staff get the training they need about security practices and acceptable use. What is the role that Fred is most likely to hold in the organization?
- Data owner
- System owner
- User
- Custodian
-
Sally is using IPsec’s ESP component in transport mode. What important information should she be aware of about transport mode?
- Transport mode provides full encryption of the entire IP packet.
- Transport mode adds a new, unencrypted header to ensure that packets reach their destination.
- Transport mode does not encrypt the header of the packet.
- Transport mode provides no encryption; only tunnel mode provides encryption.
-
Which one of the following is not a key process area for the Repeatable phase of the Software Capability Maturity Model (SW-CMM)?
- Software Project Planning
- Software Quality Management
- Software Project Tracking
- Software Subcontract Management
-
Ben wants to provide predictive information about his organization’s risk exposure in an automated way as part of an ongoing organizational risk management plan. What should he use to do this?
- KRIs
- Quantitative risk assessments
- KPIs
- Penetration tests
-
In the image shown here, what does system B send to system A at step 2 of the three-way TCP handshake?
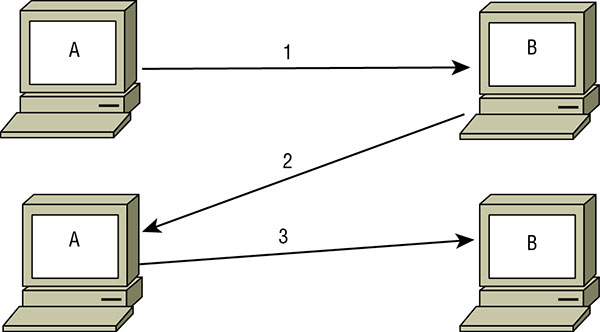
- SYN
- ACK
- FIN/ACK
- SYN/ACK
-
Chris is conducting reconnaissance on a remote target and discovers that pings are allowed through his target’s border firewall. What can he learn by using ping to probe the remote network?
- Which systems respond to ping, a rough network topology, and potentially the location of additional firewalls
- A list of all of the systems behind the target’s firewall
- The hostnames and time to live (TTL) for each pingable system, and the ICMP types allowed through the firewall
- Router advertisements, echo request responses, and potentially which hosts are tarpitted
-
What access management concept defines what rights or privileges a user has?
- Identification
- Accountability
- Authorization
- Authentication
-
Which one of the following is not a classification level commonly found in commercial data classification schemes?
- Secret
- Sensitive
- Confidential
- Public
-
Files, databases, computers, programs, processes, devices, and media are all examples of what?
- Subjects
- Objects
- File stores
- Users
-
Danielle is testing tax software, and part of her testing process requires her to input a variety of actual tax forms to verify that the software produces the right answers. What type of testing is Danielle performing?
- Use case testing
- Dynamic testing
- Fuzzing
- Misuse testing
-
After 10 years working in her organization, Cassandra is moving into her fourth role, this time as a manager in the accounting department. What issue is likely to show up during an account review if her organization does not have strong account maintenance practices?
- An issue with least privilege
- Privilege creep
- Account creep
- Account termination
-
IP addresses like 10.10.10.10 and 172.19.24.21 are both examples of what type of IP address?
- Public IP addresses
- Prohibited IP addresses
- Private IP addresses
- Class B IP ranges
-
What flaw is a concern with preset questions for cognitive passwords?
- It prevents the use of tokens.
- The question’s answer may be easy to find on the Internet.
- Cognitive passwords require users to think to answer the question, and not all users may be able to solve the problems presented.
- Cognitive passwords don’t support long passwords.
-
Megan needs to create a forensic copy of a hard drive that will be used in an investigation. Which of the following tools is best suited to her work?
- xcopy
- dd
- DBAN
- ImageMagik
-
Kay is selecting an application management approach for her organization. Employees need the flexibility to install software on their systems, but Kay wants to prevent them from installing certain prohibited packages. What type of approach should she use?
- Antivirus
- Whitelist
- Blacklist
- Heuristic
-
Data relating to the past, present, or future payment for the provision of healthcare to an individual is what type of data per HIPAA?
- PCI
- Personal billing data
- PHI
- Personally identifiable information (PII)
-
Yagis, panel, cantennas, and parabolic antennas are all examples of what type of antenna?
- Omnidirectional
- Rubber duck or base antenna
- Signal boosting
- Directional
-
While traveling, James is held at knifepoint and forced to log into his laptop. What is this called?
- Duress
- Antisocial engineering
- Distress
- Knifepoint hacking
-
What is the minimum number of people who should be trained on any specific business continuity plan implementation task?
- 1
- 2
- 3
- 5
-
Cameron is responsible for backing up his company’s primary file server. He configured a backup schedule that performs full backups every Monday evening at 9 p.m. and incremental backups on other days of the week at that same time. How many files will be copied in Wednesday’s backup?

- 1
- 2
- 5
- 6
-
Susan uses a span port to monitor traffic to her production website and uses a monitoring tool to identify performance issues in real time. What type of monitoring is she conducting?
- Passive monitoring
- Active monitoring
- Synthetic monitoring
- Signature-based monitoring
-
The type of access granted to an object and the actions that you can take on or with the object are examples of what?
- Permissions
- Rights
- Privileges
- Roles
-
Which one of the following would be considered an example of infrastructure as a service cloud computing?
- Payroll system managed by a vendor and delivered over the web
- Application platform managed by a vendor that runs customer code
- Servers provisioned by customers on a vendor-managed virtualization platform
- Web-based email service provided by a vendor
- For questions 24–26, please refer to the following scenario:
- Darcy is an information security risk analyst for Roscommon Agricultural Products. She is currently trying to decide whether the company should purchase an upgraded fire suppression system for their primary data center. The data center facility has a replacement cost of $2 million.
- After consulting with actuaries, data center managers, and fire subject matter experts, Darcy determined that a typical fire would likely require the replacement of all equipment inside the building but not cause significant structural damage. Together, they estimated that recovering from the fire would cost $750,000. They also determined that the company can expect a fire of this magnitude once every 50 years.
-
Based on the information in this scenario, what is the exposure factor for the effect of a fire on the Roscommon Agricultural Products data center?
- 7.5%
- 15.0%
- 27.5%
- 37.5%
-
Based on the information in this scenario, what is the annualized rate of occurrence for a fire at the Roscommon Agricultural Products data center?
- 0.002
- 0.005
- 0.02
- 0.05
-
Based on the information in this scenario, what is the annualized loss expectancy for a fire at the Roscommon Agricultural Products data center?
- $15,000
- $25,000
- $75,000
- $750,000
-
Two TCP header flags are rarely used. Which two are you unlikely to see in use in a modern network?
- CWR and ECE
- URG and FIN
- ECE and RST
- CWR and URG
-
Mike wants to ensure that third-party users of his service’s API can be tracked to prevent abuse of the API. What should he implement to help with this?
- Session IDs
- An API firewall
- API keys
- An API buffer
-
Fran is a web developer who works for an online retailer. Her boss asked her to create a way that customers can easily integrate themselves with Fran’s company’s site. They need to be able to check inventory in real time, place orders, and check order status programmatically without having to access the web page. What can Fran create to most directly facilitate this interaction?
- API
- Web scraper
- Data dictionary
- Call center
-
What type of power issue occurs when a facility experiences a momentary loss of power?
- Fault
- Blackout
- Sag
- Brownout
-
Lauren’s team of system administrators each deal with hundreds of systems with varying levels of security requirements and find it difficult to handle the multitude of usernames and passwords they each have. What type of solution should she recommend to ensure that passwords are properly handled and that features like logging and password rotation occur?
- A credential management system
- A strong password policy
- Separation of duties
- Single sign-on
-
Ed’s Windows system can’t connect to the network and ipconfig shows the following:

- What has occurred on the system?
- The system has been assigned an invalid IP address by its DHCP server.
- The system has a manually assigned IP address.
- The system has failed to get a DHCP address and has assigned itself an address.
- The subnet mask is set incorrectly and the system cannot communicate with the gateway.
-
What term is commonly used to describe initial creation of a user account in the provisioning process?
- Enrollment
- Clearance verification
- Background checks
- Initialization
-
What type of forensic investigation typically has the highest evidentiary standards?
- Administrative
- Criminal
- Civil
- Industry
-
There is a significant conflict between the drive for profit and the security requirements that Olivia’s organization has standardized. Olivia’s role means that decreased usability and loss of profit due to her staff’s inability to use the system is her major concern. What is the most likely role that Olivia plays in her organization?
- Business manager
- Information security analyst
- Data processor
- Mission owner
-
Tom believes that a customer of his Internet service provider has been exploiting a vulnerability in his system to read the email messages of other customers. If true, what law did the customer most likely violate?
- ECPA
- CALEA
- HITECH
- Privacy Act
-
In the ring protection model shown here, what ring contains user programs and applications?

- Ring 0
- Ring 1
- Ring 2
- Ring 3
-
Metrics like the attack vector, complexity, exploit maturity, and how much user interaction is required are all found in what scoring system?
- CVE
- CVSS
- CNA
- NVD
-
In which of the following circumstances does an individual not have a reasonable expectation of privacy?
- Placing a telephone call on your cell phone
- Sending a letter through the US mail
- Sending an email at work
- Retrieving your personal voicemail
-
During which of the following disaster recovery tests does the team sit together and discuss the response to a scenario but not actually activate any disaster recovery controls?
- Checklist review
- Full interruption test
- Parallel test
- Tabletop exercise
-
Susan wants to integrate her website to allow users to use accounts from sites like Google. What technology should she adopt?
- Kerberos
- LDAP
- OpenID
- SESAME
-
Tom is conducting a business continuity planning effort for Orange Blossoms, a fruit orchard located in Central Florida. During the assessment process, the committee determined that there is a small risk of snow in the region but that the cost of implementing controls to reduce the impact of that risk is not warranted. They elect to not take any specific action in response to the risk. What risk management strategy is Orange Blossoms pursuing?
- Risk mitigation
- Risk transference
- Risk avoidance
- Risk acceptance
-
Match each of the numbered cable types with exactly one of the lettered maximum cable lengths.
Cable type
- Category 5e
- Coaxial (RG-58)
- Fiber optic
Maximum length
- 500 feet
- 300 feet
- 1+ kilometers
-
Jack’s organization is a multinational nonprofit that has small offices in many developing countries throughout the world. They need to implement an access control system that allows flexibility and that can work despite poor Internet connectivity at their locations. What is the best type of access control design for Jack’s organization?
- Centralized access control
- Mandatory access control
- Decentralized access control
- Rule-based access control
-
What US government classification label is applied to information that, if disclosed, could cause serious damage to national security and also requires that the damage that would be caused is able to be described or identified by the classification authority?
- Classified
- Secret
- Confidential
- Top Secret
- For questions 46–49, please refer to the following scenario:
- Mike and Renee would like to use an asymmetric cryptosystem to communicate with each other. They are located in different parts of the country but have exchanged encryption keys by using digital certificates signed by a mutually trusted certificate authority.
-
When the certificate authority (CA) created Renee’s digital certificate, what key was contained within the body of the certificate?
- Renee’s public key
- Renee’s private key
- CA’s public key
- CA’s private key
-
When the certificate authority created Renee’s digital certificate, what key did it use to digitally sign the completed certificate?
- Renee’s public key
- Renee’s private key
- CA’s public key
- CA’s private key
-
When Mike receives Renee’s digital certificate, what key does he use to verify the authenticity of the certificate?
- Renee’s public key
- Renee’s private key
- CA’s public key
- CA’s private key
-
Mike would like to send Renee a private message using the information gained during this exchange. What key should he use to encrypt the message?
- Renee’s public key
- Renee’s private key
- CA’s public key
- CA’s private key
-
Which one of the following tools may be used to directly violate the confidentiality of communications on an unencrypted VoIP network?
- Nmap
- Nessus
- Wireshark
- Nikto
-
How does single sign-on increase security?
- It decreases the number of accounts required for a subject.
- It helps decrease the likelihood that users will write down their passwords.
- It provides logging for each system that it is connected to.
- It provides better encryption for authentication data.
-
Which one of the following cryptographic algorithms supports the goal of nonrepudiation?
- Blowfish
- DES
- AES
- RSA
-
Microsoft’s STRIDE threat assessment framework uses six categories for threats: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. If a penetration tester is able to modify audit logs, what STRIDE categories best describe this issue?
- Tampering and information disclosure
- Elevation of privilege and tampering
- Repudiation and denial of service
- Repudiation and tampering
-
RIP, OSPF, and BGP are all examples of protocols associated with what type of network device?
- Switches
- Bridges
- Routers
- Gateways
-
AES-based CCMP and 802.1x replaced what security protocol that was designed as part of WPA to help fix the significant security issues found in WEP?
- TLS
- TKIP
- EAP
- PEAP
-
The government agency that Ben works at installed a new access control system. The system uses information such as Ben’s identity, department, normal working hours, job category, and location to make authorization. What type of access control system did Ben’s employer adopt?
- Role-based access control
- Attribute-based access control
- Administrative access control
- System discretionary access control
-
The Low Orbit Ion Cannon (LOIC) attack tool used by Anonymous leverages a multitude of home PCs to attack its chosen targets. This is an example of what type of network attack?
- DDoS
- Ionization
- Zombie horde
- Teardrop
-
Andrew believes that a digital certificate belonging to his organization was compromised and would like to add it to a Certificate Revocation List. Who must add the certificate to the CRL?
- Andrew
- The root authority for the top-level domain
- The CA that issued the certificate
- The revocation authority for the top-level domain
-
Amanda is considering the implementation of a database recovery mechanism recommended by a consultant. In the recommended approach, an automated process will move records of transactions from the primary site to a backup site on an hourly basis. What type of database recovery technique is the consultant describing?
- Electronic vaulting
- Transaction logging
- Remote mirroring
- Remote journaling
-
A process on a system needs access to a file that is currently in use by another process. What state will the process scheduler place this process in until the file becomes available?
- Running
- Ready
- Waiting
- Stopped
-
Which one of the following investigation types has the loosest standards for the collection and preservation of information?
- Civil investigation
- Operational investigation
- Criminal investigation
- Regulatory investigation
-
Sue was required to sign an NDA when she took a job at her new company. Why did the company require her to sign it?
- To protect the confidentiality of their data
- To ensure that Sue did not delete their data
- To prevent Sue from directly competing with them in the future
- To require Sue to ensure the availability for their data as part of her job
-
Susan is concerned about the FAR associated with her biometric technology. What is the best method to deal with the FAR?
- Adjust the CER.
- Change the sensitivity of the system to lower the FRR.
- Add a second factor.
- Replace the biometric system.
-
Match the following numbered Service Organization Control (SOC) levels to their matching lettered SOC report descriptions:
SOC levels
- SOC 1, Type 1
- SOC 1, Type 2
- SOC 2
- SOC 3
SOC report descriptions
- A general use report that reports on controls related to compliance and/or operations
- A report that provides predefined, standard benchmarks for controls involving confidentiality, availability, integrity, and privacy of a system and the information it contains, generally for restricted use
- A report that provides an assessment of the risk of material misstatement of financial statement assertions affected by the service organization’s processing and that includes a description of the service auditor’s tests of the controls and the results of the tests and their effectiveness
- A report that provides the auditor’s opinions of financial statements about controls at the service organization and that includes a report on the opinion on the presentation of the service organization’s system as well as suitability of the controls
-
Which of the following is not a code review process?
- Email pass-around
- Over the shoulder
- Pair programming
- IDE forcing
-
Which one of the following attack types depends on precise timing?
- TOCTOU
- SQL injection
- Pass the hash
- Cross-site scripting
-
What process adds a header and a footer to data received at each layer of the OSI model?
- Attribution
- Encapsulation
- TCP wrapping
- Data hiding
-
Attackers who compromise websites often acquire databases of hashed passwords. What technique can best protect these passwords against automated password cracking attacks that use precomputed values?
- Using the MD5 hashing algorithm
- Using the SHA-1 hashing algorithm
- Salting
- Double-hashing
-
Jim starts a new job as a system engineer, and his boss provides him with a document entitled “Forensic Response Guidelines.” Which one of the following statements is not true?
- Jim must comply with the information in this document.
- The document contains information about forensic examinations.
- Jim should read the document thoroughly.
- The document is likely based on industry best practices.
-
Which one of the following tools is most often used for identification purposes and is not suitable for use as an authenticator?
- Password
- Retinal scan
- Username
- Token
-
Ben needs to verify that the most recent patch for his organization’s critical application did not introduce issues elsewhere. What type of testing does Ben need to conduct to ensure this?
- Unit testing
- White box
- Regression testing
- Black box
-
Tamara recently decided to purchase cyber-liability insurance to cover her company’s costs in the event of a data breach. What risk management strategy is she pursuing?
- Risk acceptance
- Risk mitigation
- Risk transference
- Risk avoidance
-
Which of the following is not one of the four canons of the (ISC)2 code of ethics?
- Avoid conflicts of interest that may jeopardize impartiality.
- Protect society, the common good, necessary public trust and confidence, and the infrastructure.
- Act honorably, honestly, justly, responsibly, and legally.
- Provide diligent and competent service to principals.
-
Jim wants to allow a partner organization’s Active Directory forest (B) to access his domain forest’s (A)’s resources but doesn’t want to allow users in his domain to access B’s resources. He also does not want the trust to flow upward through the domain tree as it is formed. What should he do?
- Set up a two-way transitive trust.
- Set up a one-way transitive trust.
- Set up a one-way nontransitive trust.
- Set up a two-way nontransitive trust.
-
Susan’s team is performing code analysis by manually reviewing the code for flaws. What type of analysis are they performing?
- Gray box
- Static
- Dynamic
- Fuzzing
-
The IP address 201.19.7.45 is what type of address?
- A public IP address
- An RFC 1918 address
- An APIPA address
- A loopback address
-
Sam is a security risk analyst for an insurance company. He is currently examining a scenario where a hacker might use a SQL injection attack to deface a web server due to a missing patch in the company’s web application. In this scenario, what is the vulnerability?
- Unpatched web application
- Web defacement
- Hacker
- Operating system
-
Which one of the following categories of secure data removal techniques would include degaussing?
- Clear
- Shrink
- Purge
- Destroy
-
What type of alternate processing facility includes all of the hardware and data necessary to restore operations in a matter of minutes or seconds?
- Hot site
- Warm site
- Cold site
- Mobile site
-
What UDP port is typically used by the syslog service?
- 443
- 514
- 515
- 445
-
Fred finds a packet that his protocol analyzer shows with both PSH and URG set. What type of packet is he looking at, and what do the flags mean?
- A UDP packet; PSH and URG are used to indicate that the data should be sent at high speed
- A TCP packet; PSH and URG are used to clear the buffer and indicate that the data is urgent
- A TCP packet; PSH and URG are used to preset the header and indicate that the speed of the network is unregulated
- A UDP packet; PSH and URG are used to indicate that the UDP buffer should be cleared and that the data is urgent
-
What code review process is shown here?

- Static inspection
- Fagan inspection
- Dynamic inspection
- Interface testing
-
During a log review, Karen discovers that the system she needs to gather logs from has the log setting shown here. What problem is Karen likely to encounter?

- Too much log data will be stored on the system.
- The system is automatically purging archived logs.
- The logs will not contain the information needed.
- The logs will only contain the most recent 20 MB of log data.
-
While investigating a widespread distributed denial of service attack, Matt types in the IP address of one of the attacking systems into his browser and sees the following page. What type of devices is the botnet likely composed of?

- SCADA
- Cloud infrastructure
- Web servers
- IoT
- For questions 85–87, please refer to the following scenario:
- Alejandro is an incident response analyst for a large corporation. He is on the midnight shift when an intrusion detection system alerts him to a potential brute-force password attack against one of the company’s critical information systems. He performs an initial triage of the event before taking any additional action.
-
What stage of the incident response process is Alejandro currently conducting?
- Detection
- Response
- Recovery
- Mitigation
-
If Alejandro’s initial investigation determines that a security incident is likely taking place, what should be his next step?
- Investigate the root cause.
- File a written report.
- Activate the incident response team.
- Attempt to restore the system to normal operations.
-
As the incident response progresses, during which stage should the team conduct a root cause analysis?
- Response
- Reporting
- Remediation
- Lessons Learned
-
Barry recently received a message from Melody that Melody encrypted using symmetric cryptography. What key should Barry use to decrypt the message?
- Barry’s public key
- Barry’s private key
- Melody’s public key
- Shared secret key
-
After you do automated functional testing with 100 percent coverage of an application, what type of error is most likely to remain?
- Business logic errors
- Input validation errors
- Runtime errors
- Error handling errors
-
During what phase of the incident response process would security professionals analyze the process itself to determine whether any improvements are warranted?
- Lessons Learned
- Remediation
- Recovery
- Reporting
-
What law prevents the removal of protection mechanisms placed on a copyrighted work by the copyright holder?
- HIPAA
- DMCA
- GLBA
- ECPA
-
Linda is selecting a disaster recovery facility for her organization, and she wishes to retain independence from other organizations as much as possible. She would like to choose a facility that balances cost and recovery time, allowing activation in about one week after a disaster is declared. What type of facility should she choose?
- Cold site
- Warm site
- Mutual assistance agreement
- Hot site
-
Purchasing insurance is a form of what type of risk response?
- Transfer
- Avoid
- Mitigate
- Accept
-
What type of penetration testing provides detail on the scope of a penetration test—including items like what systems would be targeted—but does not provide full visibility into the configuration or other details of the systems or networks the penetration tester must test?
- Crystal box
- White box
- Black box
- Gray box
-
Test coverage is computed using which of the following formulas?
- Number of use cases tested/total number of use cases
- Number of lines of code tested/total number of lines of code
- Number of functions tested/total number of functions
- Number of conditional branches tested/Total number of testable branches
-
TCP and UDP both operate at what layer of the OSI model?
- Layer 2
- Layer 3
- Layer 4
- Layer 5
-
Which one of the following goals of physical security environments occurs first in the functional order of controls?
- Delay
- Detection
- Deterrence
- Denial
-
In what type of trusted recovery process is the system able to recover without administrator intervention but the system may suffer some loss of data?
- Automated recovery
- Manual recovery
- Automated recovery without undue data loss
- Function recovery
-
Skip needs to transfer files from his PC to a remote server. What protocol should he use instead of FTP?
- SCP
- SSH
- HTTP
- Telnet
-
Ben’s New York–based commercial web service collects personal information from California residents. What does the California Online Privacy Protection Act require Ben to do to be compliant?
- Ben must encrypt all personal data he receives.
- Ben must comply with the EU GDPR.
- Ben must have a conspicuously posted privacy policy on his site.
- Ben must provide notice and choice for users of his website.
-
What process is used to verify that a dial-up user is connecting from the phone number they are preauthorized to use in a way that avoids spoofing?
- CallerID
- Callback
- CHAP
- PPP
-
‘The Meltdown bug announced in early 2018 exposed kernel data to user application space. What two rings are these referred to as for x86 PCs?
- Rings 0 and 1
- Rings 1 and 2
- Rings 1 and 3
- Rings 0 and 3
-
What advantage do iris scans have over most other types of biometric factors?
- Iris scanners are harder to deceive.
- Irises don’t change as much as other factors.
- Iris scanners are cheaper than other factors.
- Iris scans cannot be easily replicated.
-
Alex would like to ask all of his staff to sign an agreement that they will not share his organization’s intellectual property with unauthorized individuals. What type of agreement should Alex ask employees to sign?
- SLA
- NDA
- OLA
- DLP
-
Matthew, Richard, and Christopher would like to exchange messages with each other using symmetric cryptography. They want to ensure that each individual can privately send a message to another individual without the third person being able to read the message. How many keys do they need?
- 1
- 2
- 3
- 6
-
Which one of the following is not an example of criminal law?
- Gramm-Leach-Bliley Act
- Computer Fraud and Abuse Act
- Electronic Communications Privacy Act
- Identity Theft and Assumption Deterrence Act
-
What is the best way to ensure email confidentiality in motion?
- Use TLS between the client and server.
- Use SSL between the client and server.
- Encrypt the email content.
- Use a digital signature.
-
Brenda is analyzing the web server logs after a successful compromise of her organization’s web-based order processing application. She finds an entry in the log file showing that a user entered the following information as his last name when placing an order:
- Smith’;DROP TABLE orders;--
- What type of attack was attempted?
- Buffer overflow
- Cross-site scripting
- Cross-site request forgery
- SQL injection
-
What type of policy describes how long data is kept before destruction?
- Classification
- Audit
- Record retention
- Availability
-
What is the goal of the BCP process?
- RTO < MTD
- MTD < RTO
- RPO < MTD
- MTD < RPO
-
During which phase of the incident response process would administrators design new security controls intended to prevent a recurrence of the incident?
- Reporting
- Recovery
- Remediation
- Lessons Learned
-
Bethany received an email from one of her colleagues with an unusual attachment named smime.p7s. She does not recognize the attachment and is unsure what to do. What is the most likely scenario?
- This is an encrypted email message.
- This is a phishing attack.
- This is embedded malware.
- This is a spoofing attack.
- For questions 113–115, please refer to the following scenario:
- Kim is the database security administrator for Aircraft Systems, Inc. (ASI). ASI is a military contractor engaged in the design and analysis of aircraft avionics systems and regularly handles classified information on behalf of the government and other government contractors. Kim is concerned about ensuring the security of information stored in ASI databases.
- Kim’s database is a multilevel security database, and different ASI employees have different security clearances. The database contains information on the location of military aircraft containing ASI systems to allow ASI staff to monitor those systems.
-
Kim learned that the military is planning a classified mission that involves some ASI aircraft. She is concerned that employees not cleared for the mission may learn of it by noticing the movement of many aircraft to the region. Individual employees are cleared to know about the movement of an individual aircraft, but they are not cleared to know about the overall mission. What type of attack is Kim concerned about?
- Aggregation
- SQL injection
- Inference
- Multilevel security
-
What technique can Kim employ to prevent employees not cleared for the mission from learning the true location of the aircraft?
- Input validation
- Polyinstantiation
- Parameterization
- Server-side validation
-
Kim’s database uniquely identifies aircraft by using their tail number. Which one of the following terms would not necessarily accurately describe the tail number?
- Database field
- Foreign key
- Primary key
- Candidate key
-
Kim would like to create a key that enforces referential integrity for the database. What type of key does she need to create?
- Primary key
- Foreign key
- Candidate key
- Master key
-
Doug is choosing a software development life-cycle model for use in a project he is leading to develop a new business application. He has very clearly defined requirements and would like to choose an approach that places an early emphasis on developing comprehensive documentation. He does not have a need for the production of rapid prototypes or iterative improvement. Which model is most appropriate for this scenario?
- Agile
- Waterfall
- Spiral
- DevOps
-
Which individual bears the ultimate responsibility for data protection tasks?
- Data owner
- Data custodian
- User
- Auditor
-
What should be true for salts used in password hashes?
- A single salt should be set so passwords can be de-hashed as needed.
- A single salt should be used so the original salt can be used to check passwords against their hash.
- Unique salts should be stored for each user.
- Unique salts should be created every time a user logs in.
-
What type of assessment methods are associated with mechanisms and activities based on the recommendations of NIST SP800-53A, the Guide for Assessing Security Controls in Federal Information Systems?
- Examine and interview
- Test and assess
- Test and interview
- Examine and test
-
Which one of the following controls would be most effective in detecting zero-day attack attempts?
- Signature-based intrusion detection
- Anomaly-based intrusion detection
- Strong patch management
- Full-disk encryption
-
The ability to store and generate passwords, provide logging and auditing capabilities, and allow password check-in and check-out are all features of what type of system?
- AAA
- Credential management
- Two-factor authentication
- Kerberos
-
Which one of the following components should be included in an organization’s emergency response guidelines?
- Secondary response procedures for first responders
- Long-term business continuity protocols
- Activation procedures for the organization’s cold sites
- Contact information for ordering equipment
-
When Jim enters his organization’s data center, he has to use a smart card and code to enter and is allowed through one set of doors. The first set of doors closes, and he must then use his card again to get through a second set, which locks behind him. What type of control is this, and what is it called?
- A physical control; a one-way trapdoor
- A logical control; a dual-swipe authorization
- A directive control; a one-way access corridor
- A preventive access control; a mantrap
-
What security control may be used to implement a concept known as two-person control?
- Mandatory vacation
- Separation of duties
- Least privilege
- Defense in depth
