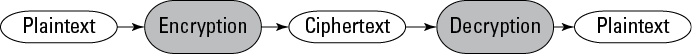
Figure 8-1: Encryption and decryption.
Cryptography Basics
Cryptography today has evolved into a complex science (some say an art) presenting many great promises and challenges in the field of information security. The basics of cryptography include various terms and concepts, the individual components of the cryptosystem, and the classes and types of ciphers.
Plaintext and ciphertext
A plaintext message is a message in its original readable format or a ciphertext message that has been properly decrypted (unscrambled) to produce the original readable plaintext message.
A ciphertext message is a plaintext message that has been transformed (encrypted) into a scrambled message that’s unintelligible. This term doesn’t apply to messages from your boss that may also happen to be unintelligible!
Encryption and decryption
Encryption (or enciphering) is the process of converting plaintext communications into ciphertext. Decryption (or deciphering) reverses that process, converting ciphertext into plaintext. (See Figure 8-1.)
Traffic on a network can be encrypted by using either end-to-end or link encryption.
End-to-end encryption
With end-to-end encryption, packets are encrypted once at the original encryption source and then decrypted only at the final decryption destination. The advantages of end-to-end encryption are its speed and overall security. However, in order for the packets to be properly routed, only the data is encrypted, not the routing information.
Link encryption
Link encryption requires that each node (for example, a router) has separate key pairs for its upstream and downstream neighbors. Packets are encrypted and decrypted, then re-encrypted at every node along the network path.
The following example in Lab 8-1 and Figure 8-2 illustrates link encryption:
Lab 8-1 Link Encryption
1. Computer 1 encrypts a message by using Secret Key A, and then transmits the message to Router 1.
2. Router 1 decrypts the message by using Secret Key A, re-encrypts the message by using Secret Key B, and then transmits the message to Router 2.
3. Router 2 decrypts the message by using Secret Key B, re-encrypts the message by using Secret Key C, and then transmits the message to Computer 2.
4. Computer 2 decrypts the message by using Secret Key C.
Figure 8-2: Link encryption.

The advantage of using link encryption is that the entire packet (including routing information) is encrypted. However, link encryption has the following two disadvantages:
![]() Latency: Packets must be encrypted/decrypted at every node, which creates latency (delay) in the transmission of those packets.
Latency: Packets must be encrypted/decrypted at every node, which creates latency (delay) in the transmission of those packets.
![]() Inherent vulnerability: If a node is compromised or a packet’s decrypted contents are cached in a node, the message can be compromised.
Inherent vulnerability: If a node is compromised or a packet’s decrypted contents are cached in a node, the message can be compromised.
Putting it all together: The cryptosystem
A cryptosystem is the hardware or software implementation that transforms plaintext into ciphertext (encrypting it) and back into plaintext (decrypting it).
An effective cryptosystem must have the following properties:
![]() The encryption and decryption process is efficient for all possible keys within the cryptosystem’s keyspace.
The encryption and decryption process is efficient for all possible keys within the cryptosystem’s keyspace.
 A keyspace is the range of all possible values for a key in a cryptosystem.
A keyspace is the range of all possible values for a key in a cryptosystem.
![]() The cryptosystem is easy to use.
The cryptosystem is easy to use.
![]() The strength of the cryptosystem depends on the secrecy of the cryptovariables (or keys), rather than the secrecy of the algorithm.
The strength of the cryptosystem depends on the secrecy of the cryptovariables (or keys), rather than the secrecy of the algorithm.
Cryptosystems are typically composed of two basic elements:
![]() Cryptographic algorithm: Also called a cipher, the cryptographic algorithm details the step-by-step mathematical function used to produce
Cryptographic algorithm: Also called a cipher, the cryptographic algorithm details the step-by-step mathematical function used to produce
• Ciphertext (encipher)
• Plaintext (decipher)
![]() Cryptovariable: Also called a key, the cryptovariable is a secret value applied to the algorithm. The strength and effectiveness of the cryptosystem largely depend on the secrecy and strength of the cryptovariable.
Cryptovariable: Also called a key, the cryptovariable is a secret value applied to the algorithm. The strength and effectiveness of the cryptosystem largely depend on the secrecy and strength of the cryptovariable.
Key clustering (or simply clustering) occurs when identical ciphertext messages are generated from a plaintext message by using the same encryption algorithm but different encryption keys. Key clustering indicates a weakness in a cryptographic algorithm because it statistically reduces the number of key combinations that must be attempted in a brute force attack.
Classes of ciphers
Ciphers are cryptographic transformations. The two main classes of ciphers used in symmetric key algorithms are block and stream (see the section “Not Quite the Metric System: Symmetric and Asymmetric Key Systems,” later in this chapter), which describe how the ciphers operate on input data.
Block ciphers
Block ciphers operate on a single fixed block (typically 64 bits) of plaintext to produce the corresponding ciphertext. Using a given key in a block cipher, the same plaintext block always produces the same ciphertext block. Advantages of block ciphers compared with stream ciphers are
![]() Reusable keys: Key management is much easier.
Reusable keys: Key management is much easier.
![]() Interoperability: Block ciphers are more widely supported.
Interoperability: Block ciphers are more widely supported.
Block ciphers are typically implemented in software.
Stream ciphers
Stream ciphers operate in real time on a continuous stream of data, typically bit by bit. Stream ciphers generally work faster than block ciphers and require less code to implement. However, the keys in a stream cipher are generally used only once (see the sidebar “A disposable cipher: The one-time pad”) and then discarded. Key management becomes a serious problem. Using a stream cipher, the same plaintext bit or byte will produce a different ciphertext bit or byte every time it is encrypted. Stream ciphers are typically implemented in hardware.
Types of ciphers
The two basic types of ciphers are substitution and transposition. Both are involved in the process of transforming plaintext into ciphertext.
Substitution ciphers
Substitution ciphers replace bits, characters, or character blocks in plaintext with alternate bits, characters, or character blocks to produce ciphertext. A classic example of a substitution cipher is one that Julius Caesar used: He substituted letters of the message with other letters from the same alphabet. (Read more about this in the sidebar “Tales from the crypt-o: A brief history of cryptography,” earlier in this chapter.) In a simple substitution cipher using the standard English alphabet, a cryptovariable (key) is added modulo 26 to the plaintext message. In modulo 26 addition, the remainder is the final result for any sum equal to or greater than 26. For example, a basic substitution cipher in which the word BOY is encrypted by adding three characters using modulo 26 math produces the following result:
|
B |
O |
Y |
PLAINTEXT |
|
|
2 |
15 |
25 |
NUMERIC VALUE |
|
|
+ |
3 |
3 |
3 |
SUBSTITUTION VALUE |
|
5 |
18 |
2 |
MODULO 26 RESULT |
|
|
E |
R |
B |
CIPHERTEXT |
A substitution cipher may be monoalphabetic or polyalphabetic:
![]() Monoalphabetic: A single alphabet is used to encrypt the entire plaintext message.
Monoalphabetic: A single alphabet is used to encrypt the entire plaintext message.
![]() Polyalphabetic: A more complex substitution that uses a different alphabet to encrypt each bit, character, or character block of a plaintext message.
Polyalphabetic: A more complex substitution that uses a different alphabet to encrypt each bit, character, or character block of a plaintext message.
A more modern example of a substitution cipher is the S-boxes (Substitution boxes) employed in the Data Encryption Standard (DES) algorithm. The S-boxes in DES produce a nonlinear substitution (6 bits in, 4 bits out). Note: Do not attempt to sing this to the tune “Shave and a Haircut” to improve the strength of the encryption by hiding any statistical relationship between the plaintext and ciphertext characters.
Transposition (or permutation) ciphers
Transposition ciphers rearrange bits, characters, or character blocks in plaintext to produce ciphertext. In a simple columnar transposition cipher, a message might be read horizontally but written vertically to produce the ciphertext as in the following example:
THE QUICK BROWN FOX JUMPS OVER THE LAZY DOG
written in 9 columns as
THEQUICKB
ROWNFOXJU
MPSOVERTH
ELAZYDOG
then transposed (encrypted) vertically as
TRMEHOPLEWSAQNOZUFVYIOEDCXROKJTGBUH
The original letters of the plaintext message are the same; only the order has been changed to achieve encryption.
DES performs permutations through the use of P-boxes (Permutation boxes) to spread the influence of a plaintext character over many characters so that they’re not easily traced back to the S-boxes used in the substitution cipher.
Other types of ciphers include
![]() Codes: Includes words and phrases to communicate a secret message.
Codes: Includes words and phrases to communicate a secret message.
![]() Running (or book) ciphers: For example, the key is page 137 of The Catcher in the Rye, and text on that page is added modulo 26 to perform encryption/decryption.
Running (or book) ciphers: For example, the key is page 137 of The Catcher in the Rye, and text on that page is added modulo 26 to perform encryption/decryption.
![]() Vernam ciphers: Also known as one-time pads, which are keystreams that can be used only once. We discuss these more in the earlier sidebar “A disposable cipher: The one-time pad.”
Vernam ciphers: Also known as one-time pads, which are keystreams that can be used only once. We discuss these more in the earlier sidebar “A disposable cipher: The one-time pad.”
![]() Concealment ciphers: These ciphers include steganography, which we discuss in the section “Steganography: A picture is worth a thousand (hidden) words,” later in this chapter.
Concealment ciphers: These ciphers include steganography, which we discuss in the section “Steganography: A picture is worth a thousand (hidden) words,” later in this chapter.

 An analogy of a cryptosystem is a deadbolt lock. A deadbolt lock can be easily identified, and its inner working mechanisms aren’t closely guarded state secrets. What makes a deadbolt lock effective is the individual key that controls a specific lock on a specific door. However, if the key is weak (imagine only one or two notches on a flat key) or not well protected (left under your doormat), the lock won’t protect your belongings. Similarly, if an attacker is able to determine what cryptographic algorithm (lock) was used to encrypt a message, it should still be protected because you’re using a strong key (128-bit) that you’ve kept secret, rather than a six-character password that you wrote on a scrap of paper and left under your mouse pad.
An analogy of a cryptosystem is a deadbolt lock. A deadbolt lock can be easily identified, and its inner working mechanisms aren’t closely guarded state secrets. What makes a deadbolt lock effective is the individual key that controls a specific lock on a specific door. However, if the key is weak (imagine only one or two notches on a flat key) or not well protected (left under your doormat), the lock won’t protect your belongings. Similarly, if an attacker is able to determine what cryptographic algorithm (lock) was used to encrypt a message, it should still be protected because you’re using a strong key (128-bit) that you’ve kept secret, rather than a six-character password that you wrote on a scrap of paper and left under your mouse pad.