One thing I have often seen is badly stored passwords. Just because the password is stored in a database on your server, does not make it secure. So what do badly stored passwords look like?

Secure passwords stored badly are no longer secure. The passwords in the previous screenshot are the actual user passwords. Entering the first password, ^tj_Y4$g1!8LkD at the login screen will give the user access to the system. Passwords should be stored securely in the database. In fact, you need to employ salted password hashing. You should be able to encrypt the user's password, but never decrypt it.
So how do you decrypt the password to match it to the password the user enters at the login screen? Well, you don't. You always hash the password the user enters at the login screen. If it matches the hash of their real password stored in the database, you give them access to the system.
The SQL tables in this recipe are for illustration only and are not written to by the code in the recipe. The database can be found in the _database scripts folder that accompanies the source code for this book.
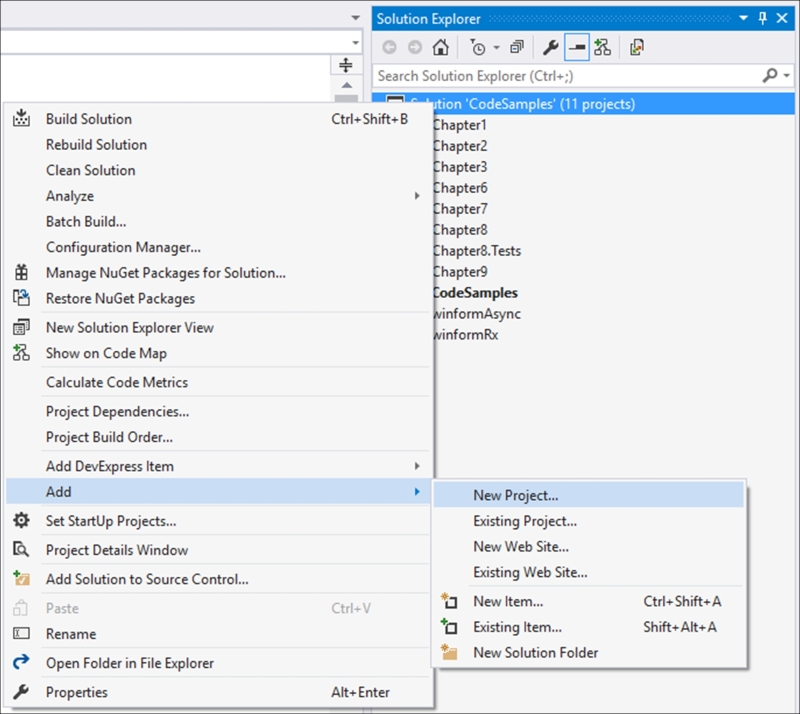
- Create a new class library by right-clicking on your solution, and selecting Add and then New Project from the context menu:
- From the Add New Project dialog screen, select Class Library from the installed templates and call your class
Chapter12: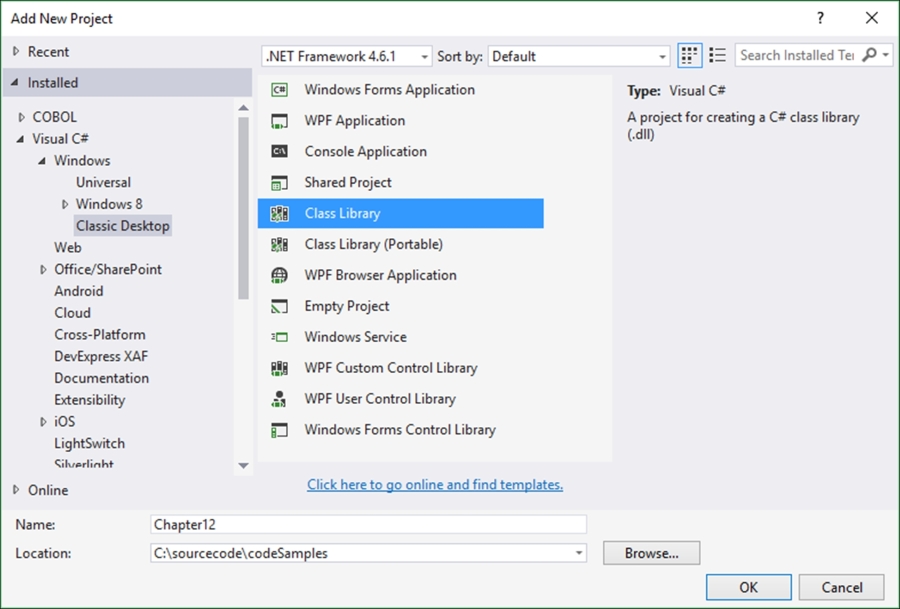
- Your new class library will be added to your solution with a default name of
Class1.cs, which we renamedRecipes.csin order to distinguish the code properly. You can, however, rename your class whatever you like if that makes more sense to you. - To rename your class, simply click on the class name in the Solution Explorer and select Rename from the context menu:

- Visual Studio will ask you to confirm a rename of all references to the code element Class1 in the project. Just click Yes:

- The following class is added to your
Chapter12library project:namespace Chapter12 { public class Recipes { } } - Add the following
usingstatement to your class:using System.Security.Cryptography;
- Next, you need to add two properties to the class. These properties will store the salt and the hash. Usually you will write these values to the database along with the username, but for the purposes of this recipe we will simply add them to the static properties. Also add two methods to the class called
RegisterUser()andValidateLogin(). Both methods take as parameters theusernameandpasswordvariables:public static class Recipes { public static string saltValue { get; set; } public static string hashValue { get; set; } public static void RegisterUser(string password, string username) { } public static void ValidateLogin(string password, string username) { } } - Starting with the
RegisterUser()method, here we do a number of things. To list the steps in the method:- We generate a truly random, cryptographically strong salt value using
RNGCryptoServiceProvider - Add the salt to the password and hash the salted password using
SHA256. - Store the salt value and the hash value along with the username in the database.
This is a very secure way to handle user passwords in your application:
public static void RegisterUser(string password, string username) { // Create a truly random salt using RNGCryptoServiceProvider. RNGCryptoServiceProvider csprng = new RNGCryptoServiceProvider(); byte[] salt = new byte[32]; csprng.GetBytes(salt); // Get the salt value saltValue = Convert.ToBase64String(salt); // Salt the password byte[] saltedPassword = Encoding.UTF8.GetBytes(saltValue + password); // Hash the salted password using SHA256 SHA256Managed hashstring = new SHA256Managed(); byte[] hash = hashstring.ComputeHash(saltedPassword); // Save both the salt and the hash in the user's database record. saltValue = Convert.ToBase64String(salt); hashValue = Convert.ToBase64String(hash); }
- We generate a truly random, cryptographically strong salt value using
- The next method we need to create is the
ValidateLogin()method. Here we take the username and validate that first. If the user entered the username incorrectly, do not tell them so. This would alert someone trying to compromise the system that they have the wrong username and that as soon as they get a wrong password notification, they know that the username is correct. The steps in this method are as follows:- Get the salt and hash values for the entered username from the database.
- Salt the password the user entered at the login screen with the salt read from the database.
- Hash the salted password using the same hashing algorithm as when the user registered.
- Compare the hash value read from the database to the hash value generated in the method. If the two hashes match, then the password is correctly entered and the user validated.
Note that we never decrypt the password from the database. If you have code decrypting user passwords and matching that to the password entered, you need to reconsider and rewrite your password logic. A system should never be able to decrypt user passwords.
public static void ValidateLogin(string password, string username) { // Read the user's salt value from the database string saltValueFromDB = saltValue; // Read the user's hash value from the database string hashValueFromDB = hashValue; byte[] saltedPassword = Encoding.UTF8.GetBytes(saltValueFromDB + password); // Hash the salted password using SHA256 SHA256Managed hashstring = new SHA256Managed(); byte[] hash = hashstring.ComputeHash(saltedPassword); string hashToCompare = Convert.ToBase64String(hash); if (hashValueFromDB.Equals(hashToCompare)) Console.WriteLine("User Validated."); else Console.WriteLine("Login credentials incorrect. User not validated."); }
- To test the code, add a reference to the
Chapter12class in yourCodeSamplesproject:
- Because we created a static class, you can add the new
using staticto yourProgram.csfile:using static Chapter12.Recipes;
- Test the code by calling the
RegisterUser()method and pass it theusernameandpasswordvariable. After that, call theValidateLogin()method and see whether the password matches the hash. This would obviously not happen at the same time in a real production system:string username = "dirk.strauss"; string password = "^tj_Y4$g1!8LkD"; RegisterUser(password, username); ValidateLogin(password, username); Console.ReadLine();
- When you debug the code, you will see the user has been validated:

- Lastly, modify the code slightly and set the
passwordvariable to something else. This will mimic a user entering an incorrect password:string username = "dirk.strauss"; string password = "^tj_Y4$g1!8LkD"; RegisterUser(password, username); password = "WrongPassword"; ValidateLogin(password, username); Console.ReadLine();
- When you debug the application, you will see that the user is not validated:

Nowhere in the code did we decrypt the password. In fact, the password is never stored anywhere. We always worked with the hash of the password. Here are the important points to take away from this recipe:
- Never use the
Randomclass in C# to generate your salt. Always use theRNGCryptoServiceProviderclass. - Never re-use the same salt in your code. So don't create a constant with your salt and use it to salt all the passwords in your system.
- Never tell the user that the password is incorrect if the password didn't match. Also, never tell the user that they entered an incorrect username. This prevents someone trying to compromise the system from knowing that they got one of the two login credentials correct. If either the username or password has been entered incorrectly, rather notify the user that their login credentials are incorrect. This could mean that either the username or password (or both) have been entered incorrectly.
- You can't get the passwords from the hash or salt stored in the database. Therefore, if the database was compromised, the password data stored within it would not be at risk. The encryption of the user's password is a one-way operation, meaning that it can never be decrypted. Also important to note is that even if the source code was compromised and stolen by someone with malicious intent, you would not be able to use the code to decipher the encrypted data in the database.
- Combine the previous methods with a strong password policy (because even in 2016, there are still users that think using
'l3tm31n'for a password is good enough), and you have a very good password encryption routine.
When we look at the user access table, the correct way to store user credentials would look something like this:

The salt and hash are stored alongside the username, and are secure because they can't be decrypted to expose the actual password.
Tip
If you sign up for a service on the Internet and they send you a confirmation either via email or text message and display your password in this message in plain text, then you should seriously consider closing your account. If a system can read your password and send it to you in plain text, then so can anybody else. Never use the same password for all your logins.
