- CISSP in 21 Days Second Edition
- CISSP in 21 Days Second Edition
- Credits
- About the Author
- About the Reviewer
- www.PacktPub.com
- Preface
- 1. Day 1 – Security and Risk Management - Security, Compliance, and Policies
- 2. Day 2 – Security and Risk Management - Risk Management, Business Continuity, and Security Education
- 3. Day 3 – Asset Security - Information and Asset Classification
- 4. Day 4 – Asset Security - Data Security Controls and Handling
- 5. Day 5 – Exam Cram and Practice Questions
- 6. Day 6 – Security Engineering - Security Design, Practices, Models, and Vulnerability Mitigation
- 7. Day 7 – Security Engineering - Cryptography
- 8. Day 8 – Communication and Network Security - Network Security
- An overview of communication and network security
- Network architecture, protocols, and technologies
- Open System Interconnect (OSI) model
- OSI layers and security
- Application layer protocols and security
- Presentation layer protocols and security
- Summary
- Sample questions
- 9. Day 9 – Communication and Network Security - Communication Security
- An overview of communication security
- Security in communication channels
- Attacks on communication networks
- Preventing or mitigating communication network attacks
- Summary
- Sample questions
- 10. Day 10 – Exam Cram and Practice Questions
- 11. Day 11 – Identity and Access Management - Identity Management
- 12. Day 12 – Identity and Access Management - Access Management, Provisioning, and Attacks
- 13. Day 13 – Security Assessment and Testing - Designing, Performing Security Assessment, and Tests
- An overview of security assessment and testing
- Security assessment and test strategies
- Security controls
- Summary
- Sample questions
- 14. Day 14 – Security Assessment and Testing - Controlling, Analyzing, Auditing, and Reporting
- 15. Day 15 – Exam Cram and Practice Questions
- 16. Day 16 – Security Operations - Foundational Concepts
- An overview of operations security
- The physical security design
- Physical and operations security controls
- Operations/facility security
- Protecting and securing equipment
- Computer investigations
- Summary
- Sample questions
- 17. Day 17 – Security Operations - Incident Management and Disaster Recovery
- 18. Day 18 – Software Development Security - Security in Software Development Life Cycle
- 19. Day 19 – Software Development Security - Assessing effectiveness of Software Security
- 20. Day 20 – Exam Cram and Practice Questions
- 21. Day 21 – Exam Cram and Mock Test
Q1. Which one of the following is not an Identity and Access Management (IAM) process?
- Authorization
- Accountability
- Identification
- Allocation
Q2. A user is trying to access an application. During the process, the user fills in a user name and password, and he submits the same to the application. Which one of the following represents such an activity?
- Identification
- Authentication
- Authorization
- Accountability
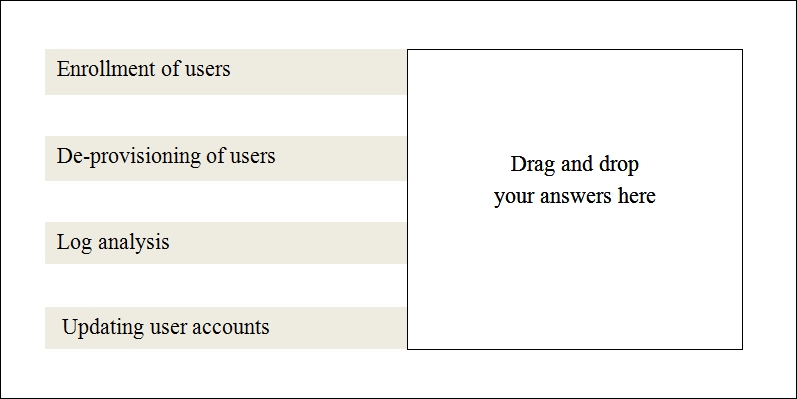
Q3. Which statements, among the following, are a part of the Identity and Access Management facilitation process (this is a drag and drop type of question. Here you can draw a line from the list of answers from the left to the empty box on the right)?
Q4. Identity theft is what?
- Stealing one's money
- Stealing one's property
- Stealing one's credentials
- Stealing one's computer
Q5. The following statements pertaining to Single Sign On (SSO) are true except.
- SSO is an accountability mechanism to monitor user logon activities
- SSO is an access control mechanism that allows multiple web resource access with a single credential
- SSO works on the access layer
- SSO allows one authentication and multiple authorizations
Q6. Identity federation-related services and terminologies from the following list (this is a drag-and-drop type of question. Here, you can draw a line from the list of answers from the left to the empty box on the right).

Q7. Listening to communications surreptitiously between a client and a server is called what?
- Eavestailing
- Eavesdropping
- Tailgating
- Forgery
Q8. The Triple A of access control consists of what?
- Identification, Authentication and Authorization
- Identification, Authentication and Accountability
- Identification, Authorization and Authorization
- Authentication, Authorization and Accountability
-
No Comment
