 3. Day 3 – Asset Security - Information and Asset Classification
by M. L. Srinivasan
CISSP in 21 Days - Second Edition
3. Day 3 – Asset Security - Information and Asset Classification
by M. L. Srinivasan
CISSP in 21 Days - Second Edition
- CISSP in 21 Days Second Edition
- CISSP in 21 Days Second Edition
- Credits
- About the Author
- About the Reviewer
- www.PacktPub.com
- Preface
- 1. Day 1 – Security and Risk Management - Security, Compliance, and Policies
- 2. Day 2 – Security and Risk Management - Risk Management, Business Continuity, and Security Education
- 3. Day 3 – Asset Security - Information and Asset Classification
- 4. Day 4 – Asset Security - Data Security Controls and Handling
- 5. Day 5 – Exam Cram and Practice Questions
- 6. Day 6 – Security Engineering - Security Design, Practices, Models, and Vulnerability Mitigation
- 7. Day 7 – Security Engineering - Cryptography
- 8. Day 8 – Communication and Network Security - Network Security
- An overview of communication and network security
- Network architecture, protocols, and technologies
- Open System Interconnect (OSI) model
- OSI layers and security
- Application layer protocols and security
- Presentation layer protocols and security
- Summary
- Sample questions
- 9. Day 9 – Communication and Network Security - Communication Security
- An overview of communication security
- Security in communication channels
- Attacks on communication networks
- Preventing or mitigating communication network attacks
- Summary
- Sample questions
- 10. Day 10 – Exam Cram and Practice Questions
- 11. Day 11 – Identity and Access Management - Identity Management
- 12. Day 12 – Identity and Access Management - Access Management, Provisioning, and Attacks
- 13. Day 13 – Security Assessment and Testing - Designing, Performing Security Assessment, and Tests
- An overview of security assessment and testing
- Security assessment and test strategies
- Security controls
- Summary
- Sample questions
- 14. Day 14 – Security Assessment and Testing - Controlling, Analyzing, Auditing, and Reporting
- 15. Day 15 – Exam Cram and Practice Questions
- 16. Day 16 – Security Operations - Foundational Concepts
- An overview of operations security
- The physical security design
- Physical and operations security controls
- Operations/facility security
- Protecting and securing equipment
- Computer investigations
- Summary
- Sample questions
- 17. Day 17 – Security Operations - Incident Management and Disaster Recovery
- 18. Day 18 – Software Development Security - Security in Software Development Life Cycle
- 19. Day 19 – Software Development Security - Assessing effectiveness of Software Security
- 20. Day 20 – Exam Cram and Practice Questions
- 21. Day 21 – Exam Cram and Mock Test
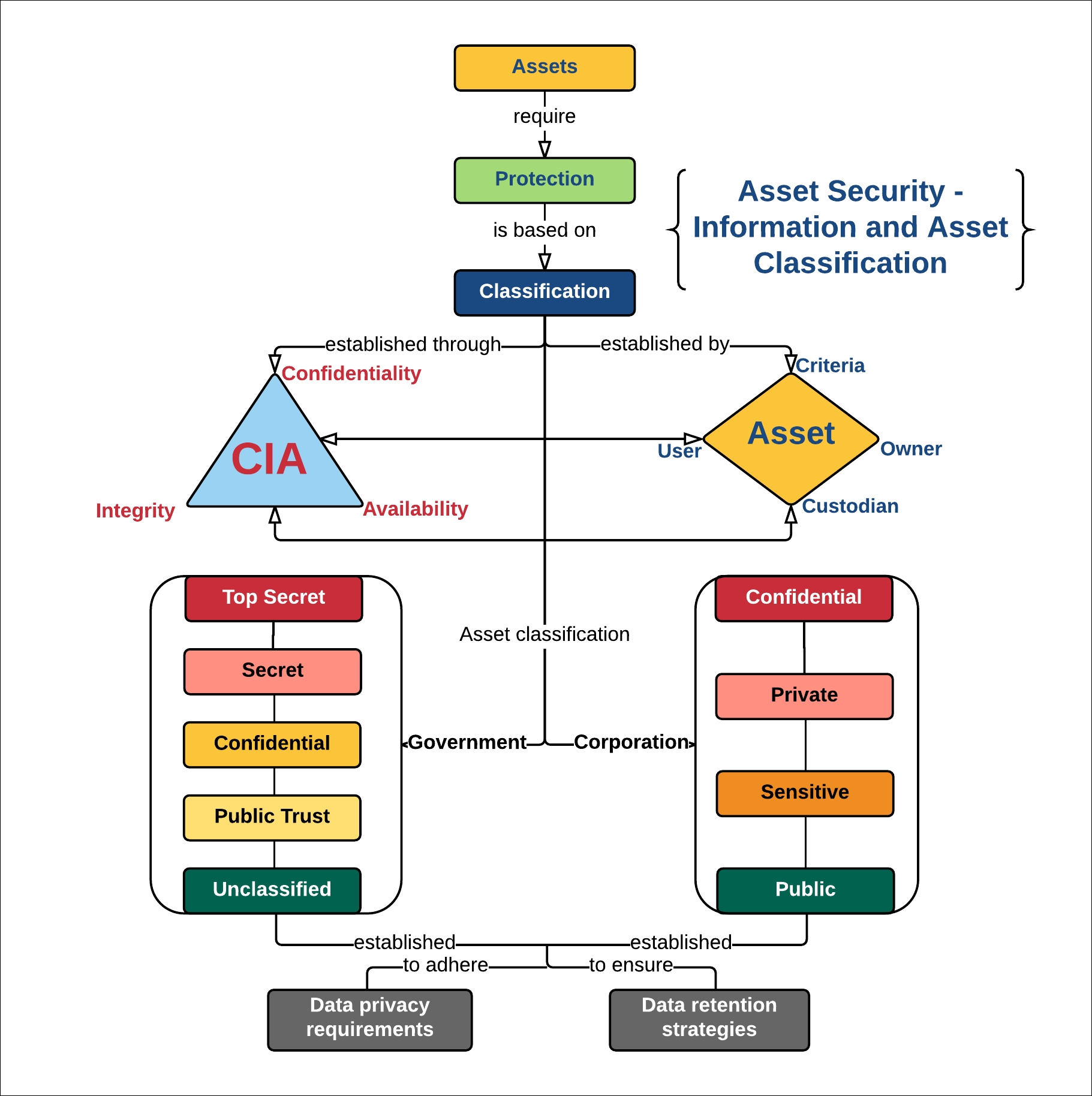
Information security is the preservation of confidentiality and integrity and the availability of assets. Assets have intrinsic value to the business and are classified into various types. The type of asset and its value are used to determine the required level of security assurance.
This chapter provides an overview of asset security. The concepts and techniques that pertain to information assets are covered in detail throughout this chapter. Data security concepts and controls are also covered in detail using suitable illustration and examples.
This chapter covers the following:
- Overview of asset security
- Overview of information and asset classification
- Asset ownership
- Classification types in government
- Classification types in corporations
- Overview of data privacy
- Overview of data retention strategies
Asset protection forms the baseline for security. Unintended disclosure, unauthorized modification, or destruction of an asset can affect security. In other words, confidentiality, integrity, and/or availability requirements will be affected.
As covered in Chapter 1, Day 1 – Security and Risk Management - Security, Compliance, and Policies, assets are grouped based on their type, such as physical, hardware, information, and so on. Similarly, assets are further classified based on their value and sensitivity. Value can be monetary or based on other qualitative factors, such as loss in terms of people, property, or image. Sensitivity is based on confidentiality factors and the effect of disclosure to national security. For corporations, sensitivity is based on the extent of the loss of corporate image.
Observe the following illustration:
-
No Comment